云的安全是一个重要的问题,很多企业不上云的原因就认为云不安全,特别是对安全性要求较高的企业,所以云安全是一个非常广泛且重要的话题,其实在之前章节中的组件都会或多或少讲述与其相关的安全问题,这里也会详细讲一下。本章主要通过讲述一些独立或与安全有关的组件以及网络安全等方面,简单说一下AWS上关于SAP-C02考试的内容。
目录
1 AWS CloudTrail
AWS CloudTrail 是一项 AWS 服务,可帮助您对 AWS 账户进行操作和风险审核、监管和合规性检查。用户、角色或 AWS 服务执行的操作将记录为 CloudTrail 中的事件。事件包括在 AWS Management Console、AWS Command Line Interface 和 AWS 开发工具包和 API 中执行的操作。简单来说,CloudTrail就是可以对用户在AWS上的行为进行采集、存储、操作和审查等,之所以将其放在安全部分,是因为对行为的监控是安全的第一步。
1.1 基本特性
- 包括: management events(管理事件)、data events(数据事件)、Insights events(见解事件)
- 可以将日志存入CloudWatch Logs中
- 可以和不同服务集成做更多事情:https://docs.aws.amazon.com/zh_cn/awscloudtrail/latest/userguide/cloudtrail-aws-service-specific-topics.html
- 控制台可以查看过去90天内容
- 默认包括创建、修改和删除事件,也可以自定义内容展示
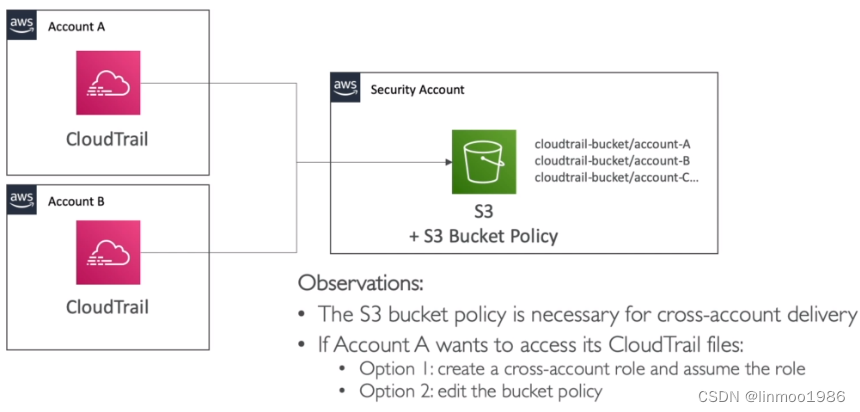
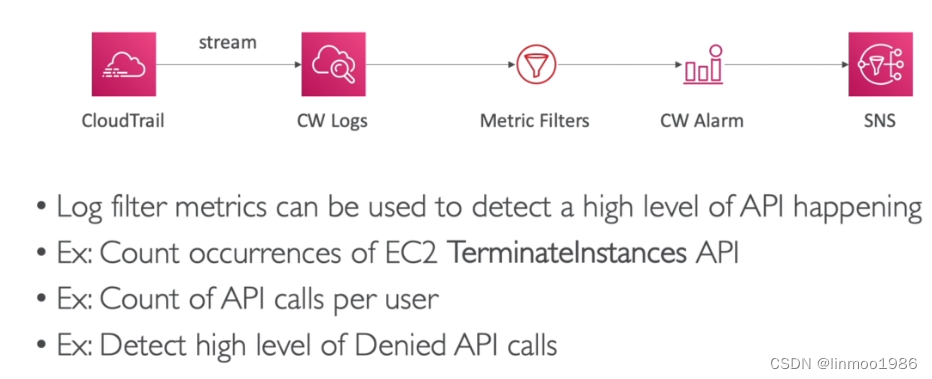
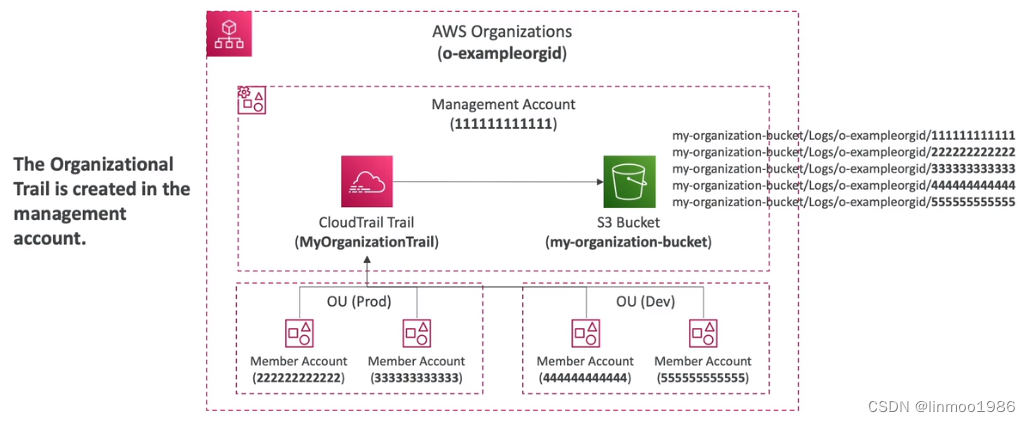
1.2 典型架构
- 日志的处理架构
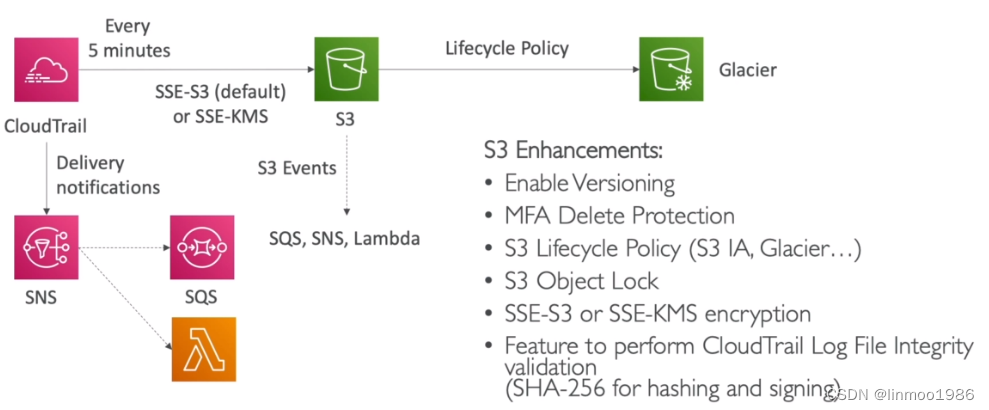
- 多账号多区域统一日志管理
- 通过日志采集设置报警架构
- Organization下统一日志管理
1.3 方案比较
日志采集后存储及处理,会有不同方案,不同的方案有不同的应用场景,下列给出不同方案,可供不同场景使用:
方案解决问题CloudWatch Event能够在CloudTrail触发API调用,是目前延迟最小的监控CloudWatch Logs以流式将日志过滤并可以设置警告通知S3将日志存储在S3,可以长期保持并且结合如Athena工具进行检索
2 AWS KMS
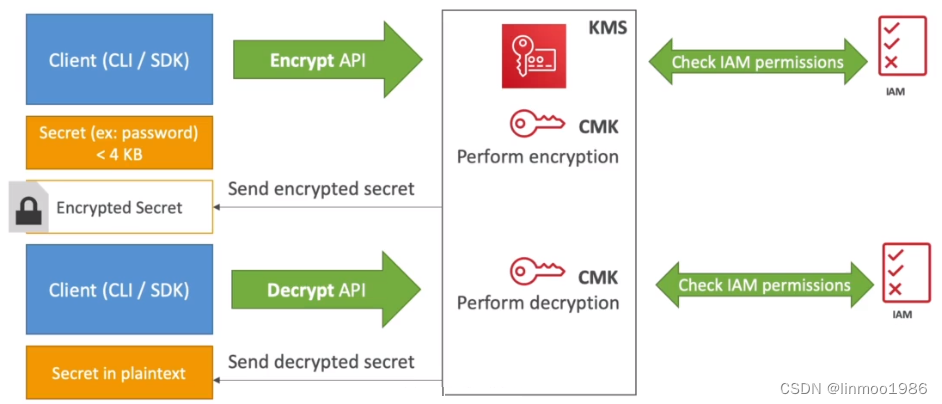
AWS Key Management Service(AWS KMS)是一项托管式服务,可让您轻松创建和控制用于保护您的数据的加密密钥。简单理解,就是一个加密平台,上面保存密钥,同时提供API供客户端进行加密和解密。
2.1 基本特性
- 基本功能是用来加密和解密(考试中但凡与加密解密有关的,那么一般跟KMS也有关系)
- 有AWS管理密钥,因此安全度高
- AWS KMS 与大多数用于加密数据的其他 AWS 服务集成
例题:A company needs to move its write-intensive Amazon RDS for PostgreSQL database from the eu-west-1 Region to the eu-north-1 Region. As part of the migration, the company needs to change from Amazon RDS for PostgreSQL to Amazon Aurora PostgreSQL.
The company is using a new AWS account to host a new Aurora PostgreSQL DB cluster. The RDS database is encrypted with an AWS managed AWS Key Management Service (AWS KMS) key. There must be no interruption to applications that use the RDS for PostgreSQL DB instance.
Which solution will meet these requirements?
A. Create VPC peering between the VPCs in both accounts. Take a snapshot of the RDS DB instance. Export the snapshot to Amazon S3. Create an S3 gateway endpoint. Use the S3 sync command for ongoing synchronization of data. Restore the snapshot from Amazon S3 in the Aurora account. Migrate the snapshot to the Aurora DB cluster.
B. Create VPC peering between the VPCs in both accounts. Import the AWS managed KMS key to the Aurora account. Take a snapshot of the RDS DB instance. Share the snapshot with the Aurora account. Copy the shared snapshot to eu-north-1 in the Aurora account. Migrate the shared snapshot to the Aurora DB cluster. Use AWS Database Migration Service (AWS DMS) with ongoing replication to complete the migration.
C. Create VPC peering between the VPCs in both accounts. Copy the AWS managed KMS key to the Aurora account. Create an Aurora cross-Region read replica of the RDS DB instance in the Aurora account. Promote the read replica from standby DB instance to primary DB instance.
D. Create VPC peering between the VPCs in both accounts. Create a multi-Region customer managed KMS key in the RDS account, and share the key with the Aurora account. Modify the cluster to use the customer managed KMS key. Take a snapshot of the RDS DB instance. Share the snapshot with the Aurora account. Copy the shared snapshot to eu-north-1 in the Aurora account. Migrate the shared snapshot to the Aurora DB cluster. Use AWS Database Migration Service (AWS DMS) with ongoing replication to complete the migration.
答案:D
答案解析:题目要求需要跨区域迁移PostgreSQL数据库。并且使用KMS做密钥管理。因此D选项最合适。
- 提供CLI或者SDK进行加密和解密
- 只能对小于4KB的内容加密
- 集成CloudTrail进行API调用审计
- 密钥可以轮转
2.2 密钥类型
KMS的密钥有3种不同类型,区别如下:(考试中出现客户托管和AWS托管的区别判别)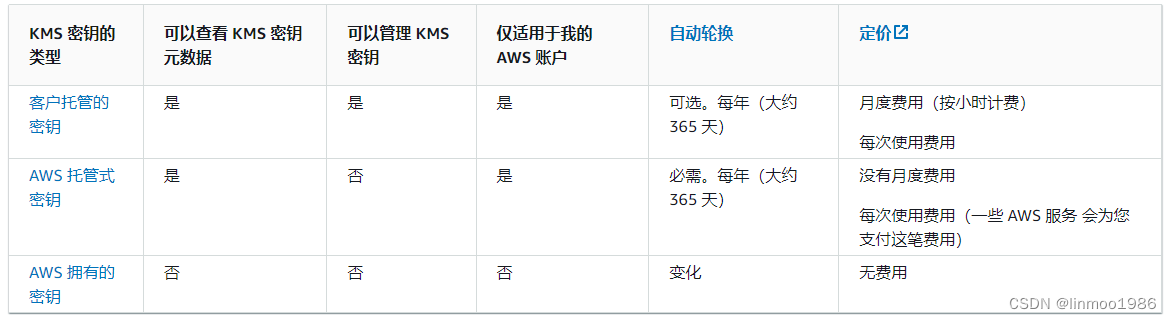
例题:A company has multiple business units. Each business unit has its own AWS account and runs a single website within that account. The company also has a single logging account. Logs from each business unit website are aggregated into a single Amazon S3 bucket in the logging account. The S3 bucket policy provides each business unit with access to write data into the bucket and requires data to be encrypted.
The company needs to encrypt logs uploaded into the bucket using a single AWS Key Management Service (AWS KMS) CMK. The CMK that protects the data must be rotated once every 365 days.
Which strategy is the MOST operationally efficient for the company to use to meet these requirements?
A. Create a customer managed CMK in the logging account. Update the CMK key policy to provide access to the logging account only. Manually rotate the CMK every 365 days.
B. Create a customer managed CMK in the logging account. Update the CMK key policy to provide access to the logging account and business unit accounts. Enable automatic rotation of the CMK.
C. Use an AWS managed CMK in the logging account. Update the CMK key policy to provide access to the logging account and business unit accounts. Manually rotate the CMK every 365 days.
D. Use an AWS managed CMK in the logging account. Update the CMK key policy to provide access to the logging account only. Enable automatic rotation of the CMK.
答案:B
答案解析:题目要求使用KMS管理密钥,并且密钥能够轮转。因此A选项手动轮转比自动轮转要差;C选项同样手动轮转比自动轮转要差;D选项AWS managed CMK默认就是开启rotation,所以无需在手动开启。因此选择B选项
2.3 加密和解密过程
3.4 典型架构
- 通过KMS与S3加密配置架构(需要使用:kms:GenerateDataKey)
例题:A solutions architect needs to implement a client-side encryption mechanism for objects that will be stored in a new Amazon S3 bucket. The solutions architect created a CMK that is stored in AWS Key Management Service (AWS KMS) for this purpose.
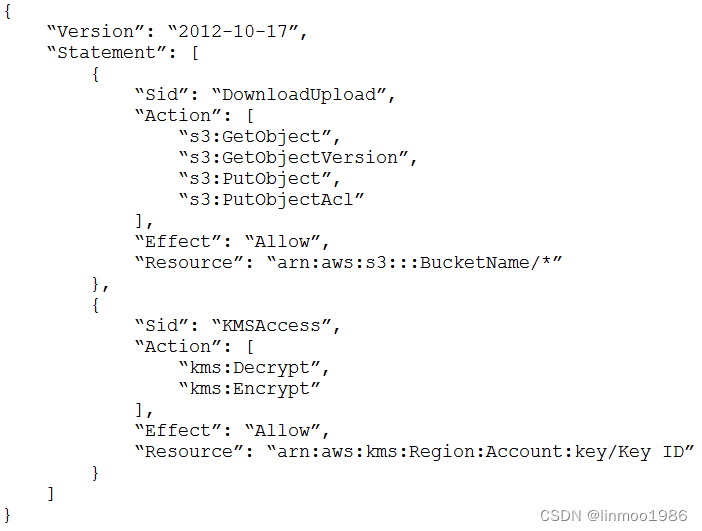
The solutions architect created the following IAM policy and attached it to an IAM role:
During tests, the solutions architect was able to successfully get existing test objects in the S3 bucket. However, attempts to upload a new object resulted in an error message. The error message stated that the action was forbidden.
Which action must the solutions architect add to the IAM policy to meet all the requirements?
A. kms:GenerateDataKey
B. kms:GetKeyPolicy
C. kms:GetPublicKey
D. kms:Sign
答案:A
答案解析:SSE-KMS要上传对象,需要使用AWS kms密钥的kms:GenerateDataKey权限。
例题:A health insurance company stores personally identifiable information (PII) in an Amazon S3 bucket. The company uses server-side encryption with S3 managed encryption keys (SSE-S3) to encrypt the objects. According to a new requirement, all current and future objects in the S3 bucket must be encrypted by keys that the company’s security team manages. The S3 bucket does not have versioning enabled.
Which solution will meet these requirements?
A. In the S3 bucket properties, change the default encryption to SSE-S3 with a customer managed key. Use the AWS CLI to re-upload all objects in the S3 bucket. Set an S3 bucket policy to deny unencrypted PutObject requests.
B. In the S3 bucket properties, change the default encryption to server-side encryption with AWS KMS managed encryption keys (SSE-KMS). Set an S3 bucket policy to deny unencrypted PutObject requests. Use the AWS CLI to re-upload all objects in the S3 bucket.
C. In the S3 bucket properties, change the default encryption to server-side encryption with AWS KMS managed encryption keys (SSE-KMS). Set an S3 bucket policy to automatically encrypt objects on GetObject and PutObject requests.
D. In the S3 bucket properties, change the default encryption to AES-256 with a customer managed key. Attach a policy to deny unencrypted PutObject requests to any entities that access the S3 bucket. Use the AWS CLI to re-upload all objects in the S3 bucket.
答案:B
答案解析:在S3桶属性中,使用AWS KMS管理的加密密钥(SSE-KMS)将默认加密更改为服务器端加密。设置S3桶策略,拒绝未加密的PutObject请求。通过AWS CLI重新上传S3桶中的所有对象。参考:https://docs.aws.amazon.com/AmazonS3/latest/userguide/UsingKMSEncryption.html
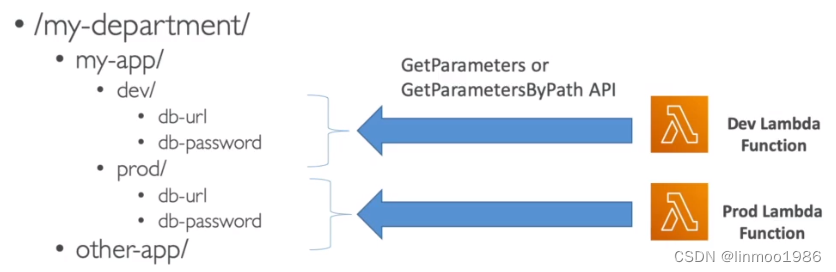
3 Parameter store
Parameter Store(AWS Systems Manager(SSM) 的一项功能)可提供安全的分层存储,用于配置数据管理和密钥管理。您可以将密码、数据库字符串、Amazon Machine Image (AMI) ID 和许可证代码等数据存储为参数值。可以将值存储为纯文本或加密数据。在考试中出现概率较高,重点关注其与Secrets manager的区别。
3.1 基本特性
- severless的服务,使用SDK调用API
- 可以自动结合KMS进行加密
- 有版本和追踪功能
- 能够触发CloudWatch Event
- 能够被CloudFormation中引用
3.2 典型架构
- 开发环境和生产环境配置
4 AWS Secrets manager
AWS Secrets Manager,您可以在数据库凭证、应用程序凭证、OAuth 令牌、API 密钥和其他密钥的整个生命周期内对其进行管理、检索和轮换。许多 AWS 服务将密钥存储在 Secrets Manager 中。其加密也是可以与KMS自动结合。在考试中出现概率较高,重点关注其与Parameter store的区别。
4.1 基本特性
注意点(考试中与Parameter store区别,但出现下面2个应用需求时,基本上就选择Secrets manager):
- 其能使用Lambda自动生成密钥,且能每隔一段时间将密钥轮转(出现密钥轮转,基本上就要选择Secrets manager,虽然Parameter store也能设计轮转但比较麻烦)
例题:A security engineer determined that an existing application retrieves credentials to an Amazon RDS for MySQL database from an encrypted file in Amazon S3. For the next version of the application, the security engineer wants to implement the following application design changes to improve security:
– The database must use strong, randomly generated passwords stored in a secure AWS managed service.
– The application resources must be deployed through AWS CloudFormation.
– The application must rotate credentials for the database every 90 days.
A solutions architect will generate a CloudFormation template to deploy the application.
Which resources specified in the CloudFormation template will meet the security engineer’s requirements with the LEAST amount of operational overhead?
A. Generate the database password as a secret resource using AWS Secrets Manager. Create an AWS Lambda function resource to rotate the database password. Specify a Secrets Manager RotationSchedule resource to rotate the database password every 90 days.
B. Generate the database password as a SecureString parameter type using AWS Systems Manager Parameter Store. Create an AWS Lambda function resource to rotate the database password. Specify a Parameter Store RotationSchedule resource to rotate the database password every 90 days.
C. Generate the database password as a secret resource using AWS Secrets Manager. Create an AWS Lambda function resource to rotate the database password. Create an Amazon EventBridge scheduled rule resource to trigger the Lambda function password rotation every 90 days.
D. Generate the database password as a SecureString parameter type using AWS Systems Manager Parameter Store. Specify an AWS AppSync DataSource resource to automatically rotate the database password every 90 days.
答案:A
答案解析:题目关键词:randomly generated passwords, rotate credentials。B选项和D选项对于轮换密钥过复杂,因此只能选择A选项或者C选项;而设置RotationSchedule做自动轮转不需要EventBridge,因此答案为A
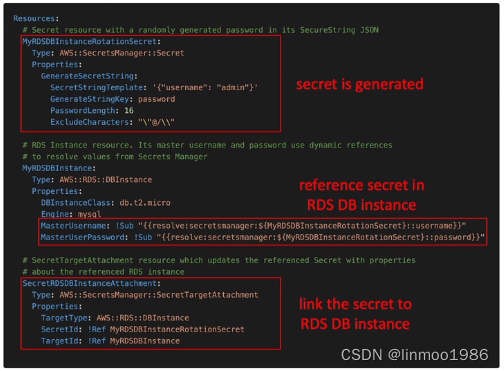
- 与RDS深度结合
4.2 典型架构
- 与CloudFormation集成
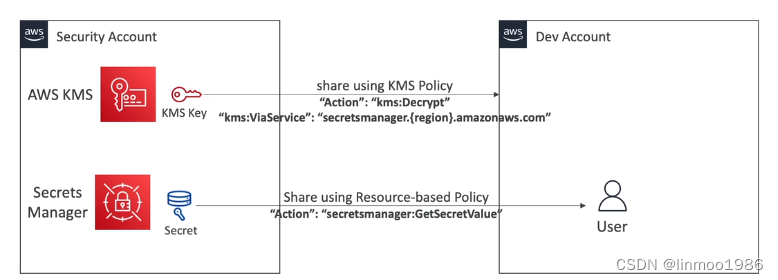
- 跨账号共享Secrets
5 AWS Certificate manager(ACM)
AWS Certificate Manager (ACM) 处理创建、存储和续订公有及私有 SSL/TLS X.509 证书和密钥的复杂操作,这些证书和密钥可保护您的AWS网站和应用程序。您可以直接通过 ACM 签发证书,或者通过将第三方证书导入 ACM 管理系统中,为集成AWS服务提供证书。很明显,它是一个SSL/TLS X.509 证书和密钥的管理平台,要真正弄清楚ACM,我们先要弄清楚几个内容:SSL/TLS、SNI、DNSSEC。
5.1 SSL/TLS、SNI、DNSSEC
5.1.1 SSL/TLS
网络传输中,如果我们使用HTTP传输,其实是不安全的,因此需要加密。而SSL/TLS(安全套接层/传输套接层)是Netscape公司率先采用的网络安全协议。它是在传输通信协议(TCP/IP)上实现的一种安全协议,采用公开密钥技术。也就是说通过SSL/TLS可实现加密,HTTPS就是通过SSL/TLS技术实现安全加密。加密原理如下: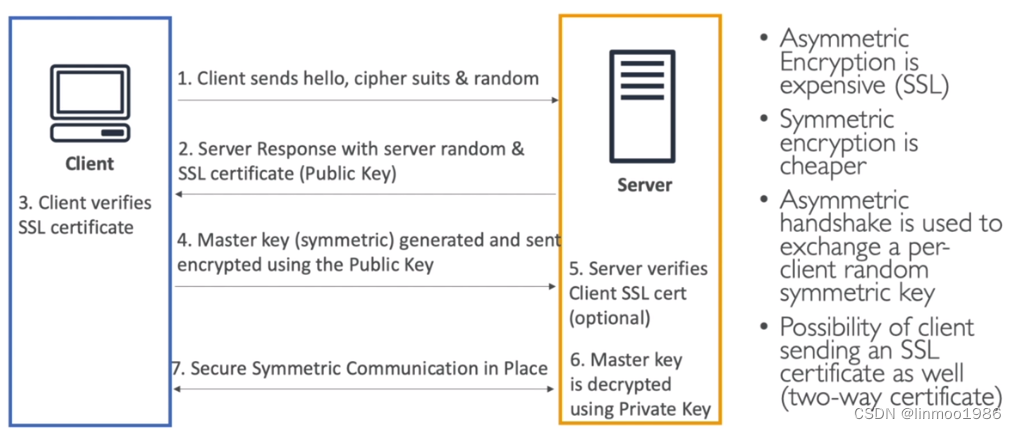
5.1.2 SNI
从4.1.1图中知道加密需要一个叫SSL Certificate,也就是所谓的安全证书。SNI的作用就是可以在同一个web服务器中实现多个SSL Certificate,AWS的负载均衡服务ALB和NLB都有此功能,但CLB不具备。
5.1.3 DNSSEC
下图是一个“Man-in-the-MiddleAttack(中间人攻击)”,以及通过SSL加密后防止的原理: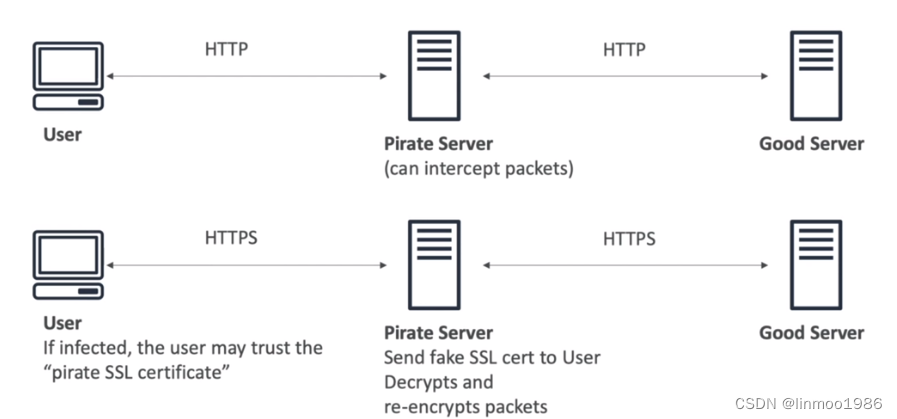
除了使用SSL外,还有一种可以放在这种中间人攻击,那就是DNSSEC,但是AWS Route53不支持DNSSEC,除非你使用第三方的DNS。
5.2 基本特性
- 管理和颁发Certificate的AWS服务
- 可以与多个组件集成(ELB、CloudFormation、API gateway等)
- 公有证书:必须使用符合 DNS 的主题名称
- 私有证书:CA 可能位于您的账户中,也可能由其他账户与您共享
- 证书更新可以托给ACM管理
- 只是一个单区域的,不能跨区域
6 AWS CloudHSM
AWS CloudHSM将AWS云的优势与硬件安全模块 (HSM) 的安全性相结合。硬件安全模块 (HSM) 是一种计算设备,可处理加密操作并提供加密密钥的安全存储。借助AWS CloudHSM,您可以完全控制 AWS 云中的高可用性 HSM,这些密码具有低延迟访问权限,并拥有可自动执行 HSM 管理(包括备份、配置、配置和维护)的安全信任根。简单来说就是一个硬件版本的KMS。主要记住以下几点特性和与KMS的比较即可
6.1 基本特性
- 是一个基于硬件的加密工具
- 支持对称和非对称加密
- 密钥需要自己管理,不能托管AWS
- 可以部署多可用区集群
- 必须使用CloudHSM Client Software
- 不是免费的(注意:考试中出现过S3存储加密,有SSE-S3和CloudHSM的选择,CloudHSM是收费的,并非开销最小的选择)
6.2 与KMS比较

7 AWS Inspector
Amazon Inspector 是一项漏洞管理服务,持续扫描您的AWS工作负载中是否存在软件漏洞和意外网络暴露。Amazon Inspector 会自动发现和扫描正在运行的 Amazon EC2 实例、亚马逊Elastic Container Registry (Amazon ECR) 中的容器映像,以及针对已知软件漏洞和意外网络泄露的AWS Lambda函数。这里只需要记住以下几点:
- 它只用于EC2、ECR和Lambda的漏洞扫描即可
- 漏洞规则是AWS管理的
- 最后生成报告
8 Amazon GuardDuty
Amazon GuardDuty 是一项安全监控服务,用于分析和处理AWS CloudTrail管理事件基础数据源、AWS CloudTrail事件日志、VPC 流日志(来自 Amazon EC2 实例)和 DNS 日志。它还处理 Kubernetes 审计日志、RDS 登录活动、S3 日志、EBS 卷、运行时监控和 Lambda 网络活动日志等功能。简单理解就是一个安全监测工具,将通过一些日志作为输入,然后通过机器学习等算法分析出存在异常的内容,再通过CloudWatch发出警告。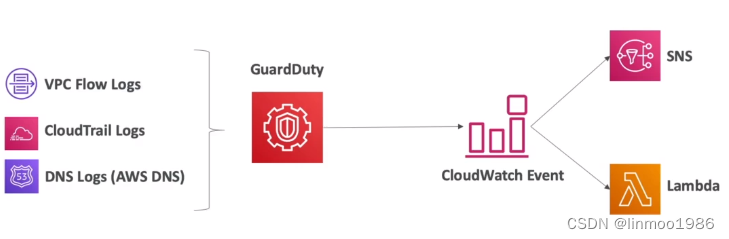
9 AWS Systems Manager(SSM)
AWS Systems Manager 是您 AWS 应用程序和资源的操作中心,也是混合和多云环境的安全端到端管理解决方案,可以实现大规模的安全操作。简单理解就是一个可以对你的EC2、本地数据中心的服务器的操作系统做管理的平台。
9.1 特性
- 管理你的EC2或者本地数据中心的服务器
- 发现你基础设施存在的安全问题
- 可以更新你服务器的补丁(注意:考试中遇到patching,基本上就是与SSM相关)
A Solutions Architect must establish a patching plan for a large mixed fleet of Windows and Linux servers.The patching plan must be implemented securely, be audit ready, and comply with the company’s business requirements. Which option will meet these requirements with MINIMAL effort?
A. Install and use an OS-native patching service to manage the update frequency and release approval for all instances.Use AWS Config to verify the OS state on each instance and report on any patch compliance issues
B. Use AWS Systems Manager on all instances to manage patching. Test patches outside of production and then deployduring a maintenance window with the appropriate approval.
C. Use AWS OpsWorks for Chef Automate to run a set of scripts that will iterate through all instances of a given typessue the appropriate OS command to get and install updates on each instance, including any required restarts during themaintenance window.
D. Migrate all applications to AWS Ops Works and use Ops Works automatic patching support to keep the OS up-to-datefollowing the initial installation. Use AWS Config to provide audit and compliance reporting.
答案:B
答案解析:这道题关键词:Windows and Linux servers,patching plan,MINIMAL effort。主要考察AWS Config、Systems Manager、OpsWorks的使用场景。AWS Config主要是配置管理,OpsWorks也有更新补丁功能,是Puppet 或 Chef迁移到AWS云上使用,但是AWS如果不强调Puppet 或 Chef迁移,补丁修复建议都是使用Systems Manager(https://docs.aws.amazon.com/zh_cn/opsworks/latest/userguide/workingsecurity-updates.html)。而Systems Manager其中一个重要功能就是更新服务器补丁。因此选B。
例题:A company needs to implement a patching process for its servers. The on-premises servers and Amazon EC2 instances use a variety of tools to perform patching.
Management requires a single report showing the patch status of all the servers and instances.
Which set of actions should a solutions architect take to meet these requirements?
A. Use AWS Systems Manager to manage patches on the on-premises servers and EC2 instances. Use Systems Manager to generate patch compliance reports
B. Use AWS OpsWorks to manage patches on the on-premises servers and EC2 instances. Use Amazon QuickSight integration with OpsWorks to generate patch compliance reports.
C. Use an Amazon EventBridge (Amazon CloudWatch Events) rule to apply patches by scheduling an AWS Systems Manager patch remediation job. Use Amazon Inspector to generate patch compliance reports.
D. Use AWS OpsWorks to manage patches on the on-premises servers and EC2 instances. Use AWS X-Ray to post the patch status to AWS Systems Manager OpsCenter to generate patch compliance reports.
答案:A
答案解析:题目要求给本地和EC2更新补丁。OpsWorks是主要是做配置管理;EventBridge更多是应用程序组件连接在一起的bus。而Systems Manager本身就有patching功能
- 适用于Windows和Linux OS
- 集成了CloudWatch metrics/dashboards/AWS Config
- Session Manager:可以管理 Amazon Elastic Compute Cloud(Amazon EC2)实例、边缘设备、本地服务器和虚拟机(VM)。您可使用基于浏览器的一键式交互 Shell 或 AWS Command Line Interface (AWS CLI)。Session Manager 提供安全且可审计的节点管理,而无需打开入站端口、维护堡垒主机或管理 SSH 密钥。
例题:A startup company hosts a fleet of Amazon EC2 instances in private subnets using the latest Amazon Linux 2 AMI. The company’s engineers rely heavily on SSH access to the instances for troubleshooting.
The company’s existing architecture includes the following:
– A VPC with private and public subnets, and a NAT gateway
– Site-to-Site VPN for connectivity with the on-premises environment
– EC2 security groups with direct SSH access from the on-premises environment
The company needs to increase security controls around SSH access and provide auditing of commands run by the engineers.
Which strategy should a solutions architect use?
A. Install and configure EC2 Instance Connect on the fleet of EC2 instances. Remove all security group rules attached to EC2 instances that allow inbound TCP on port 22. Advise the engineers to remotely access the instances by using the EC2 Instance Connect CLI.
B. Update the EC2 security groups to only allow inbound TCP on port 22 to the IP addresses of the engineer’s devices. Install the Amazon CloudWatch agent on all EC2 instances and send operating system audit logs to CloudWatch Logs.
C. Update the EC2 security groups to only allow inbound TCP on port 22 to the IP addresses of the engineer’s devices. Enable AWS Config for EC2 security group resource changes. Enable AWS Firewall Manager and apply a security group policy that automatically remediates changes to rules.
D. Create an IAM role with the AmazonSSMManagedInstanceCore managed policy attached. Attach the IAM role to all the EC2 instances. Remove all security group rules attached to the EC2 instances that allow inbound TCP on port 22. Have the engineers install the AWS Systems Manager Session Manager plugin for their devices and remotely access the instances by using the start-session API call from Systems Manager
答案:D
答案解析:题目要求管理SSH登录,最好的就是使用Systems Manager的Session Manager方案,参考:https://docs.aws.amazon.com//systems-manager/latest/userguide/session-manager.html
例题:A research company is running daily simulations in the AWS Cloud to meet high demand. The simulations run on several hundred Amazon EC2 instances that are based on Amazon Linux 2. Occasionally, a simulation gets stuck and requires a cloud operations engineer to solve the problem by connecting to an EC2 instance through SSH.
Company policy states that no EC2 instance can use the same SSH key and that all connections must be logged in AWS CloudTrail.
How can a solutions architect meet these requirements?
A. Launch new EC2 instances, and generate an individual SSH key for each instance. Store the SSH key in AWS Secrets Manager. Create a new IAM policy, and attach it to the engineers’ IAM role with an Allow statement for the GetSecretValue action. Instruct the engineers to fetch the SSH key from Secrets Manager when they connect through any SSH client.
B. Create an AWS Systems Manager document to run commands on EC2 instances to set a new unique SSH key. Create a new IAM policy, and attach it to the engineers’ IAM role with an Allow statement to run Systems Manager documents. Instruct the engineers to run the document to set an SSH key and to connect through any SSH client.
C. Launch new EC2 instances without setting up any SSH key for the instances. Set up EC2 Instance Connect on each instance. Create a new IAM policy, and attach it to the engineers’ IAM role with an Allow statement for the SendSSHPublicKey action. Instruct the engineers to connect to the instance by using a browser-based SSH client from the EC2 console.
D. Set up AWS Secrets Manager to store the EC2 SSH key. Create a new AWS Lambda function to create a new SSH key and to call AWS Systems Manager Session Manager to set the SSH key on the EC2 instance. Configure Secrets Manager to use the Lambda function for automatic rotation once daily. Instruct the engineers to fetch the SSH key from Secrets Manager when they connect through any SSH client.
答案:D
答案解析:要求不需要使用SSH直接登录,那么使用Systems Manager的Session Manager方案是最好的方案,参考:https://docs.aws.amazon.com//systems-manager/latest/userguide/session-manager.html
例题:A company’s AWS architecture currently uses access keys and secret access keys stored on each instance to access AWS services. Database credentials are hard-coded on each instance. SSH keys for command-line remote access are stored in a secured Amazon S3 bucket. The company has asked its solutions architect to improve the security posture of the architecture without adding operational complexity.
Which combination of steps should the solutions architect take to accomplish this? (Choose three.)
A. Use Amazon EC2 instance profiles with an IAM role
B. Use AWS Secrets Manager to store access keys and secret access keys
C. Use AWS Systems Manager Parameter Store to store database credentials
D. Use a secure fleet of Amazon EC2 bastion hosts for remote access
E. Use AWS KMS to store database credentials
F. Use AWS Systems Manager Session Manager for remote access
答案:ACF
答案解析:题目要改进安全访问EC2方式。因此使用Systems Manager Session Manager是最合适,因此步骤是ACF。
9.2 工作原理
- 在操作系统中安装SSM Agent
- EC2还需要授权角色给SSM
9.3 Run Command
- 可以执行document、script、command
- 同时给多台实例执行命令
- 不需要使用SSH(而是通过SSM Agent)
9.4 Systems Manager Parameter Store
请参照本章的第3点《3 Parameter store》。
10 AWS Security Hub
AWS Security Hub 可让您全面了解您的安全状态AWS并帮助您评估您的AWS环境与安全行业标准和最佳实践背道而驰。简单来说就是评估你AWS上面存在的一些可能的安全隐患(这个安全隐患是行业一些标准或者实践)。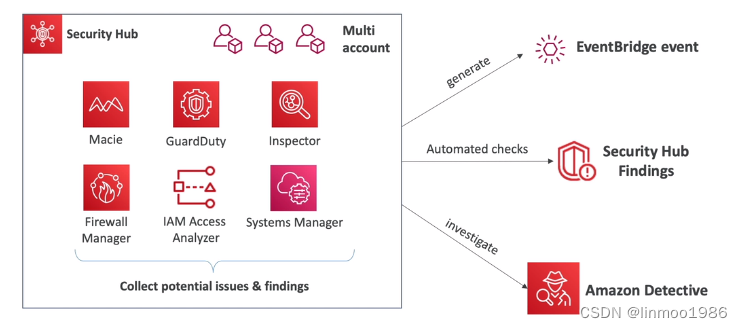
- 支持多账号安全管理(注意:如果出现多账号环境安全状态评估,一般与Security Hub相关)
- 能够自动查找更新和补救措施
- 与Control Tower的区别,都是做安全合规的,但是有一个最大区别Control Tower是检测权限是否泄漏,Security Hub是检测是否存在安全隐患。(注意:考试中经常选项会同时出现Control Tower和Security Hub,请注意2者使用场景)
11 Amazon Detective
Amazon Detective 可帮助您分析、调查和快速识别安全结果或可疑活动的根本原因。Detective 会自动从您的AWS资源中收集日志数据。然后,它使用机器学习、统计分析和图论来生成可视化效果,帮助您更快、更高效地进行安全调查。
当你使用7 GuardDuty、Security Hub等工具发现出问题,需要知道详细造成问题的原因,那么就需要Detective,它提供可视化的日志分析,最终让你迅速发现问题所在。
12 Amazon Macie
Amazon Macie 是一项数据安全服务,该服务使用机器学习和模式匹配来发现敏感数据,提供对数据安全风险的可见性,并实现针对这些风险的自动防护。
13 AWS组件内的安全
13.1 Web Server 集成SSL
- 基于ALB的SSL加密
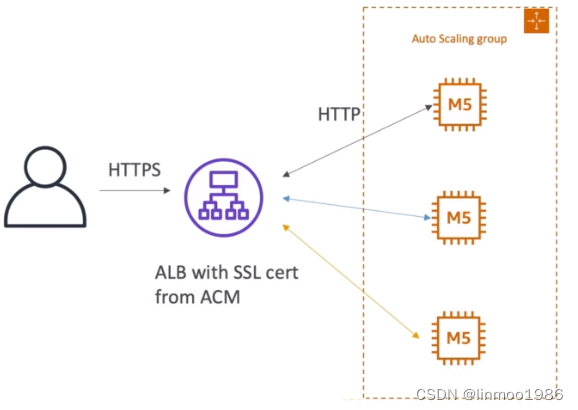
例题:A company is planning to host a web application on AWS and wants to load balance the traffic across a group of Amazon EC2 instances. One of the security requirements is to enable end-to-end encryption in transit between the client and the web server.Which solution will meet this requirement?
A. Place the EC2 instances behind an Application Load Balancer (ALB). Provision an SSL certificate using AWS Certificate Manager (ACM), and associate the SSL certificate with the ALB. Export the SSL certificate and install it on each EC2 instance. Configure the ALB to listen on port 443 and to forward traffic to port 443 on the instances.
B. Associate the EC2 instances with a target group. Provision an SSL certificate using AWS Certificate Manager (ACM). Create an Amazon CloudFront distribution and configure it to use the SSL certificate. Set CloudFront to use the target group as the origin server.
C. Place the EC2 instances behind an Application Load Balancer (ALB) Provision an SSL certificate using AWS Certificate Manager (ACM), and associate the SSL certificate with the ALB. Provision a third-party SSL certificate and install it on each EC2 instance. Configure the ALB to listen on port 443 and to forward traffic to port 443 on the instances.
D. Place the EC2 instances behind a Network Load Balancer (NLB). Provision a third-party SSL certificate and install it on the NLB and on each EC2 instance. Configure the NLB to listen on port 443 and to forward traffic to port 443 on the instances.
答案:C
答案解析:Amazon颁发的公共证书不能安装在EC2实例上。启用端到端加密时,必须使用第三方SSL证书,所以是C或D。而D会存在可能有被入侵风险,如果加入CloudHSM管理则可避免。因此答案选择C。
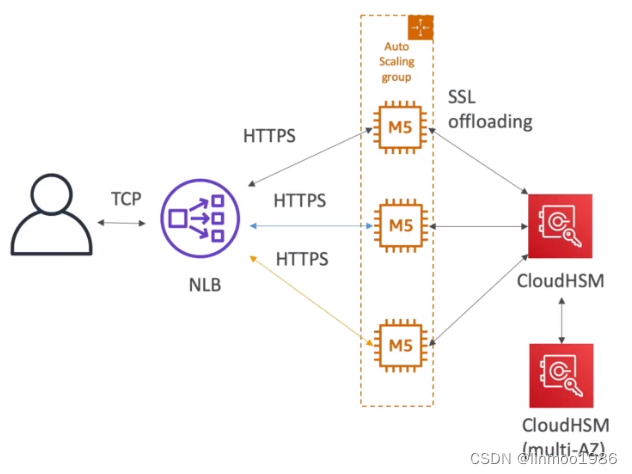
- 基于NLB在EC2进行SSL加密(缺点:证书会绑定在EC2,可能有被入侵风险,使用CloudHSM可以避免该风险)
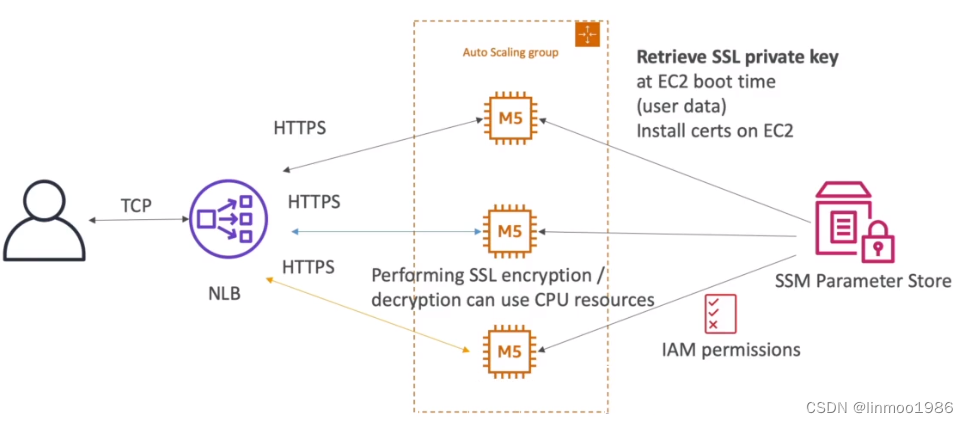
- 基于CloudHSM对EC2进行SSL加密
13.2 RDS security
关于RDS的安全方面,需要知道以下几点:
- Transparent Data Encryption(TDE)只能适合Oracle和SQL Server
- SSL 加密RDS,适用于所有数据库
- IAM可以用于MySQL和PostgreSQL,但实际验证还需要RDS本身
- CloudTrail不能用于查询RDS
13.3 S3 security
13.3.1 四种加密方式
- SSE-S3:有AWS自动加密S3对象,密钥管理完全有AWS管理
- SSE-KMS:有KMS做加密密钥管理
- SSE-C:自己管理密钥
- Client Side Encryption:完全有自己管理密钥平台 另外:还有Glacier(本身使用AEC-256加密)建议:使用HTTPS作为endpoint,因为HTTPS强制使用SSE-C
13.3.2 S3的Events
- S2 Access Logs:记录对于S3存储桶的所有请求操作
- S3 Events Notifications:属于监控桶级别的通知,可用于监听通知
- Trusted Advisor:检查S3存储桶的权限(当存储桶为public情况下)
- CloudWatch Events:属于监控对象级别的通知
13.3.3 S3的安全
- 用户层面:基于IAM policies控制
- 资源层面:基于bucket policies或者ACL。其中bucket policies为考试重点,可以跨账户授权
13.3.4 其它相关安全措施
- S3 pre-signed URLs:生成一个pre-signed URLs,用于上传和下载。一般用于临时权限,有时间限制。
- Endpoint Gateway:这个在网络那一章讲过,通过Endpoint Gateway可以让VPC通过内网方式访问S3,更加安全可靠,但不能传递边缘路由。
- 对象锁定:借助 S3 对象锁定,您可以使用一次写入,多次读取 (WORM) 模式存储对象。对象锁定可帮助防止在固定的时间段内或无限期地删除或覆盖对象。可以使用对象锁定来帮助您满足需要 WORM 存储的法规要求,或只是添加另一个保护层来防止对象被更改和删除。
13.4 Network Security, DDoS, Shield & WAF
关于网络安全方面,在网络那一章分散讲过一些,这里系统讲一下
13.4.1 Network Security
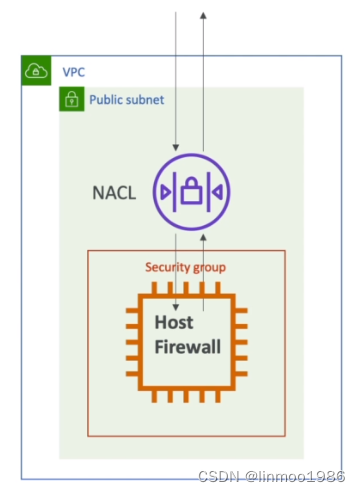
如上图,有3个安全管理的内容:
- NACL:网络访问控制列表 (ACL) 在子网级别允许或拒绝特定的入站或出站流量。您可以使用 VPC 的默认网络 ACL,也可以为 VPC 创建自定义网络 ACL,使其规则与您安全组的规则相似,以便为您的 VPC 添加额外安全层。注意:NACL是无状态(意味着入出都需要定义规则)
- 安全组:这不是VPC,这是EC2、ALB等自带的安全组,也是用于控制网络访问。注意:安全组是有状态的(意味着定义入流量,自动允许响应)
- Firewall:EC2本身的防火墙
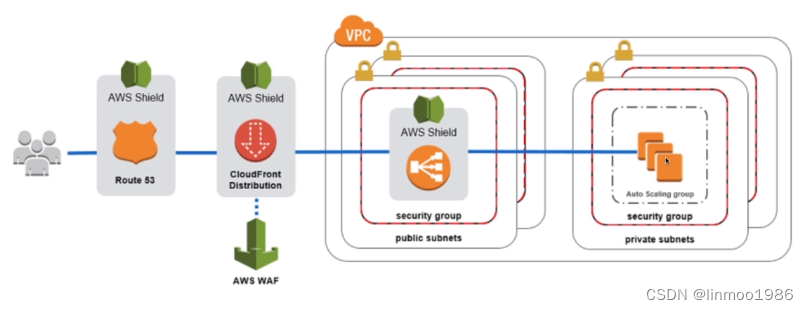
13.4.2 DDoS&Shield
- 基本概念:通过大量机器的访问导致你的web服务请求或者连接占满,导致正常用户无法访问
- 类别:SYN Flood、UDP Reflection、DNS flood attack、Slow Loris attack
- AWS的防御措施:AWS Shield Standard、AWS Shield Advanced、AWS WAF(考试经常出现)
- CloudFront和Route53默认能够预防DDoS攻击
例题:A company maintains a restaurant review website. The website is a single-page application where files are stored in Amazon S3 and delivered using Amazon CloudFront. The company receives several fake postings every day that are manually removed. The security team has identified that most of the fake posts are from bots with IP addresses that have a bad reputation within the same global region. The team needs to create a solution to help restrict the bots from accessing the website. Which strategy should a solutions architect use?
A. Use AWS Firewall Manager to control the CloudFront distribution security settings. Create a geographical block rule and associate it with Firewall Manager.
B. Associate an AWS WAF web ACL with the CloudFront distribution. Select the managed Amazon IP reputation rule group for the web ACL with a deny action.
C. Use AWS Firewall Manager to control the CloudFront distribution security settings. Select the managed Amazon IP reputation rule group and associate it with Firewall Manager with a deny action.
D. Associate an AWS WAF web ACL with the CloudFront distribution. Create a rule group for the web ACL with a geographical match statement with a deny action.
答案:B
答案解析:题目要求阻止来说某些IP。参考:https://docs.aws.amazon.com/waf/latest/developerguide/aws-managed-rule-groups-ip-rep.html
例题:A company has a website that runs on Amazon EC2 instances behind an Application Load Balancer (ALB). The instances are in an Auto Scaling group. The ALB is associated with an AWS WAF web ACL.
The website often encounters attacks in the application layer. The attacks produce sudden and significant increases in traffic on the application server. The access logs show that each attack originates from different IP addresses. A solutions architect needs to implement a solution to mitigate these attacks.
Which solution will meet these requirements with the LEAST operational overhead?
A. Create an Amazon CloudWatch alarm that monitors server access. Set a threshold based on access by IP address. Configure an alarm action that adds the IP address to the web ACL’s deny list.
B. Deploy AWS Shield Advanced in addition to AWS WAF. Add the ALB as a protected resource.
C. Create an Amazon CloudWatch alarm that monitors user IP addresses. Set a threshold based on access by IP address. Configure the alarm to invoke an AWS Lambda function to add a deny rule in the application server’s subnet route table for any IP addresses that activate the alarm.
D. Inspect access logs to find a pattern of IP addresses that launched the attacks. Use an Amazon Route 53 geolocation routing policy to deny traffic from the countries that host those IP addresses.
答案:B
答案解析:题目出现大量不同地方IP攻击,很明显是一个DDos攻击,因此使用Shield 防御DDos。因此选择B选项
13.5 Network Firewall
Network Firewall是在VPC中创建的虚拟私有云(VPC)提供的有状态、可管理的网络防火墙和入侵检测和防御服务。简单理解就是VPC上的防火墙,提供有状态的防火墙服务。
13.5.1 基本特性
- 工作在网络第3层或第7层
- 可以控制:VPC之间的流量、互联网与VPC之间的流量、VPN或Direct Connect到VPC之间的流量
- 内部其实就是通过负载均衡代理模式将流量都通过代理做管理
- 与Firewall Manager的规则集成

13.5.2 典型架构
- 通过Inspection VPC做整个AWS网络流量控制
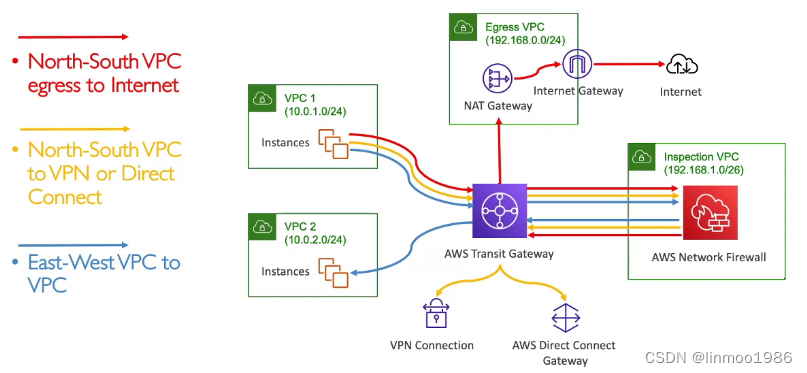 (注意:如果考试中出现希望控制公司整个AWS网络的入站或者出站流量,那么一般会采用以上架构:Transit Gateway+Network Firewall)
(注意:如果考试中出现希望控制公司整个AWS网络的入站或者出站流量,那么一般会采用以上架构:Transit Gateway+Network Firewall)
13.6 网络安全架构
下面以不同架构如何阻止某些IP访问:
- NACL和Security Group架构
 通过NACL的denied规则阻止某些IP 通过EC2的Security Group的允许规则屏蔽其它IP
通过NACL的denied规则阻止某些IP 通过EC2的Security Group的允许规则屏蔽其它IP - ALB架构
 通过NACL的denied规则阻止某些IP 通过ALB的Security Group允许规则屏蔽其它IP 通过ALB的WAF屏蔽IP 不能通过EC2的Security Group的允许规则屏蔽其它IP,因为EC2只接受来自ALB,所以IP都是一样的
通过NACL的denied规则阻止某些IP 通过ALB的Security Group允许规则屏蔽其它IP 通过ALB的WAF屏蔽IP 不能通过EC2的Security Group的允许规则屏蔽其它IP,因为EC2只接受来自ALB,所以IP都是一样的 - NLB架构
 通过NACL的denied规则阻止某些IP 不能通过NLB屏蔽其它IP,因为NLB没有Security Group 不能通过ALB的WAF屏蔽IP,因为NLB没有WAF 通过EC2的Security Group的允许规则屏蔽其它IP
通过NACL的denied规则阻止某些IP 不能通过NLB屏蔽其它IP,因为NLB没有Security Group 不能通过ALB的WAF屏蔽IP,因为NLB没有WAF 通过EC2的Security Group的允许规则屏蔽其它IP - CloudFront和ALB
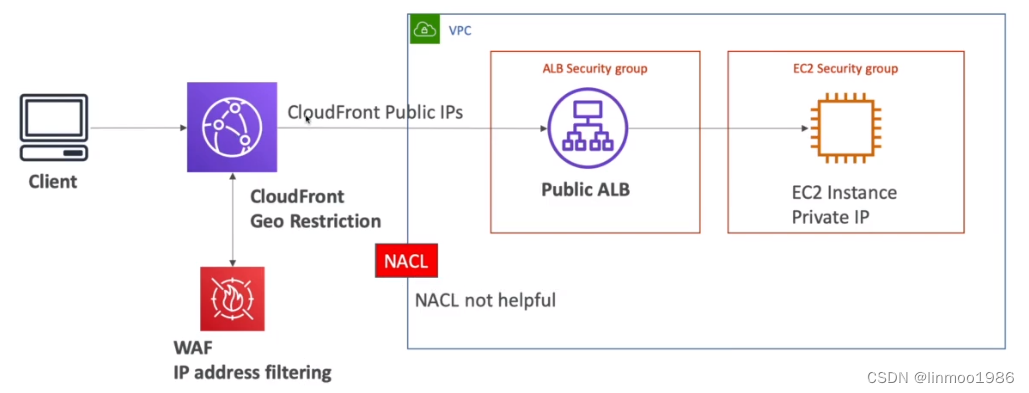 通过CloudFront的Geo Restriction限制某些区域 通过CloudFront的WAF限制IP 不能通过NACL和ALB,因为他们接收到的IP是CloudFront的IP,并非客户端IP
通过CloudFront的Geo Restriction限制某些区域 通过CloudFront的WAF限制IP 不能通过NACL和ALB,因为他们接收到的IP是CloudFront的IP,并非客户端IP
版权归原作者 linmoo1986 所有, 如有侵权,请联系我们删除。