对未来的真正慷慨,是把一切献给现在。
** ——加缪**
1.查壳
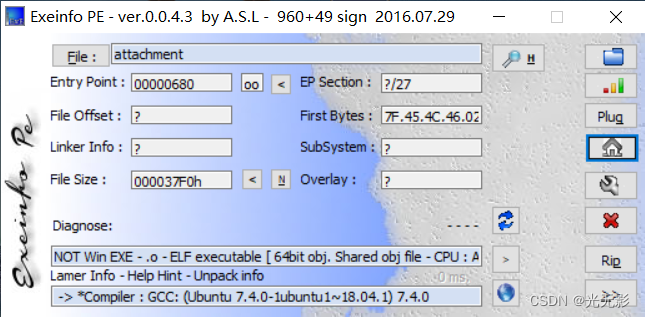
64bit可执行文件
2.处理花指令,找到main函数
操作讲解(讲解后配有这一步骤的视屏)
我们在函数窗口找不到main函数,可能存在一些脏字节之类的东西导致main函数反编译失败
先打开string窗口,跟踪找一下main函数的位置+
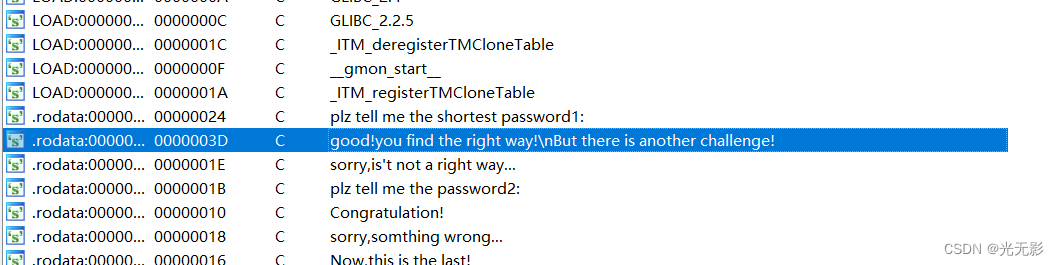
发现一个可疑的字符串
跟进,按下X交叉引用

跟进找到引用这个字符串的函数
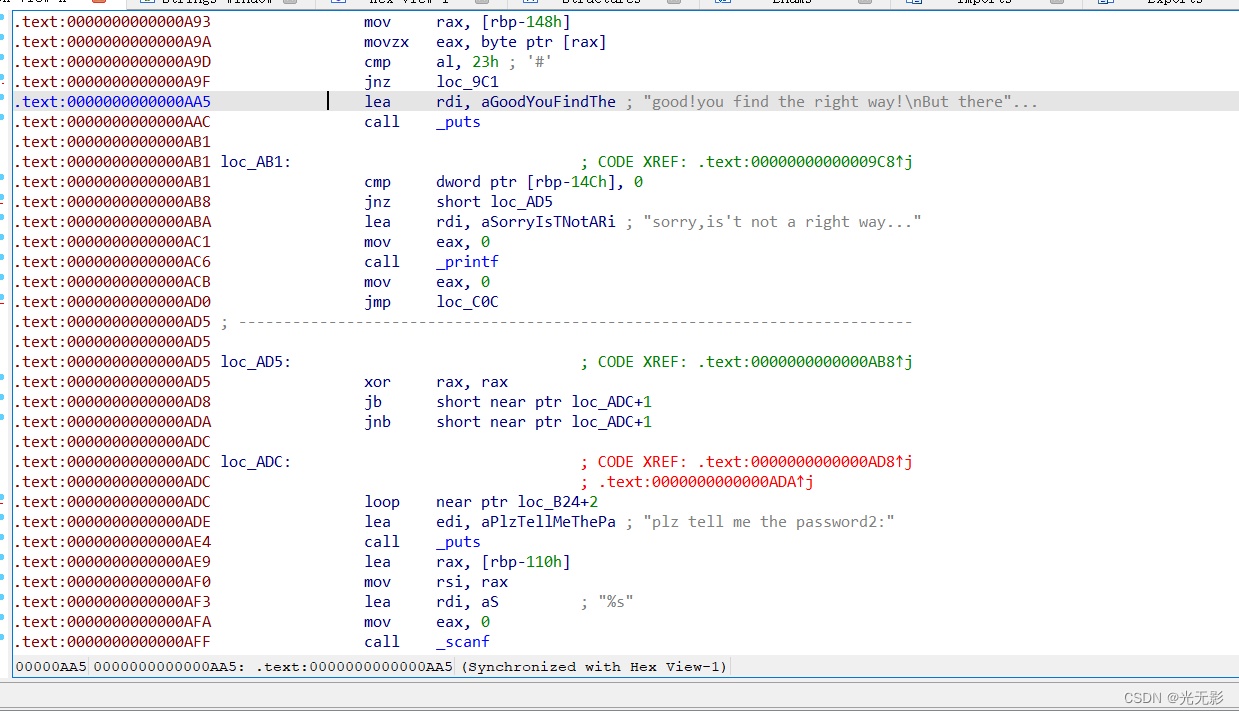 发现代码标红了
发现代码标红了
有一些花指令,nop掉,nop的方法如下:
选中花指令 Edit -> Patch program -> Assemble

花指令的位置:
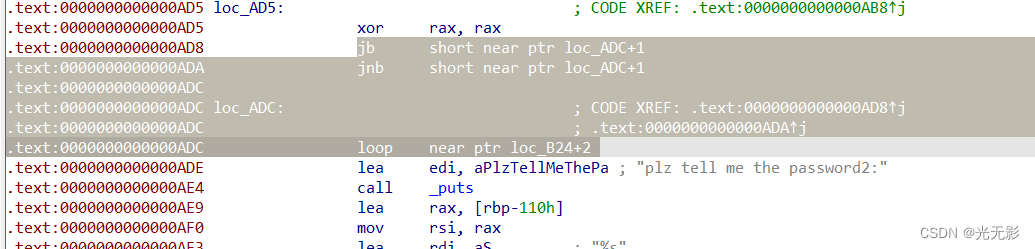
第一处,nop掉

第二处花指令,nop掉
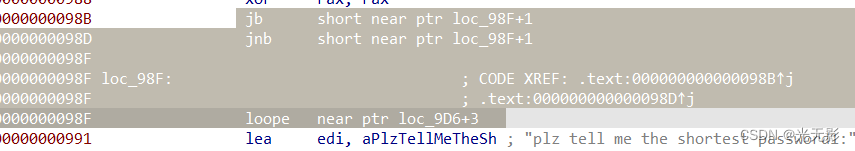
第三处花指令,nop掉

第四处花指令,nop掉
光标点在nop上面,按下如下过程点击

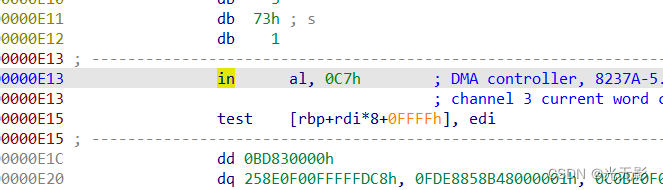
光标移到in处,Edit -> Patch program -> change byte查看字节码,很可能E4是个脏字节,影响了C7(mov)指令的反汇编

我们把E4改为90(90对应的操作码就是nop)
然将这里的数据选中,按下快捷键C重新分析
之后我们选中从push到return的标红的区间按下快捷键P,将其识别为一个函数
注意这一段标红区域有两个retn,有两个函数,要分开来P
这一操作过程可以参考下面的视频:
nop花指令
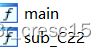
进过上述操作,我们就得到了main函数和另一个函数
3.静态分析第一部分,psword1
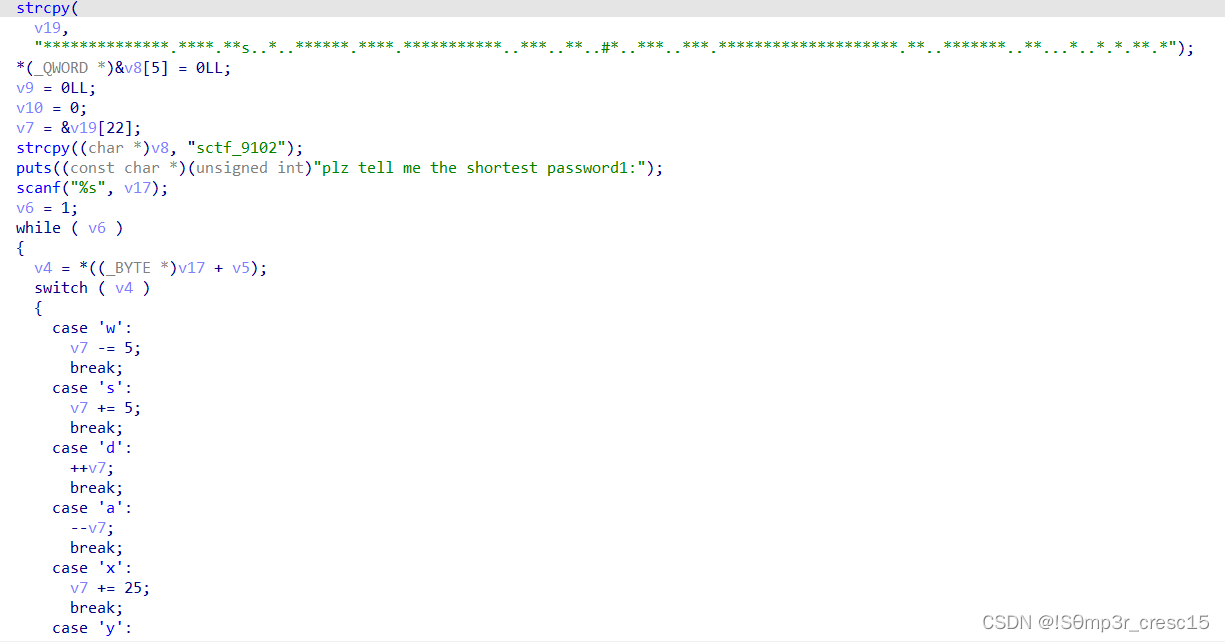
我们看到了一个迷宫图案和移动操作
这又是一个迷宫题
但是有六个移动键,有可能是一个立体迷宫
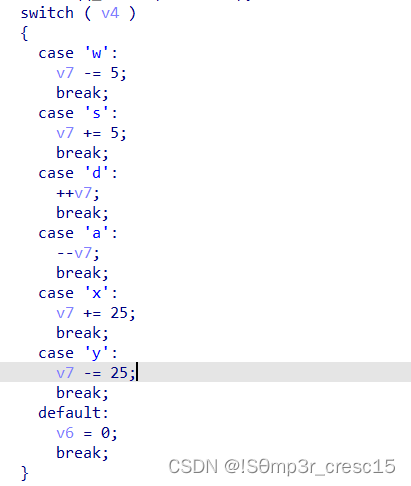
根据这里的数值判断,这可能是一个5×5×5的迷宫
将字符串排列成迷宫:
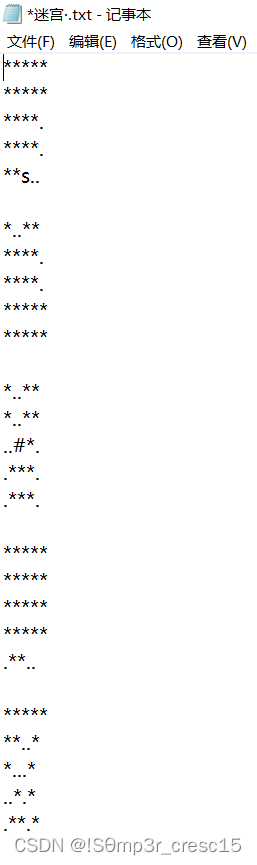
走迷宫得到的路径是ddwwxxssxaxwwaasasyywwdd
4.静态分析第二部分,psword2
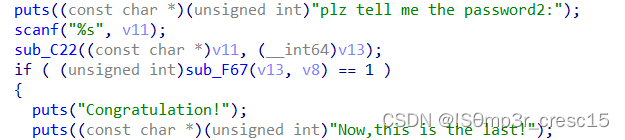
可以看出password2的关键操作函数是sub_C22,且第一个参数就是出入的psword2
跟进查看
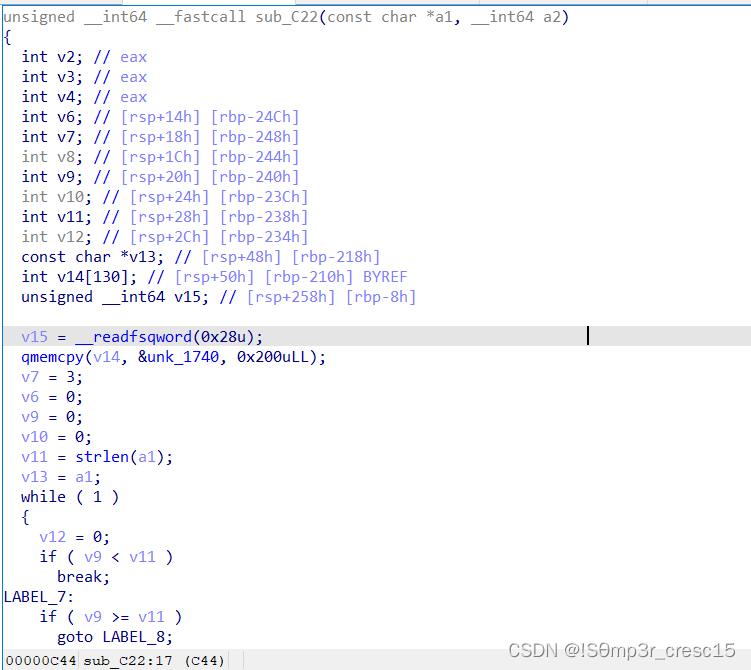
根据这段代码编写wp
#include <stdio.h>
unsigned int data[128] = {
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x3E, 0x7F, 0x7F, 0x7F, 0x3F,
0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3A, 0x3B,
0x3C, 0x3D, 0x7F, 0x7F, 0x7F, 0x40, 0x7F, 0x7F,
0x7F, 0x00, 0x01, 0x02, 0x03, 0x04, 0x05, 0x06,
0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E,
0x0F, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16,
0x17, 0x18, 0x19, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F, 0x20,
0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27, 0x28,
0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30,
0x31, 0x32, 0x33, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F
};
int main()
{
int ctf[3] = { 0x736374,0x665f39,0x313032 };
int i0, i1, i2, i3, i4, i5;
for (i0 = 0; i0 < 3; i0++)
{
for(i1=32;i1<128;i1++)
for (i2 = 32; i2 < 128; i2++)
for (i3 = 32; i3 < 128; i3++)
for (i4 = 32; i4 < 128; i4++)
{
i5 = (((((data[i1] << 6) | data[i2]) << 6) | data[i3]) << 6) | data[i4];
if (i5 == ctf[i0])
printf("%c%c%c%c",i1, i2, i3, i4);
}
}
return 0;
}
psword2:c2N0Zl85MS=yMT=yMTAy
5.静态分析第五部分,psword3
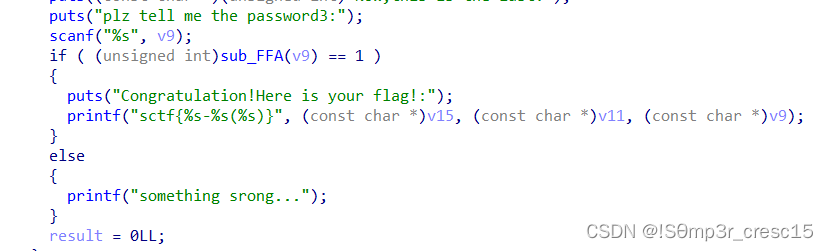
sub_FFA()函数是关键处理函数,跟进

跟进加密函数sub_143B()
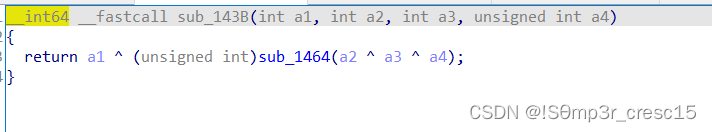
继续跟进
编写wp:
#include <stdio.h>
#include "defs.h"
unsigned int ROR4(unsigned int x, int y)
{
return (x << (32 - y) | x >> y) & 0xffffffff;
}
unsigned int ROL4(unsigned int x, int y)
{
return (x >> (32 - y) | x << y) & 0xffffffff;
}
__int64 sub_1464(unsigned int a1)
{
int v2;
unsigned int v3[288] = {
0xD6, 0x90, 0xE9, 0xFE, 0xCC, 0xE1, 0x3D, 0xB7,
0x16, 0xB6, 0x14, 0xC2, 0x28, 0xFB, 0x2C, 0x05,
0x2B, 0x67, 0x9A, 0x76, 0x2A, 0xBE, 0x04, 0xC3,
0xAA, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99,
0x9C, 0x42, 0x50, 0xF4, 0x91, 0xEF, 0x98, 0x7A,
0x33, 0x54, 0x0B, 0x43, 0xED, 0xCF, 0xAC, 0x62,
0xE4, 0xB3, 0x1C, 0xA9, 0xC9, 0x08, 0xE8, 0x95,
0x80, 0xDF, 0x94, 0xFA, 0x75, 0x8F, 0x3F, 0xA6,
0x47, 0x07, 0xA7, 0xFC, 0xF3, 0x73, 0x17, 0xBA,
0x83, 0x59, 0x3C, 0x19, 0xE6, 0x85, 0x4F, 0xA8,
0x68, 0x6B, 0x81, 0xB2, 0x71, 0x64, 0xDA, 0x8B,
0xF8, 0xEB, 0x0F, 0x4B, 0x70, 0x56, 0x9D, 0x35,
0x1E, 0x24, 0x0E, 0x5E, 0x63, 0x58, 0xD1, 0xA2,
0x25, 0x22, 0x7C, 0x3B, 0x01, 0x21, 0x78, 0x87,
0xD4, 0x00, 0x46, 0x57, 0x9F, 0xD3, 0x27, 0x52,
0x4C, 0x36, 0x02, 0xE7, 0xA0, 0xC4, 0xC8, 0x9E,
0xEA, 0xBF, 0x8A, 0xD2, 0x40, 0xC7, 0x38, 0xB5,
0xA3, 0xF7, 0xF2, 0xCE, 0xF9, 0x61, 0x15, 0xA1,
0xE0, 0xAE, 0x5D, 0xA4, 0x9B, 0x34, 0x1A, 0x55,
0xAD, 0x93, 0x32, 0x30, 0xF5, 0x8C, 0xB1, 0xE3,
0x1D, 0xF6, 0xE2, 0x2E, 0x82, 0x66, 0xCA, 0x60,
0xC0, 0x29, 0x23, 0xAB, 0x0D, 0x53, 0x4E, 0x6F,
0xD5, 0xDB, 0x37, 0x45, 0xDE, 0xFD, 0x8E, 0x2F,
0x03, 0xFF, 0x6A, 0x72, 0x6D, 0x6C, 0x5B, 0x51,
0x8D, 0x1B, 0xAF, 0x92, 0xBB, 0xDD, 0xBC, 0x7F,
0x11, 0xD9, 0x5C, 0x41, 0x1F, 0x10, 0x5A, 0xD8,
0x0A, 0xC1, 0x31, 0x88, 0xA5, 0xCD, 0x7B, 0xBD,
0x2D, 0x74, 0xD0, 0x12, 0xB8, 0xE5, 0xB4, 0xB0,
0x89, 0x69, 0x97, 0x4A, 0x0C, 0x96, 0x77, 0x7E,
0x65, 0xB9, 0xF1, 0x09, 0xC5, 0x6E, 0xC6, 0x84,
0x18, 0xF0, 0x7D, 0xEC, 0x3A, 0xDC, 0x4D, 0x20,
0x79, 0xEE, 0x5F, 0x3E, 0xD7, 0xCB, 0x39, 0x48,
0xC6, 0xBA, 0xB1, 0xA3, 0x50, 0x33, 0xAA, 0x56,
0x97, 0x91, 0x7D, 0x67, 0xDC, 0x22, 0x70, 0xB2,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00
};
v2 = (v3[BYTE2(a1)] << 16) | v3[(unsigned __int8)a1] | (v3[BYTE1(a1)] << 8) | (v3[HIBYTE(a1) ] << 24);
return ROL4(v2, 12) ^ (unsigned int)(ROL4(v2, 8) ^ ROR4(v2, 2)) ^ ROR4(v2, 6);
}
int main()
{
int n = 25;
unsigned int v10[30] = { 0 };
v10[26] = 0xBE040680;
v10[27] = 0xC5AF7647;
v10[28] = 0x9FCC401F;
v10[29] = 0xD8BF92EF;
do
{
v10[n] =v10[n + 4] ^ sub_1464(v10[n + 1] ^ v10[n + 2] ^ v10[n + 3]);
--n;
} while (n >= 0);
for (int i = 0; i < 4; i++)
printf("%c%c%c%c", ((char*)&v10[i])[0], ((char*)&v10[i])[1], ((char*)&v10[i])[2], ((char*)&v10[i])[3]);
return 0;
}
psword3:fl4g_is_s0_ug1y!
6.根据psword1~3整理出flag
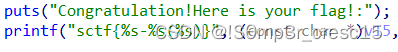
可以知道flag的格式为sctf{%s-%s(%s)}
flag{ddwwxxssxaxwwaasasyywwdd-c2N0Zl85MTAy(fl4g_is_s0_ug1y!)}
版权归原作者 御麟蹬辉 所有, 如有侵权,请联系我们删除。
