概念
IPSec是一个框架,它不是具体指某个协议,而是定义了一个框架,由各种协议组和协商而成。该框架涉及到的主要有加密算法、验证算法、封装协议、封装模式、密钥有效期等等。
IPSecVPN建立的前提:要想在两个站点之间安全的传输IP数据流,它们之间必须要先进行协商,协商它们之间所采用的加密算法,封装技术以及密钥。
分为两个阶段,第一个是建立管理连接,第二个阶段是建立数据连接
阶段一:
在两个对等体设备之间建立一个安全的管理连接。没有实际的数据通过这个连接。这个管理连接是用来保护第二阶段协商过程的。
阶段一需要协商的内容:
1.双方使用什么加密算法进行加密(des、3des、aes)
2.摘要(完整性)认证的方式(MD5、SHA)
3.采用的密钥共享方式(预共享密钥,CA数字签名、公钥认证)
4.使用的密钥强度DH组(越大加密强度越高)
5.管理连接生存时间(默认一天,单位秒)
6.协商模式(主模式或积极模式)
阶段二:
当对等体之间有了安全的管理连接之后,它们就可以接着协商用于构建安全数据连接的安全参数,这个协商过程是安全的,加密的。协商完成后,将在两个站点间形成安全的数据连接。
阶段二需要协商的内容:
1.传输模式(隧道模式还是传输模式)
2.封装技术(ESP、AH)
3.传输过程中数据的加密方式(des、3des、aes)
4.传输过程中数据的认证方式(MD5、SHA)
3.定义感兴趣(定义需要使用IPSec的流量)
IPSec的配置实验
拓扑图

先进行基配置,保证路由可达
AR1
<Huawei>sys
Enter system view, return user view with Ctrl+Z.
[Huawei]sys ar1
[ar1]int g0/0/0
[ar1-GigabitEthernet0/0/0]ip add 192.168.1.254 24
Sep 8 2022 15:22:35-08:00 ar1 %%01IFNET/4/LINK_STATE(l)[1]:The line protocol IP
on the interface GigabitEthernet0/0/0 has entered the UP state.
[ar1-GigabitEthernet0/0/0]
[ar1-GigabitEthernet0/0/0]int g0/0/1
[ar1-GigabitEthernet0/0/1]ip add 12.1.1.1 24
Sep 8 2022 15:23:06-08:00 ar1 %%01IFNET/4/LINK_STATE(l)[2]:The line protocol IP
on the interface GigabitEthernet0/0/1 has entered the UP state.
[ar1-GigabitEthernet0/0/1]quit
[ar1]ip rou
[ar1]ip route
[ar1]ip route-static 0.0.0.0 0 12.1.1.2
AR2
<Huawei>sys
Enter system view, return user view with Ctrl+Z.
[Huawei]sys ar2
[ar2]int g0/0/0
[ar2-GigabitEthernet0/0/0]ip add 12.1.1.2 24
Sep 8 2022 15:23:55-08:00 ar2 %%01IFNET/4/LINK_STATE(l)[0]:The line protocol IP
on the interface GigabitEthernet0/0/0 has entered the UP state.
[ar2-GigabitEthernet0/0/0]int g0/0/1
[ar2-GigabitEthernet0/0/1]ip add 23.1.1.2 24
Sep 8 2022 15:24:05-08:00 ar2 %%01IFNET/4/LINK_STATE(l)[1]:The line protocol IP
on the interface GigabitEthernet0/0/1 has entered the UP state.
[ar2-GigabitEthernet0/0/1]quit
[ar2]
[ar2]ip rou
[ar2]ip route
[ar2]ip route-static 172.16.1.0 24 23.1.1.3
[ar2]ip rou
[ar2]ip route
[ar2]ip route-static 192.168.1.0 24 12.1.1.1
AR3
<Huawei>sys
Enter system view, return user view with Ctrl+Z.
[Huawei]sys ar3
[ar3]int g0/0/0
[ar3-GigabitEthernet0/0/0]ip add 172.16.1.254 24
Sep 8 2022 15:24:55-08:00 ar3 %%01IFNET/4/LINK_STATE(l)[0]:The line protocol IP
on the interface GigabitEthernet0/0/0 has entered the UP state.
[ar3-GigabitEthernet0/0/0]int g0/0/1
[ar3-GigabitEthernet0/0/1]ip add 23.1.1.3 24
Sep 8 2022 15:25:11-08:00 ar3 %%01IFNET/4/LINK_STATE(l)[1]:The line protocol IP
on the interface GigabitEthernet0/0/1 has entered the UP state.
[ar3-GigabitEthernet0/0/1]quit
[ar3]ip route-static 0.0.0.0 0 23.1.1.2
测试连通性

配置阶段一
配置ike提案
[ar1]ike proposal 1
[ar1-ike-proposal-1]encryption-algorithm aes-cbc-256
[ar1-ike-proposal-1]authentication-algorithm sha1
[ar1-ike-proposal-1]authentication-method pre-share
[ar1-ike-proposal-1]dh group14
[ar1-ike-proposal-1]sa duration 1200
[ar1-ike-proposal-1]quit
AR3
[ar3]ike proposal 1
[ar3-ike-proposal-1]encryption-algorithm aes-cbc-256
[ar3-ike-proposal-1]authentication-algorithm sha1
[ar3-ike-proposal-1]authentication-method pre
[ar3-ike-proposal-1]authentication-method pre-share
[ar3-ike-proposal-1]dh group14
[ar3-ike-proposal-1]sa duration 1200
[ar3-ike-proposal-1]quit
配置ike邻居
[ar1]ike peer 1 v2
[ar1-ike-peer-1]remote-address 23.1.1.3
[ar1-ike-peer-1]pre-shared-key s
[ar1-ike-peer-1]pre-shared-key simple 123456789
[ar1-ike-peer-1]ike-proposal 1
[ar1-ike-peer-1]quit
[ar3]ike peer 1 v2
[ar3-ike-peer-1]remote-address 12.1.1.1
[ar3-ike-peer-1]pre-shared-key simple 123456789
[ar3-ike-peer-1]ike-proposal 1
配置阶段二
定义感兴趣流
高级acl,需要从进行IPSecVPN的流量
[ar1]acl 3000
[ar1-acl-adv-3000]rule permit ip source 192.168.1.0 0.0.0.255 destination 172.16
.1.0 0.0.0.255
[ar1-acl-adv-3000]quit
[ar3]acl 3000
[ar3-acl-adv-3000]rule permit ip source 172.16.1.0 0.0.0.255 destination 192.168
.1.0 0.0.0.255
[ar3-acl-adv-3000]quit
定义IPSec提案
[ar1]ipsec proposal 1
[ar1-ipsec-proposal-1]encapsulation-mode tunnel
[ar1-ipsec-proposal-1]esp authentication-algorithm sha1
[ar1-ipsec-proposal-1]esp encryption-algorithm aes-256
[ar1-ipsec-proposal-1]quit
[ar3]ipsec proposal 1
[ar3-ipsec-proposal-1]encapsulation-mode tunnel
[ar3-ipsec-proposal-1]esp encryption-algorithm aes-256
[ar3-ipsec-proposal-1]esp authentication-algorithm sha1
[ar3-ipsec-proposal-1]quit
IPsec 策略
[ar1]ipsec policy 1 1 isakmp
[ar1-ipsec-policy-isakmp-1-1]security acl 3000
[ar1-ipsec-policy-isakmp-1-1]proposal 1
[ar1-ipsec-policy-isakmp-1-1]ike-peer 1
[ar3]ipsec policy 1 1 isakmp
[ar3-ipsec-policy-isakmp-1-1]security acl 3000
[ar3-ipsec-policy-isakmp-1-1]proposal 1
[ar3-ipsec-policy-isakmp-1-1]ike-peer 1
把ipsec策略应用到接口
[ar1]int g0/0/1
[ar1-GigabitEthernet0/0/1]ipsec policy 1
[ar3]int g0/0/1
[ar3-GigabitEthernet0/0/1]ipsec policy 1
结果测试
pc2 ping pc1

在AR1和AR2之间抓包

可以看出IPsec的数据包和普通的ICMP还是有很大不同的,这里面的数据被进行了加密
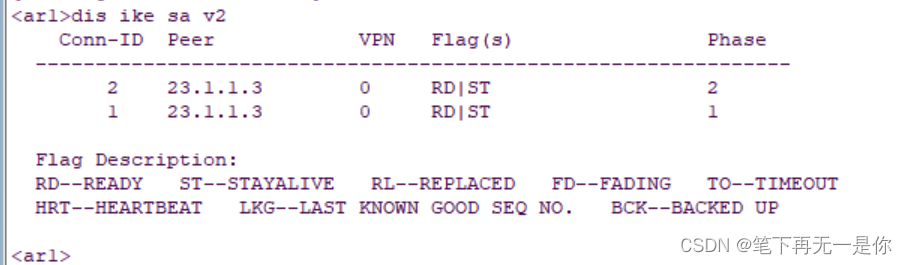
在AR1上查询阶段一的连接
再查询一下阶段二

简单的IPSecVPN实验就配置完成了,如有错误,欢迎指出!!!
版权归原作者 笔下再无一是你 所有, 如有侵权,请联系我们删除。