文章目录
新人赛,就没有存题目附件了,简单的记录一下解题过程吧
Level - Week1
WEB
easy_auth
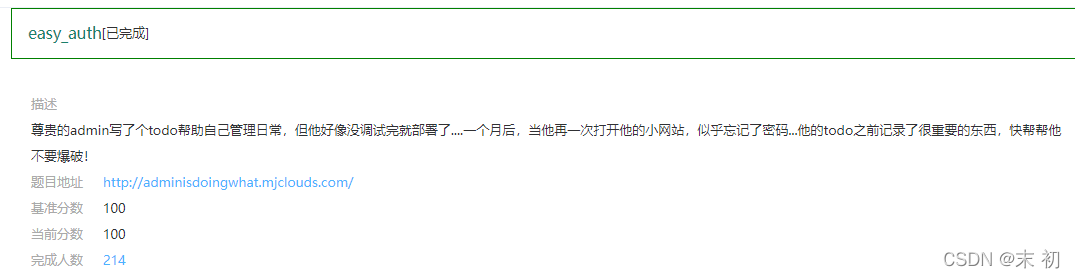
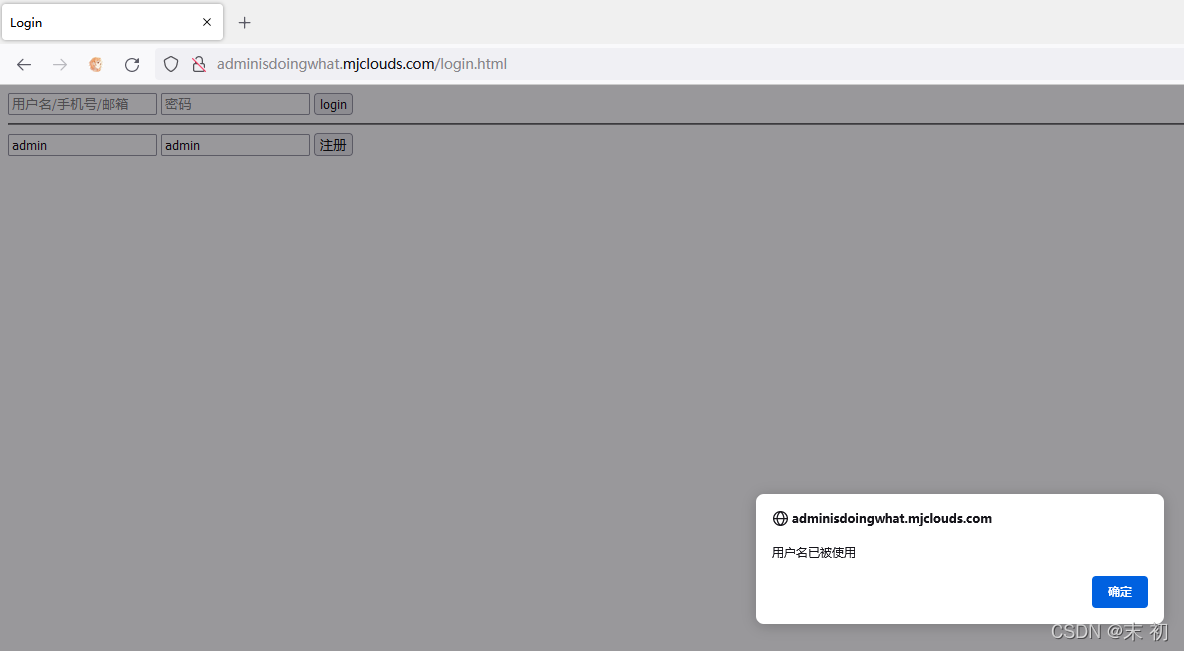
存在
admin
用户,随便设置一个任务,然后点击
doing
,抓一个
GET
的包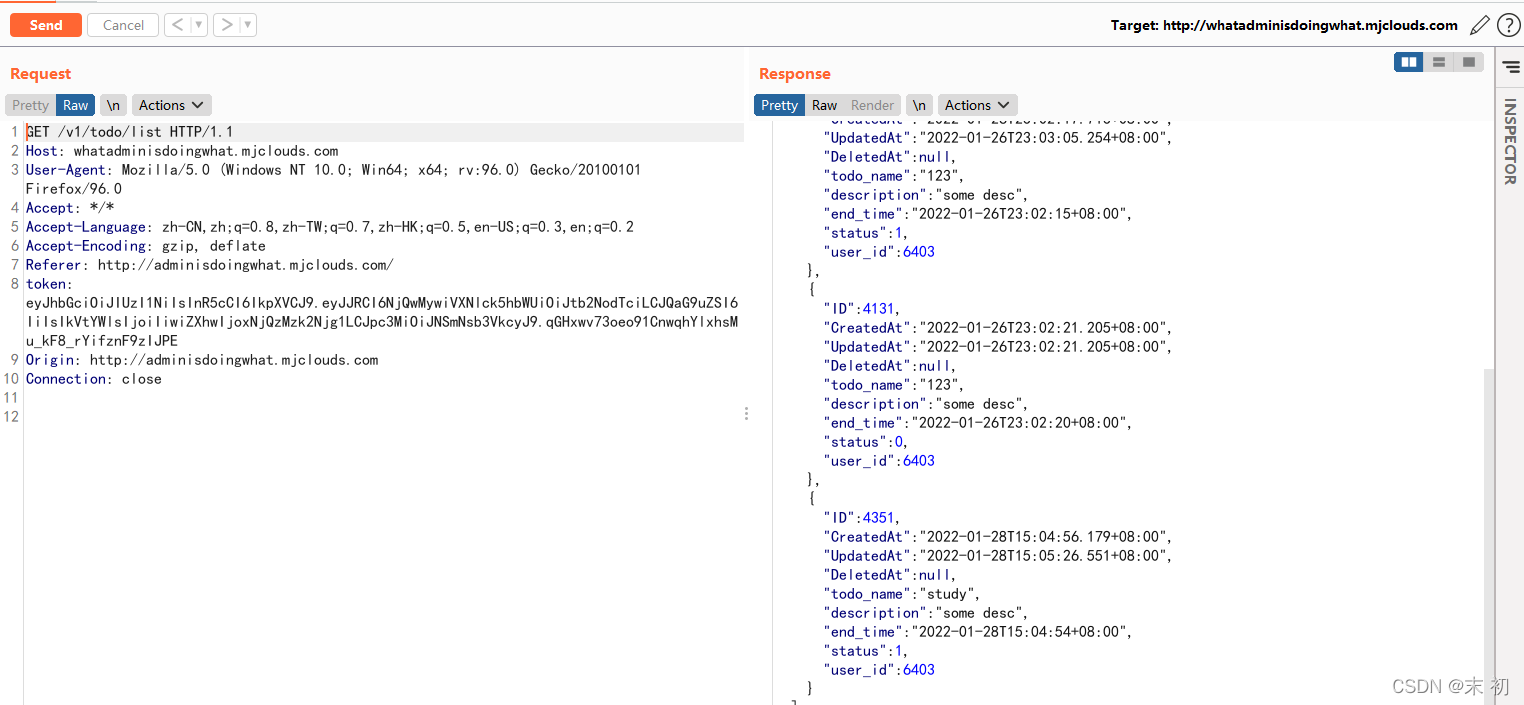
Token的格式很明显是
jwt
:https://jwt.io/
修改
ID
为
1
,
Username
为
admin
发送修改后的
jwt
密文得到flag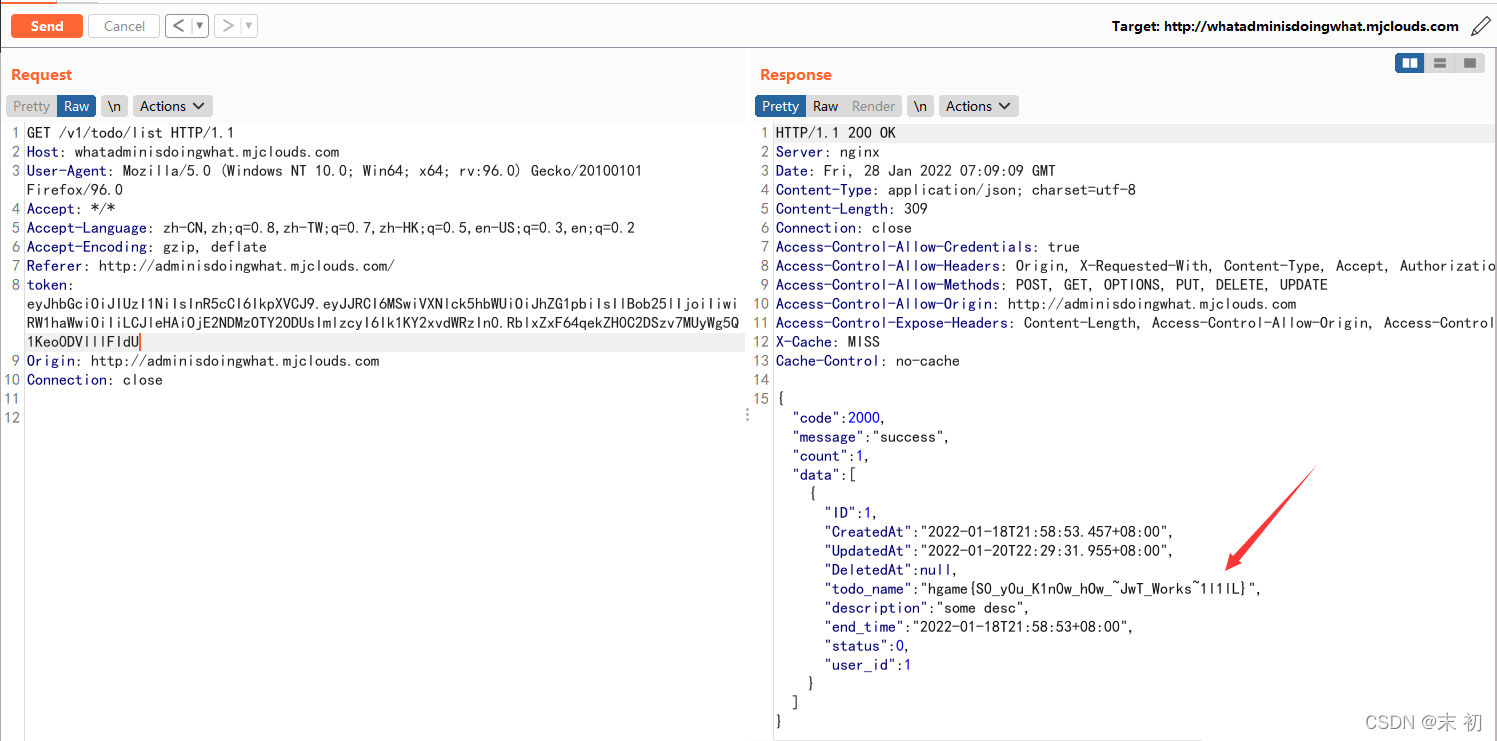
蛛蛛…嘿嘿♥我的蛛蛛

import requests
import re
init_url ="https://hgame-spider.vidar.club/8983cb3acd"
link =""whileTrue:
res_url = init_url + link
regex = re.compile('href="(.*?)"')
html = requests.get(url=res_url)
l = re.findall(regex, html.text)print(res_url)
link =[i for i in l if i !='']iflen(link)==0:breakelse:
link = link[0]
访问最后一个输出的地址,flag在响应头里面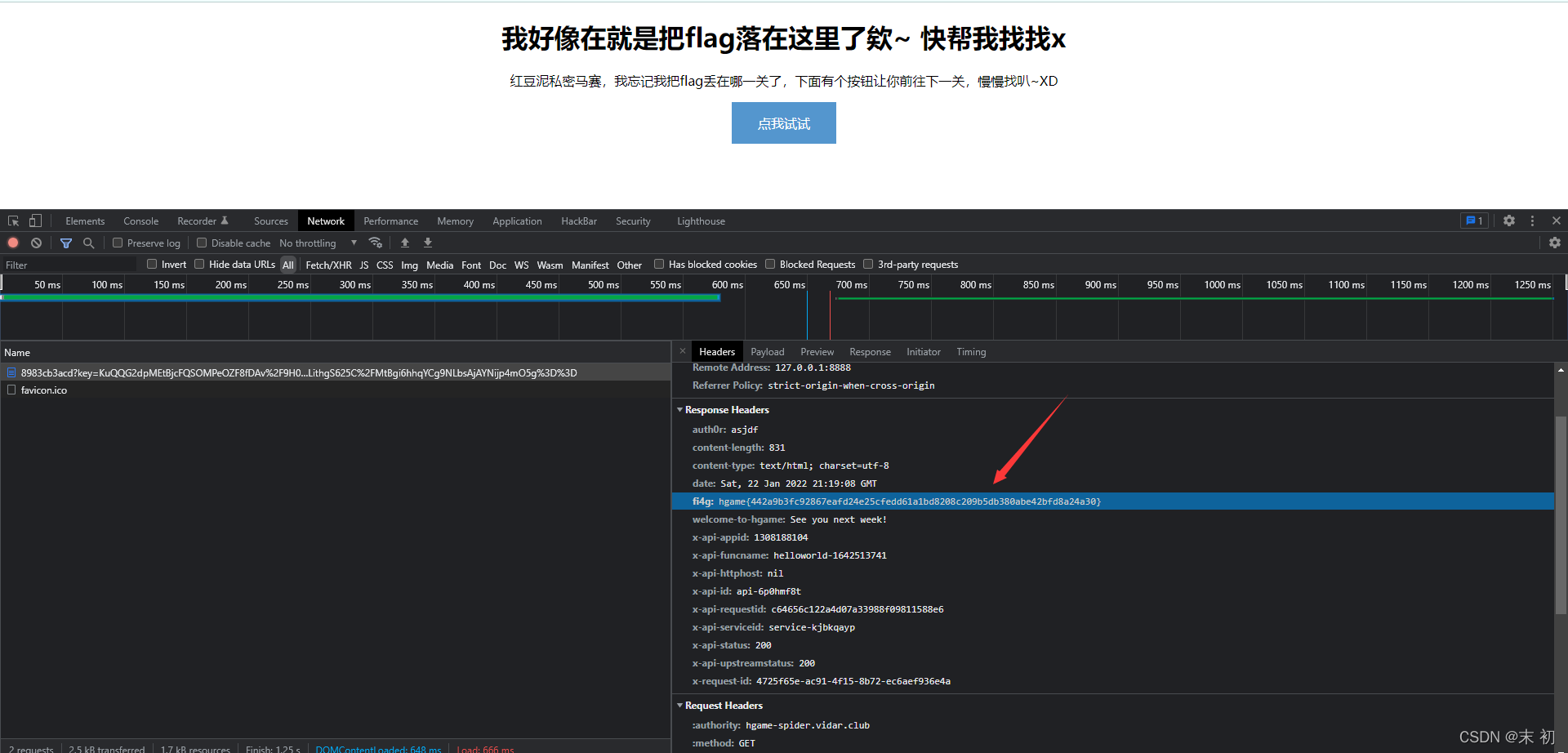
Tetris plus

在
cheking.js
中发现注释了
jsfuck
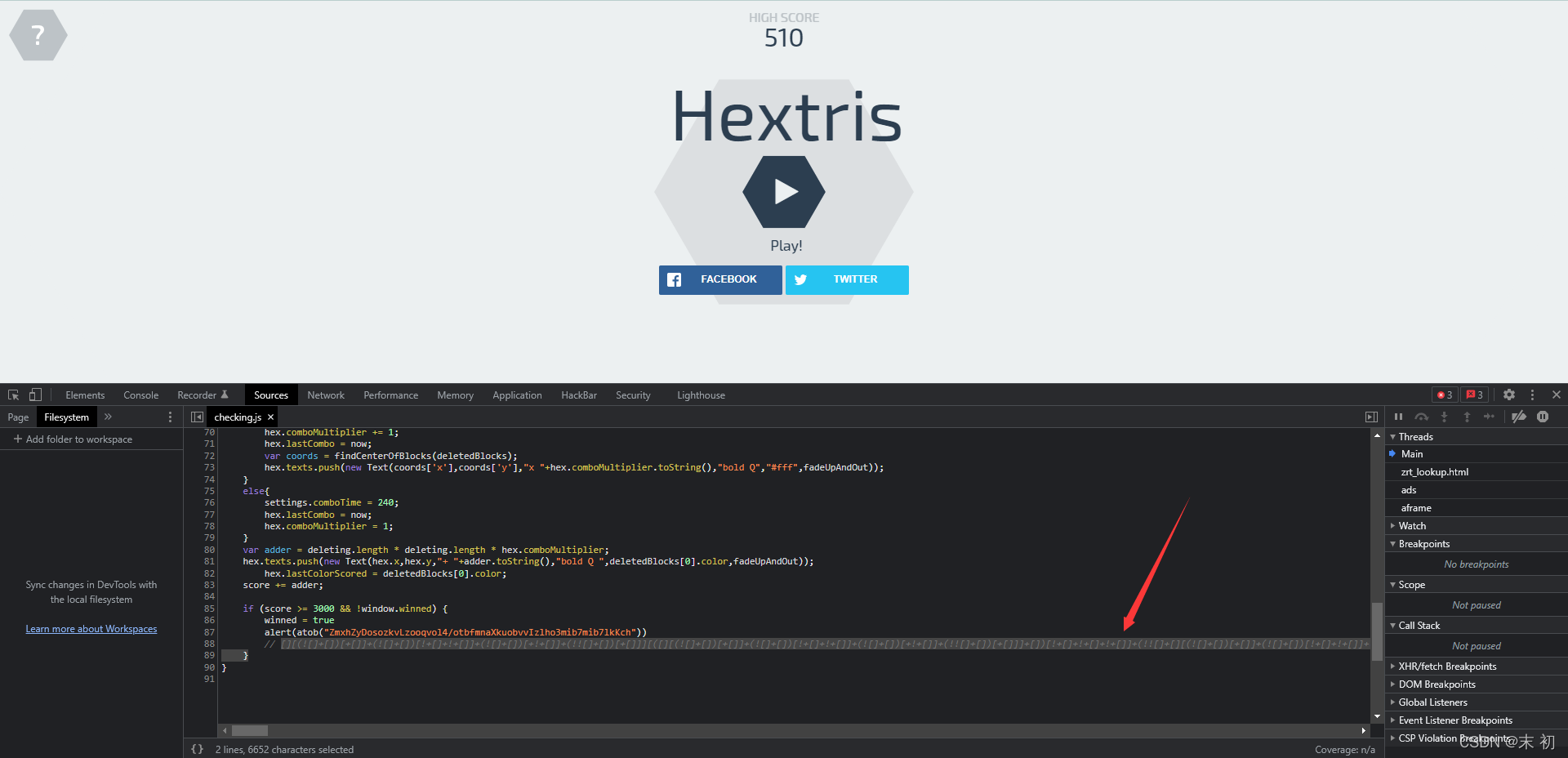
直接复制到控制台回车即可得到flag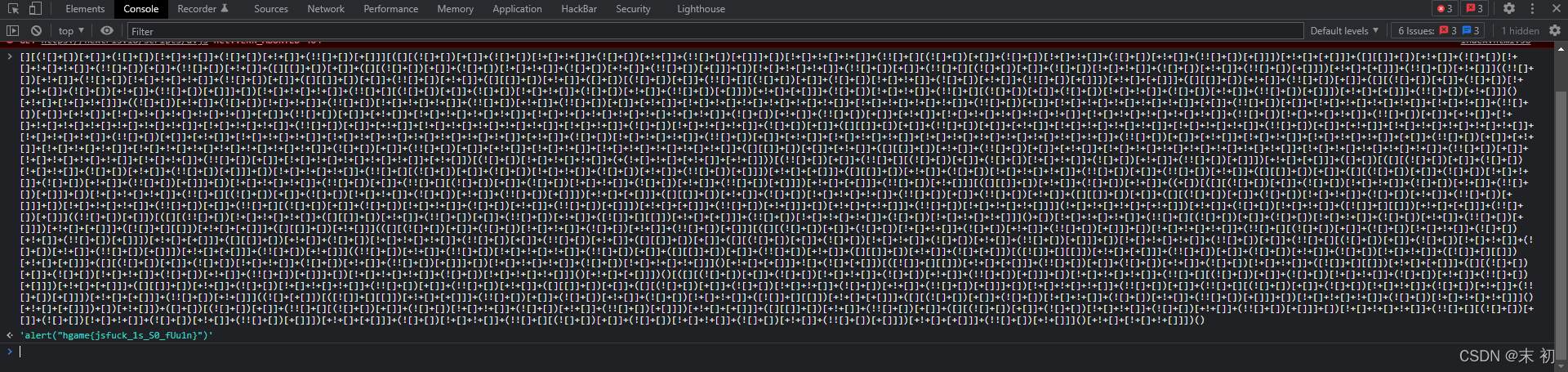
Fujiwara Tofu Shop

GET / HTTP/1.1
Host: shop.summ3r.top
User-Agent: Hachi-Roku
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
referer:qiumingshan.net
Cookie: flavor=Raspberry;
gasoline:100
x-real-ip:127.0.0.1
Connection: close
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0

MISC
欢迎欢迎!热烈欢迎!

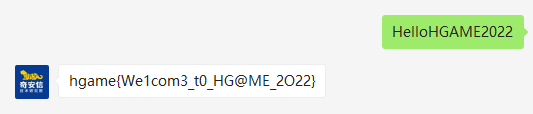
hgame{We1com3_t0_HG@ME_2O22}
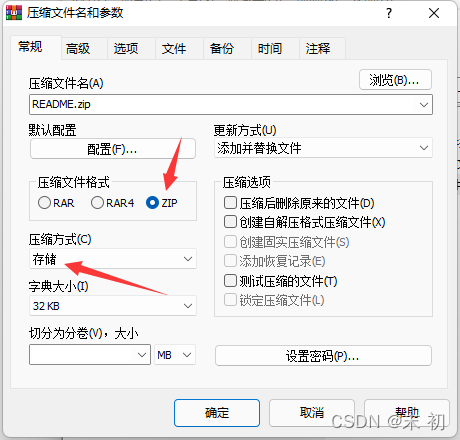
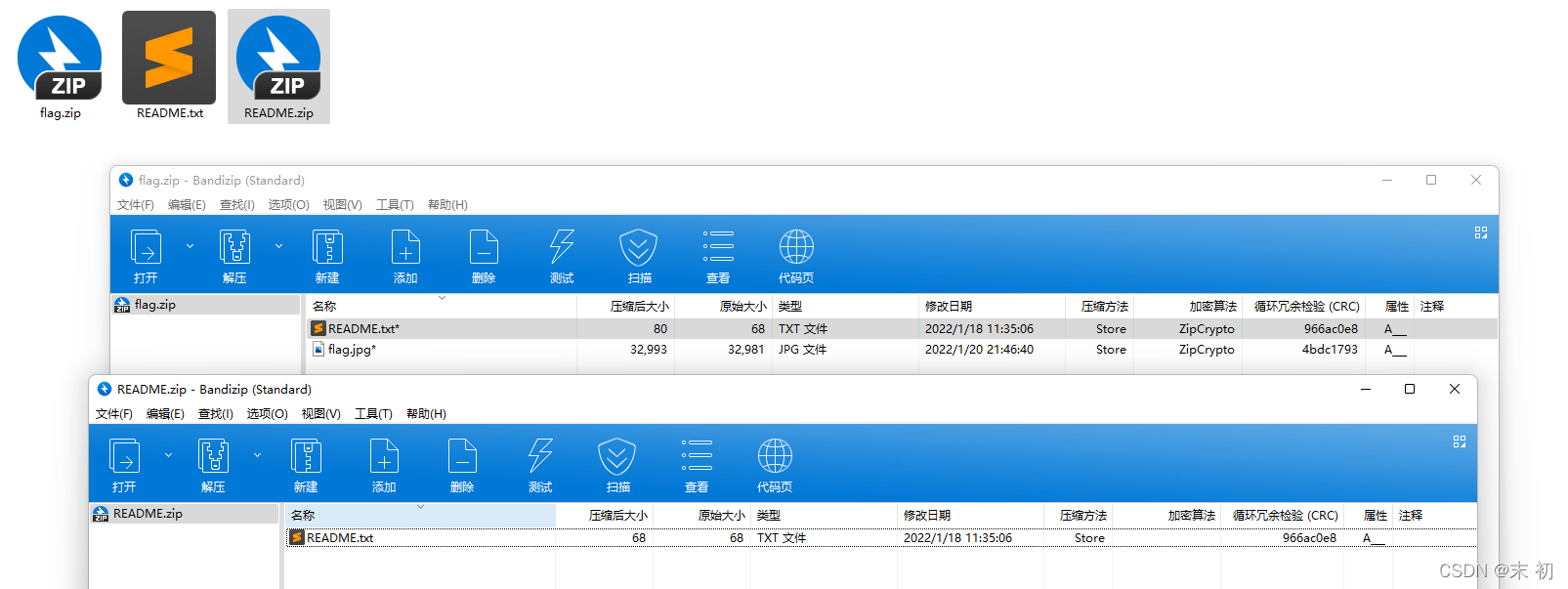
这个压缩包有点麻烦
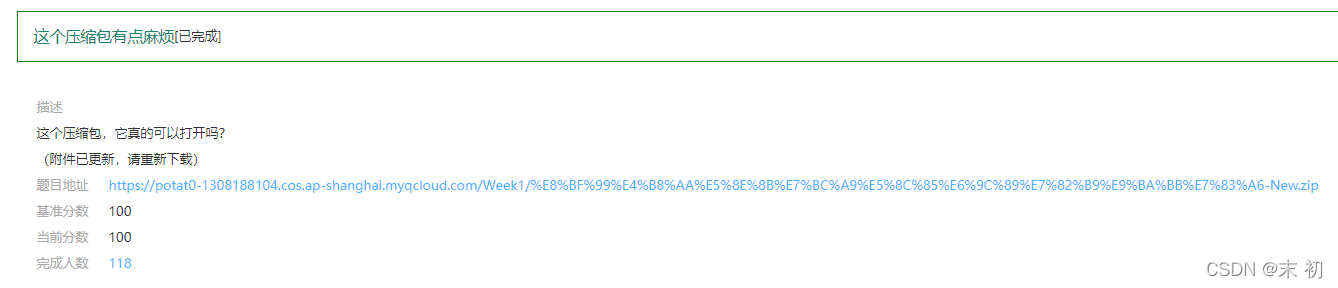
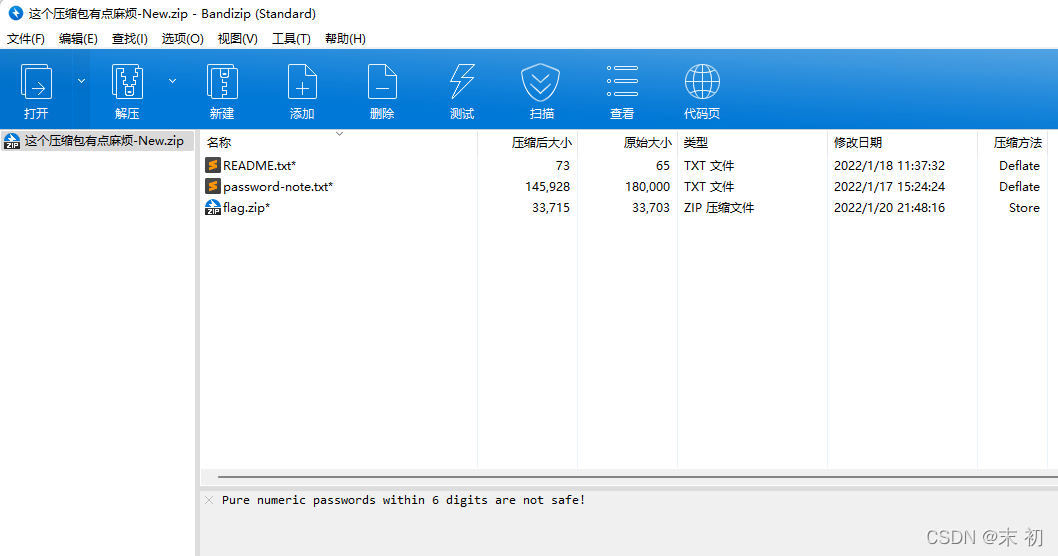
README.txt
I don't know if it's a good idea to write down all the passwords.
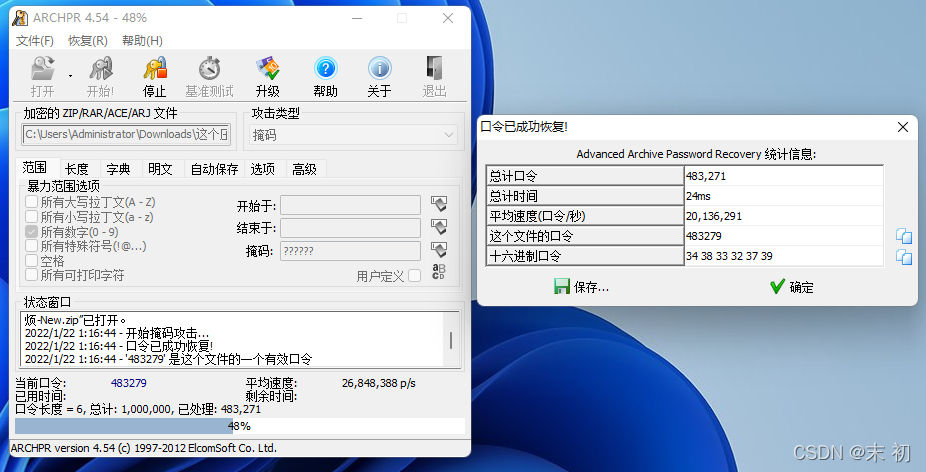
将
password-note.txt
作为字典进行爆破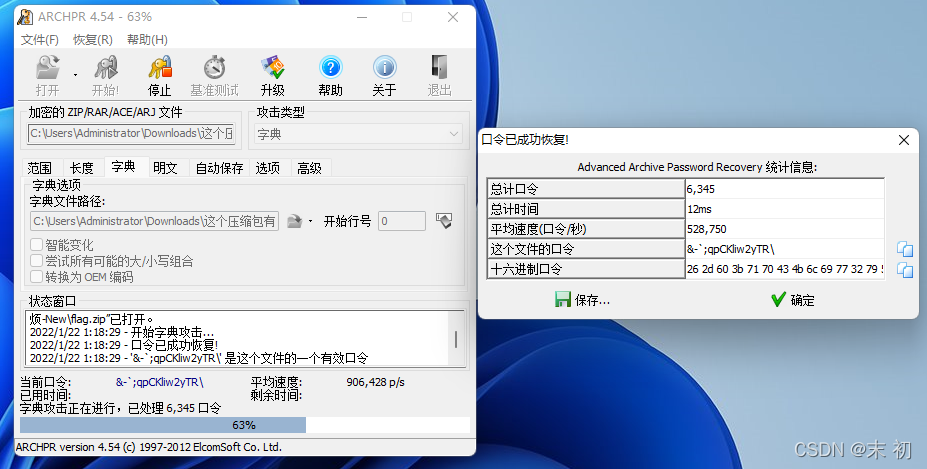
明文攻击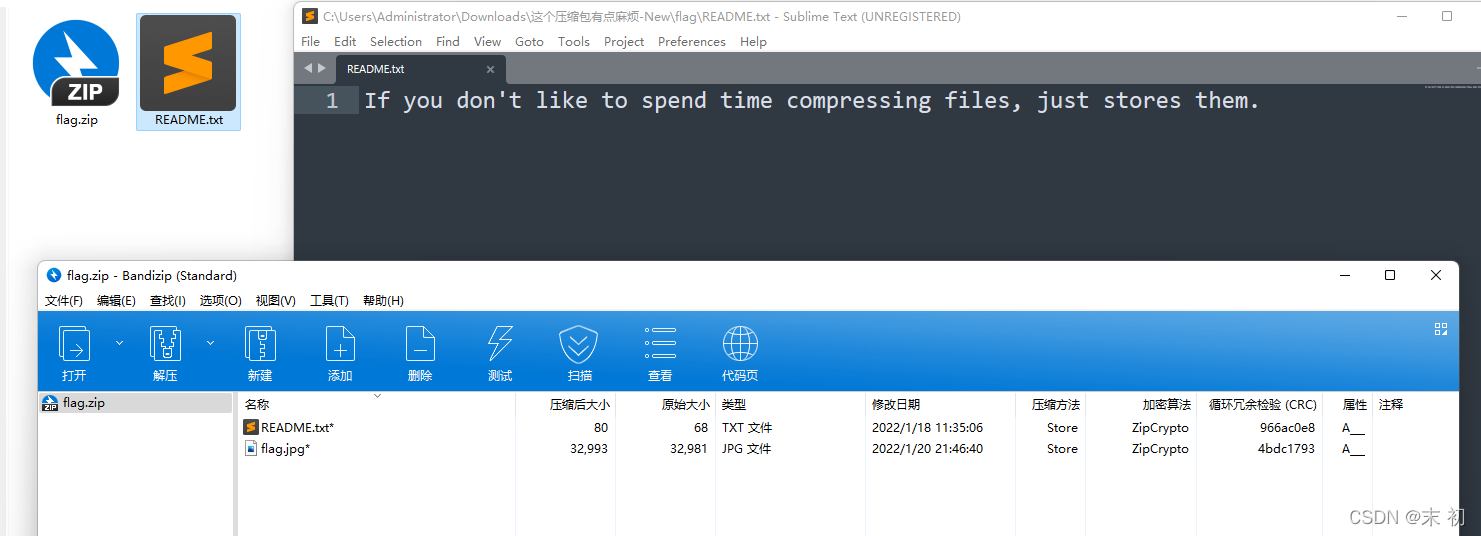

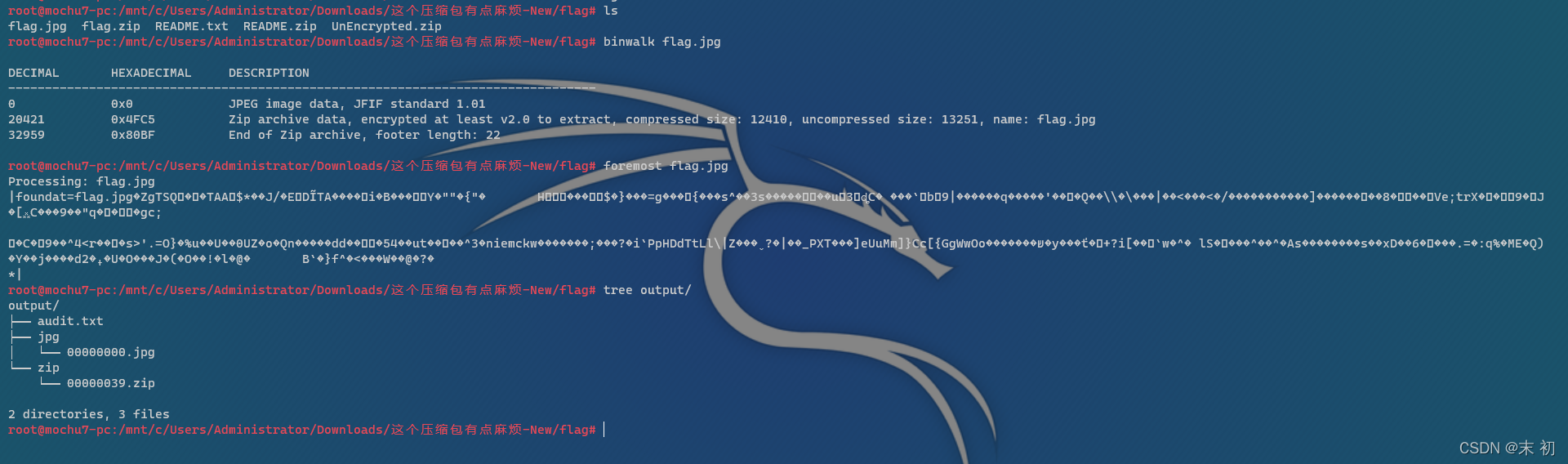
分离出来的压缩包跟一般伪加密不同的是修改了
压缩源文件数据区的全局方式标记位
,使得
7z
等压缩包无法无视伪加密直接解压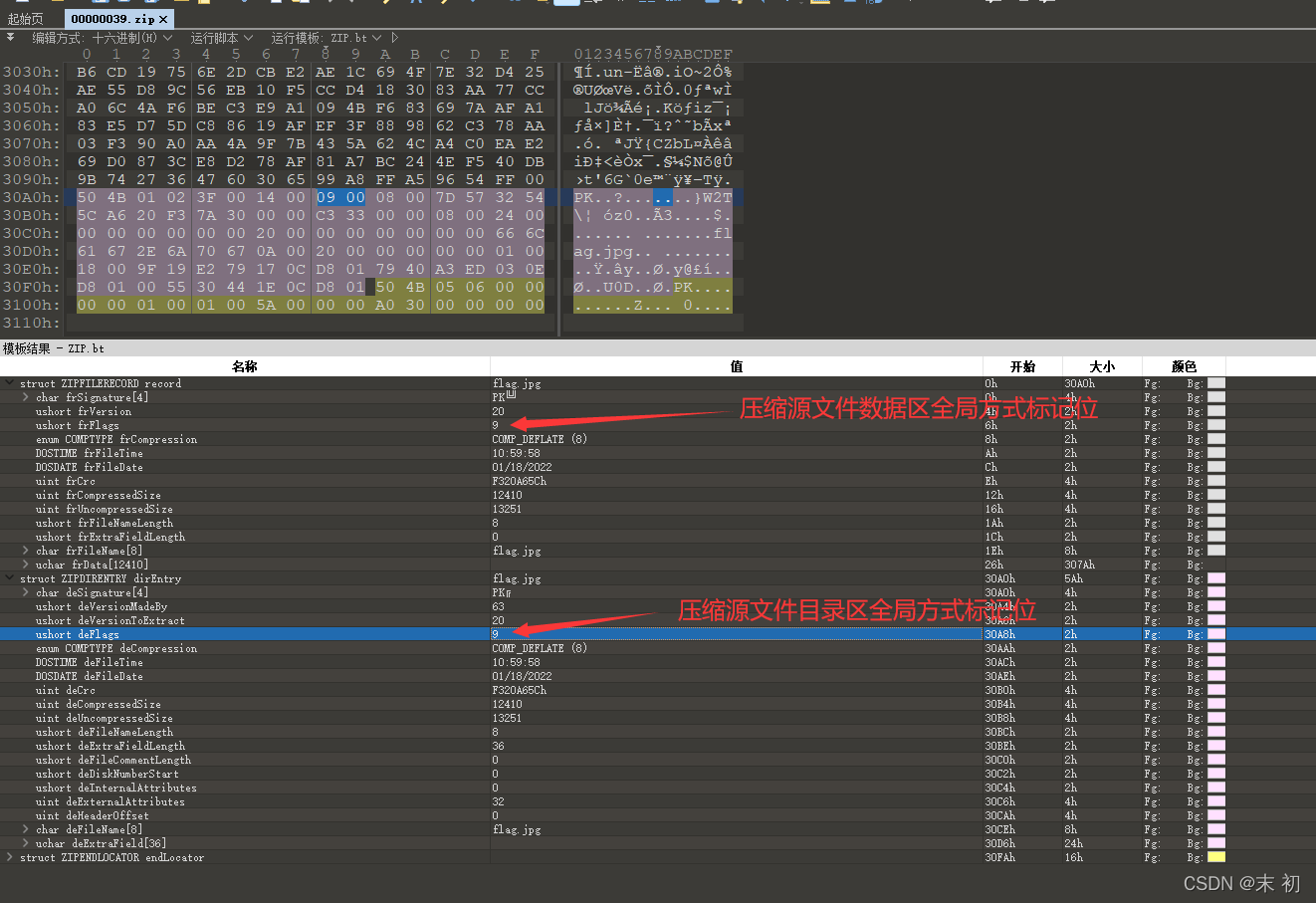
修改
压缩源文件目录区全局方式标记位
为偶数即可
hgame{W0w!_y0U_Kn0w_z1p_3ncrYpt!}
好康的流量
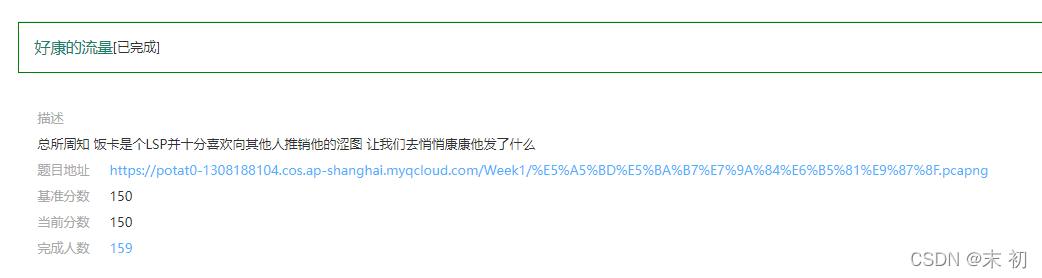
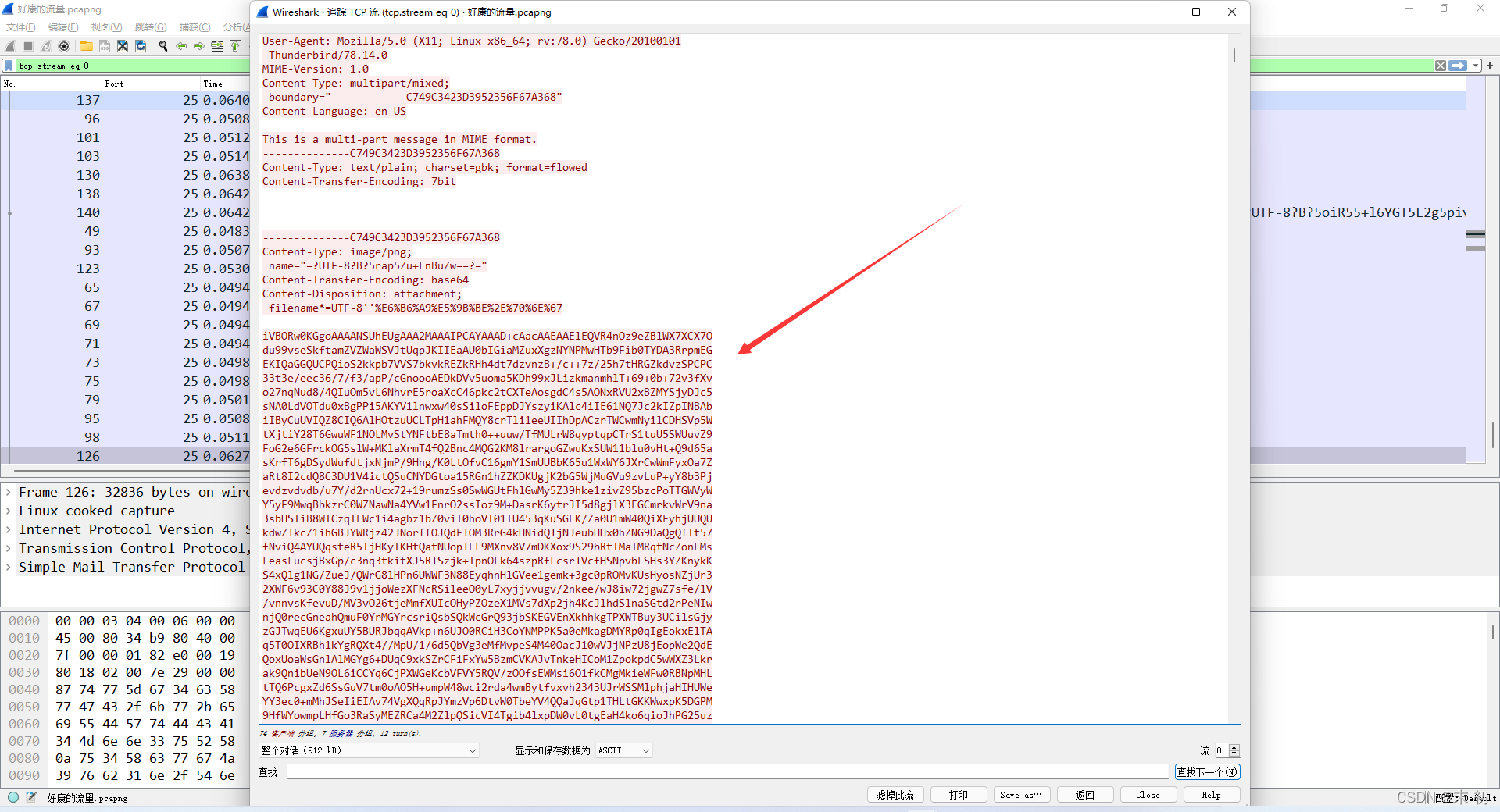


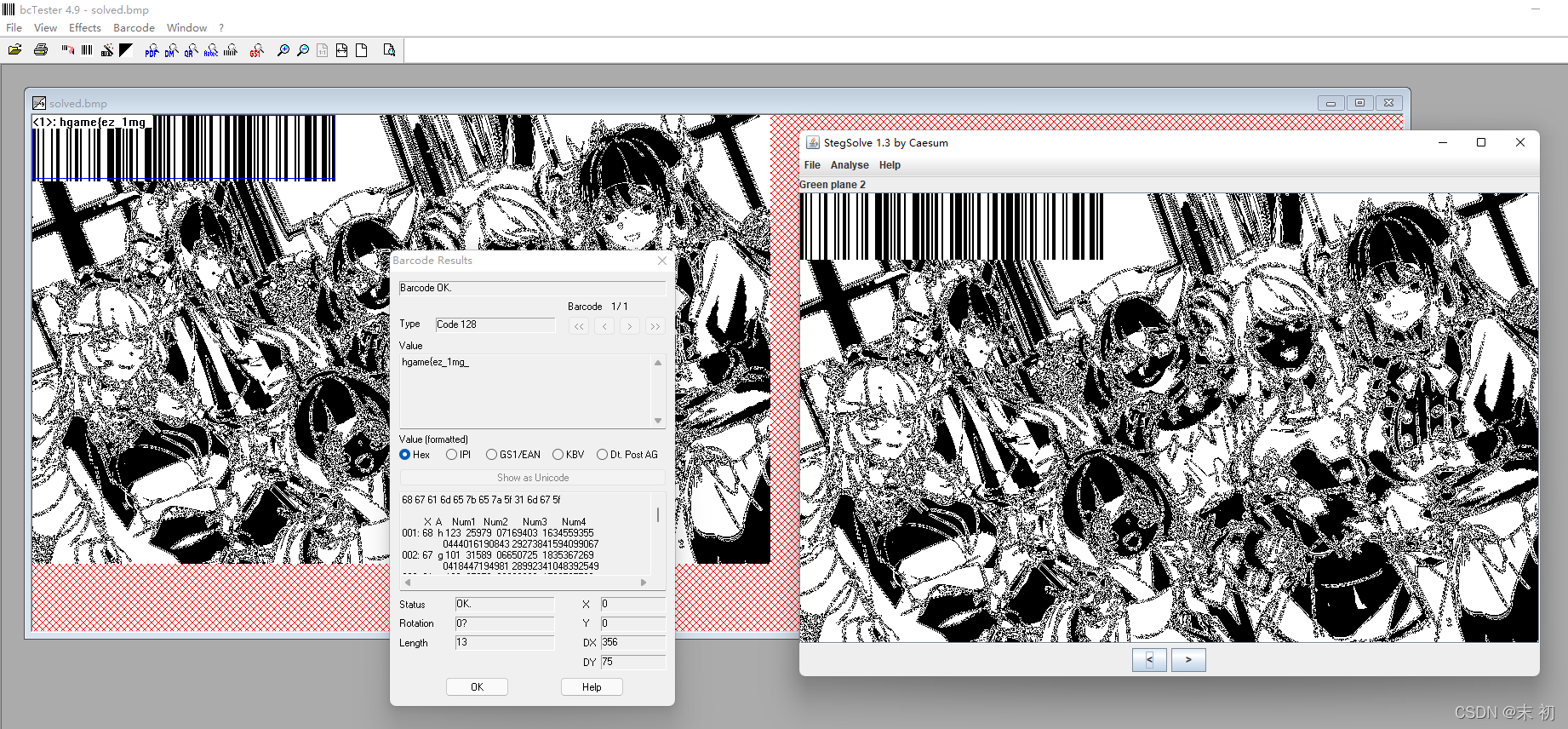
hgame{ez_1mg_
另一半flag用
zsteg
查看一下LSB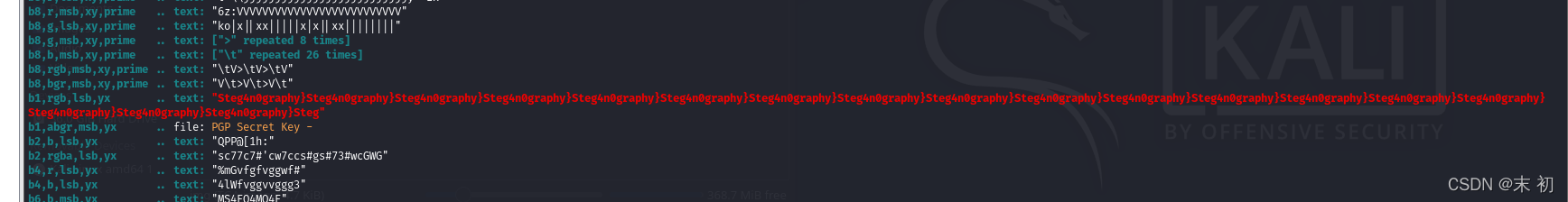
hgame{ez_1mg_Steg4n0graphy}
群青(其实是幽灵东京)

通过频谱图得到密码:
Yoasobi

音频LSB隐写,
SlientEye
解码得到一个地址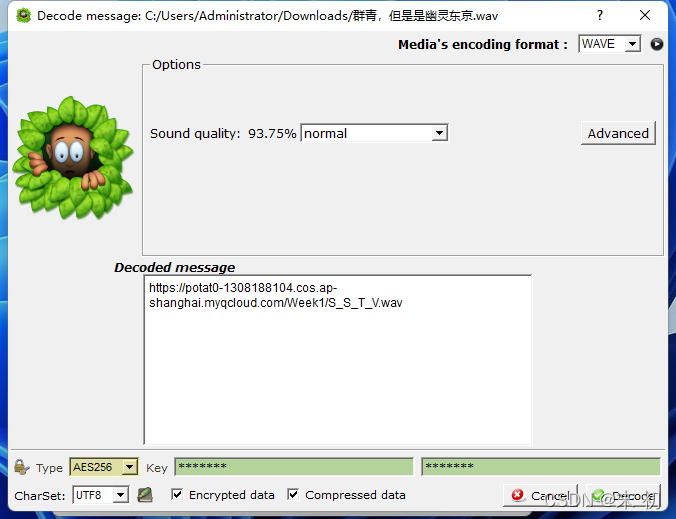
听起来是SSTV,
Robot36
直接听

hgame{1_c4n_5ee_the_wav}
CRYPTO
Dancing Line

向
X
轴方向移动一个像素点记为
0
,向
Y
轴方向移动一个像素点记为
1
from PIL import Image
img = Image.open('flag.bmp')
width, height = img.size
bin_data =''
num_list =[]
n =0for w inrange(width):for h inrange(height):
pix = img.getpixel((w,h))if pix !=(255,255,255):#print("{} {}".format(pix, n))
num_list.append(n)
n +=1for i inrange(len(num_list)-1):if(num_list[i+1]- num_list[i])>= height:
bin_data +='0'else:
bin_data +='1'print("[+]binary data: {}".format(bin_data))
flag =''for i inrange(0,len(bin_data),8):
flag +=chr(int(bin_data[i:i+8],2))print(flag)
PS C:\Users\Administrator\Downloads> python .\code.py
[+]binary data: 01101000011001110110000101101101011001010111101101000100011000010110111001100011001100010110111001100111010111110100110000110001011011100110010101011111001100010011010101011111011001100111010101101110001011000101111100110001001101010110111000100111011101000101111100110001011101000011111101111101
hgame{Danc1ng_L1ne_15_fun,_15n't_1t?}
Matryoshka

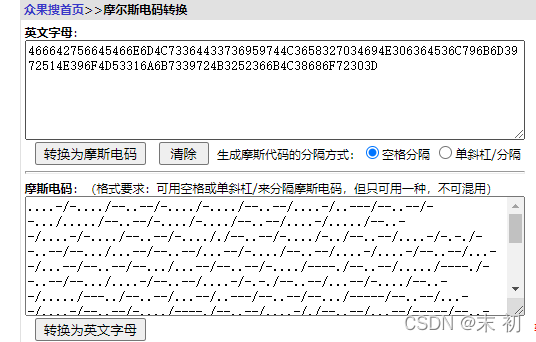
类似盲文,但是其实是摩斯码
- 将
⠨替换为. - 将
⠤替换为- - 将
⠌替换为/
然后逆序处理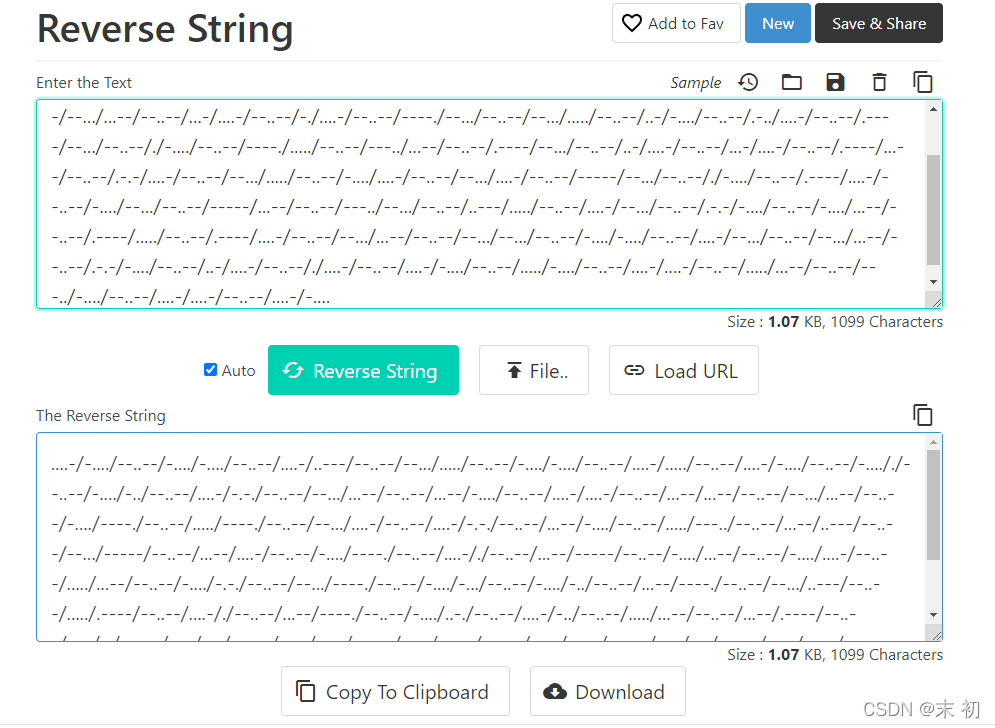
466642756645466E6D4C73364433736959744C3658327034694E306364536C796B6D3972514E396F4D53316A6B7339724B3252366B4C38686F72303D
Hex转字符得到:
FfBufEFnmLs6D3siYtL6X2p4iN0cdSlykm9rQN9oMS1jks9rK2R6kL8hor0=
维吉尼亚解密(密钥为:hgame)得到:
YzBibXZnaHl6X3swUmF6X2d4eG0wdGhrem9fMG9iMG1fdm9rY2N6dF8hcn0=
base64解码得到:
c0bmvghyz_{0Raz_gxxm0thkzo_0ob0m_vokcczt_!r}
栅栏密码(每组字数:22)得到:
cbvhz{Rzgx0hz_o0_ocz_r0mgy_0a_xmtko0bmvkct!}
凯撒密码解密(位移21)得到:
hgame{Welc0me_t0_the_w0rld_0f_crypt0graphy!}
English Novel
根据给出的密文,明文,以及加密算法,推出key,然后利用key解
flag.enc
import os
defif_length(ori_content, enc_content, match_result):iflen(ori_content)==len(enc_content):
match_result =Trueelse:
match_result =Falsereturn match_result
defif_match(ori_name, enc_name):
match_result =True
ori_path = ori_folder +'/'+ ori_name
enc_path = enc_folder +'/'+ enc_name
withopen(ori_path,'r')as f:
ori_content = f.read()withopen(enc_path,'r')as f:
enc_content = f.read()
match_result =Trueif match_result:
match_result = if_length(ori_content, enc_content, match_result)if match_result:for i inrange(len(ori_content)):if ori_content[i]== enc_content[i]:continueelif ori_content[i].isupper()and enc_content[i].isupper():continueelif ori_content[i].islower()and enc_content[i].islower():continueelse:
match_result =Falsereturn match_result
defmatch_process(ori_folder, enc_folder):
all_match =[]
original_list = os.listdir(ori_folder)
encrypt_list = os.listdir(enc_folder)for ori_name in original_list:for enc_name in encrypt_list:
match_result = if_match(ori_name, enc_name)if match_result:
ori_path = ori_folder +'/'+ ori_name
enc_path = enc_folder +'/'+ enc_name
match_group =[ori_path, enc_path]
all_match.append(match_group)
encrypt_list.remove(enc_name)else:continuereturn all_match
defdecrypt(ori_data, enc_data, enc_flag):
keys =[]for i inrange(len(enc_data)):
key =ord(enc_data[i])-ord(ori_data[i])
keys.append(key)
result =""
enc_data = enc_flag
for i inrange(len(enc_data)):if enc_data[i].isupper():
result +=chr((ord(enc_data[i])-ord('A')- keys[i])%26+ord('A'))elif enc_data[i].islower():
result +=chr((ord(enc_data[i])-ord('a')- keys[i])%26+ord('a'))else:
result += enc_data[i]return result
if __name__ =='__main__':
ori_folder ='./original'
enc_folder ='./encrypt'
enc_flag =open('./flag.enc','r').read()
match_list = match_process(ori_folder, enc_folder)for match_group in match_list:withopen(match_group[0],'r')as f:
ori_data = f.read()withopen(match_group[1],'r')as f:
enc_data = f.read()
flag = decrypt(ori_data, enc_data, enc_flag)print("{:<30}{:<30}{:<30}".format(match_group[0], match_group[1], flag))
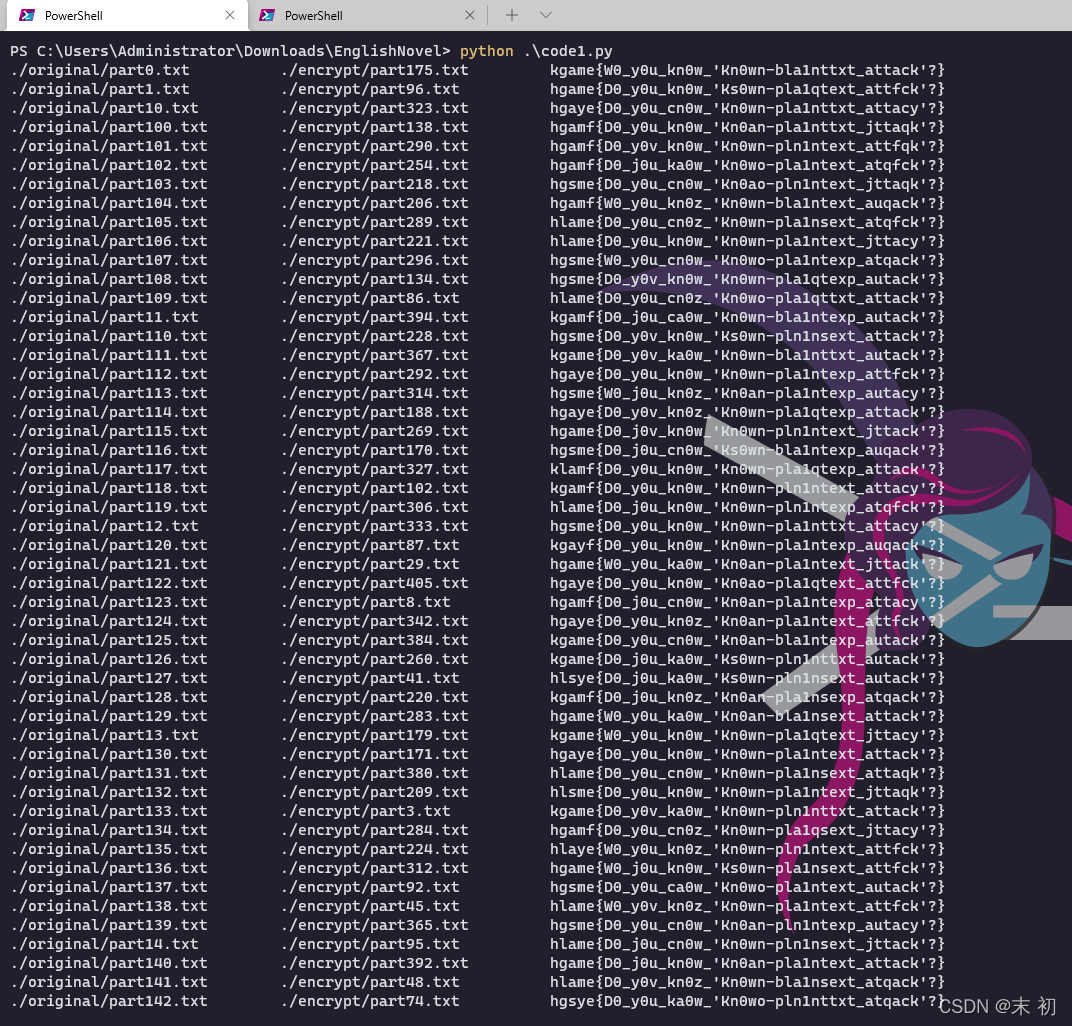
hgame{D0_y0u_kn0w_'Kn0wn-pla1ntext_attack'?}
版权归原作者 末 初 所有, 如有侵权,请联系我们删除。