Description
The remote host supports the use of SSL ciphers that offer medium strength encryption. Nessus regards medium strength as any encryption that uses key lengths at least 64 bits and less than 112 bits, or else that uses the 3DES encryption suite.
远程主机支持使用提供中等强度加密的SSL密码。 Nessus认为中等强度是指使用密钥长度至少64位且小于112位的加密,或者使用3DES加密套件的加密。
Note that it is considerably easier to circumvent medium strength encryption if the attacker is on the same physical network.
请注意,如果攻击者位于同一物理网络上,那么要规避中等强度的加密要容易得多。
Solution
Reconfigure the affected application if possible to avoid use of medium strength ciphers.
如果可能,请重新配置受影响的应用程序,以避免使用中等强度的密码。
该漏洞影响了很多的服务,包括常见的3389,80,443,25等。基于windows,修复方法整理如下:
Run-gpedit.msc-computer configuration-administrtive templates-network-SSL Configuration Settings-SSL Cipher Suite Order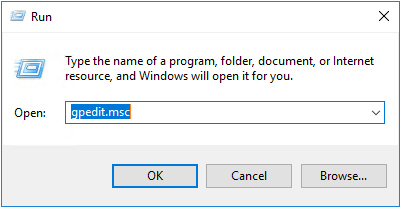
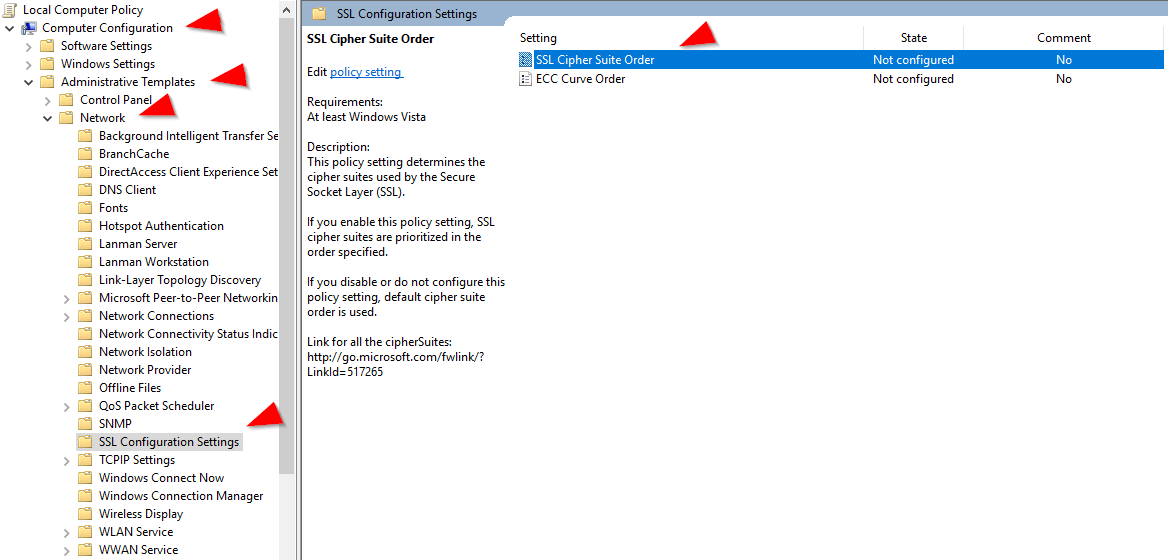
在SSL Cipher Suite Order中Enabled,并用下面的列表替换原来的列表。
替换列表:
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384_P256, TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384_P384, TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256_P256, TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256_P384, TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA_P256, TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA_P384, TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA_P256, TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA_P384, TLS_DHE_RSA_WITH_AES_256_GCM_SHA384, TLS_DHE_RSA_WITH_AES_128_GCM_SHA256, TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384_P384, TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256_P256, TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256_P384, TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384_P384, TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256_P256, TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256_P384, TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA_P256, TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA_P384, TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA_P256, TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA_P384, TLS_DHE_DSS_WITH_AES_256_CBC_SHA256, TLS_DHE_DSS_WITH_AES_128_CBC_SHA256, TLS_DHE_DSS_WITH_AES_256_CBC_SHA, TLS_DHE_DSS_WITH_AES_128_CBC_SHA, TLS_DHE_DSS_WITH_3DES_EDE_CBC_SHA
以上就是SSL Medium Strength Cipher Suites Supported (SWEET32) 漏洞修复方法了。希望对大家有帮助吧。
版权归原作者 Par@ish 所有, 如有侵权,请联系我们删除。